-
Young woman using jade roller at home
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
The concept of credit card theft. Hackers with credit cards on laptops use these data for unauthorized shopping. Unauthorized payments from credit card owners. In the hacker's secret office
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Creative code skull sketch on modern laptop monitor, theft of personal data and malware concept. 3D Rendering
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Back rear view photo of coder developing new security system to protect digital data base from being hacked using laptop as an additional work device
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Black and white line icons of shield and lock with circuit board elements for cybersecurity and finance concepts
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Cyber security technology for business and internet project with lock image
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
źrebak konia arabskiego z klaczą
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Falling binary code matrix background. Digital stream of zeros and ones for data, cybersecurity, and technology concept.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Cyber security concept Global network security technology, Women protect personal information. Encryption with a padlock icon on a futuristic virtual interface screen
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
A natural mineral made of jade on a white background. A sample of green stone
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Matrix background. Cyber security with binary code. Rapidly falling randomly green numbers. Decoding algorithms hacked software. Big data visualization.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Stadnina koni / Kaszuby / pomorskie / Polska
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Quick tips badge. Vector illustration
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Cybercrime concepts The hacker's hand is holding a credit card with a blurry computer background. Stolen data and use it for payments and shopping on laptop.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Jade Dragon Snow Mountain
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Green gemstone natural mineral fluoride or green beryl isolated
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Abstract virtual code skull hologram on modern architecture background, cybercrime and hacking concept. Multiexposure
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Lock icon. Flat vector illustration in black. EPS 10
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Hacker icon vector. Simple flat symbol. editable strokes
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Cyber security concept showing low poly hacker figure in front of streaming binary code backdrop, illustrating digital fraud, hacking activity and online threats in dark 3D style..eps
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Blue shield with white lock icon.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Black and White Glitch Noise Texture Vector with Broken Transmission Effect and Distorted Screen Pixel Overlay Design.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Digital Security Shield with Data Flow and Growth Charts.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Collection of Digital Security Shields with Cryptographic Symbols.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
cyber security concept, Login, User, identification information security and encryption, secure Internet access, cybersecurity, secure access to user's personal information,
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Zero Day Outline White Icon Set Design
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Lock icon graphic element for project and web designs
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Collection of various green precious gemstones on white background emeralds and jade stones
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Green jade chess king piece polished smooth, isolated on transparent background
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Hacker icon symbol. Flat Vector illustration set
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Cybersecurity and digital threat icon featuring robotic skull with circuit board patterns and signal waves for computer virus malware and network security vulnerability warning concept on white
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
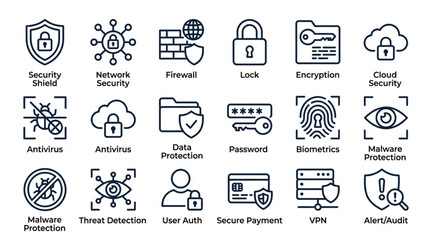
Cybersecurity Icons Representing Digital Safety and Protection.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Digital Ghost Icon Representing Cyber Security Threat.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Gua sha scrap icon, symbol of facial massage, skincare, lymphatic drainage, rejuvenation and spa treatment, vector icon in two styles: glyph and outline.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
outline cyber icons set - hack, woman online, dos attack. editable vector for web and mobile ui
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Minimalist flat black padlock icons illustrating secure and open access states for digital privacy on white background.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Cybersecurity data protection business privacy concept. Padlock on a futuristic digital circuit background. Protection mechanism and system privacy. Technology vector illustration.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Email phishing icon lineart style, silhouette flat icons
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Lock icon, outline style icon for web. vector graphics
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Cyber Security Data Protection
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Digital shield protecting network data from cyber threats and unauthorized access
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Pixel Bitmap Texture Pattern with Abstract Geometric Retro Design Vector Illustration.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Hacker icon collection. Vector icon illustrated
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Cyber Forensics Icons Set Illustrating Digital Investigation Tools and Concepts.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Set of hand-drawn cybersecurity and computer error icons. Includes warning shield, open padlock, browser alert, data analysis magnifying glass, and a worried user doodle. Black ink sketch style.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Firewall Breach Outline White Icon Set Design
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Broken padlock with star keyhole vector icon
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
A collection of black security and privacy related icons displayed in a row
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Vertical scanline glitch overlay with VHS-style screen lines and TV static interference pattern. Retro CRT monitor noise texture on white background. Motion-blurred speed stripes for video transition
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Green Matcha Powder in White Ceramic Bowl with Fresh Tea Leaves
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Set of twenty cyber security and safety protection shield icons with different symbols
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Mint green crumpled paper background with subtle creases and wavy texture background crumpled
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Elegant green marble stage or studio background featuring soft dappled leaf shadows. Ideal for product displays cosmetic mockups and nature-inspired digital backdrops
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Abstract blurred gradient mesh background in green.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
cyber hack icons minimalist flat style design, cyber hack Vector illustration on white background
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Abstract digital data binary code diagonal on blue background with light effect.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Digital black pixel pattern background with glowing squares - cyber grid for game interface, tech wallpaper, streaming overlay and futuristic design project with neon mosaic texture on dark surface.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Glitch background. VHS grunge texture with noise effect and pixelation. Analog video digital errors. Retro pixel backdrop.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Virus Code Flow Red Binary Code Bug Cyber Attack Pattern. Malware Attack Ransomware Warning Background. Computer Hacking Cyber Security Breach. AI Data Phishing Digital Fraud BG. Vector Illustration
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Cybersecurity Concept: Digital Lock, Server, Firewall, Data Protection
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Lock icon pack for web and apps design projects
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Abstract Bitmap Retro Texture with Pixelated Geometric Pattern Vector Illustration.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Horizontal scanlines glitch effect overlay, VHS screen lines, TV static interference pattern. Retro CRT monitor noise texture isolated on white. Motion blur speed stripes for video transition effects.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Cyber Security Concept Vector Illustration with Digital Shield and Data Protection Network
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Cybersecurity Castle: Data Protection, Network Security, Virus Attack
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Cyber warfare line icon set, firewall global network encryption cyberdefense cyber warrior cyber shield network attack.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Email phishing icon element for design projects and web designs
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Abstract white, teal, dark jade texture paper background, wavy layers. Wave pattern with copy space for banner
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Hacker icon or symbol set
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Lock icon graphic element for project and web designs
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Digital Padlock on abstract technology background, Technology security concept. Modern safety digital background. Protection system, Cyber Security and safety information, personal data concept
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Facial Roller Set, Jade Stone Massager Tools, Gua Sha Beauty Equipment, Skincare Accessories
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Phishing icon set. Editable stroke. Contain icons related to phishing, scam, thief, cybercrime, password hacking, money theft, data leakage, and more.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
cyber hack icons minimalist flat style design, cyber hack Vector illustration on white background
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Illustration of skincare serum, cream and jade roller.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Minimalist red data stream glitch effect on white background for technology and cybersecurity concepts
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Glitch background. VHS grunge texture with noise effect and pixelation. Analog video digital errors. Retro pixel backdrop.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Password phishing icon in trendy line style. icon illustrations
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Emerald green marble texture background, luxury stone surface with natural veins, elegant dark and light teal mineral patterns for interior design
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Succulent and Cactus Houseplant Collection Featuring Aloe Vera, Echeveria, Jade Plant, String of Pearls, and Modern Potted Vector Designs
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Black and White Glitch Noise Texture Vector with Broken Transmission Effect and Distorted Screen Pixel Overlay Design.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Horizontal scanlines glitch effect overlay, VHS screen lines, TV static interference pattern. Retro CRT monitor noise texture isolated on white. Motion blur speed stripes for video transition effects.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Scanlines Glitch Effect Overlay with VHS CRT Noise Texture Isolated on Transparent Background, transition effects, texture overlay, print texture overlay, display glitch error.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Protect Your Privacy: Safe Online, Secure Always. Your data is valuable, keep it private.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Hacker icon Flat Solid Style in black and white colors. Vector eps10.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Global cyber security illustration with earth globe protected by shield and padlock over binary data stream security cybersecurity protection internet information
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Collection of Cybersecurity Icons Representing Digital Security Concepts.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Virus White Icon Set Design
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Gua Sha Stone Icons, Heart Shape Beauty Tool Vector Set, Facial Massage Therapy Elements
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Cybersecurity concept with shield and data flow.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Polished green jade dollar sign symbol, isolated on transparent background
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Spam Phishing Email Magnet Icon.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
2d illustration abstract technology background
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Green jade bust of a Roman emperor, isolated on transparent background
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Digital Lock with Binary Code.
Do ulubionych favorite_border
Usuń z ulubionych favorite