-
Close up of the pattern and color of the surface of a raw jade stone
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Green jade gems on gold bracelet fashion wear
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Real jade is green jade for making jewelry.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Jade tree in cement pot, close-up view, space for text
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Nephrite (jade, axestone)
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Bored Teenage Girl Being Told Off By Mother
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
after boiled. soaked in ice water and cut the potato skin. make it easily pull the skin off, quick way to peel potatoes, kitchen hack
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Crassula ovata. Close up of flowers on a jade plant crassula ovata
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Data security technology blue background, Ai big data secure, crime hack digital tech, abstract privacy hi tech binary code, virus attack data, internet network connection theft, illustration vector
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Server hacking illustration concept, server security website template, illustration of hacker attacking database
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Woman in spa having jade roller facial treatment
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Beautiful jade stone with dragon carved
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
AI monitors network to issue real-time alerts for cybersecurity incidents. Alert warning showing red cyber for data breach, network threat, emphasis on security risk, caution, digital protection Vouch
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Ransomware Cyber Attack Showing Personal Files Encrypted
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Red pirate skull on smartphone screen, mobile hacking, system breach, virus
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
jade bracelet on white background
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
The flower called the dragon claw in Guatemala. Strongylodon Macrobotrys.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Jade Dragon Snow Mountain in Lijiang, China
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
abstract green marble surface texture background
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Pink roller face massager and gouache scraper . Rose quartz jade roller on a white background. Anti age, lifting and toning treatment at home. Copy space.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Gardener holding jade tree branch with roots for replanting
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Illustration of hacker activities phishing scam and hack data. Fishing hook with email envelope icon. Flat design vector
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Ombre gradient. Navy Blue atoll color. Noise grain rough grungy. Matte shimmer metallic. Black dark, foil shimmer texture light jade petrol Navy blue. Modern plain mesh vector illustration ...
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Mountain landscape in Jade Dragon Snow Mountain (Yulong Snow Mountain) located at Lijiang, Yunnan, China.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Hacking icon set in linear style. It contains symbols to hacker, fraud, cyber, security, hack and more. Security icon set. Outline symbol collection. Editable stroke. Vector collection.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Matrix of random numbers. Flying numbers. Binary computer code. Abstract digital background. 3d rendering.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Real jade Natural sparkling green color
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Woman doing machine hack squat exercise. Flat vector
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
jade plant seamless pattern
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
HUD Warning Spam Interface Vector with Alert Display Screen UI and Critical Danger Alarm Caution.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
abstract green marble surface texture background
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Beautiful young african woman making face massage with jade roller
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Marble ink abstract art from exquisite original painting for abstract background . Painting was painted on high quality paper texture to create smooth marble background pattern of ombre alcohol ink .
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
High-spirited lady with a jade roller looking forward
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Shocked young man looking at smartphone
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Transparent Background jade Illustration Png. Transparent Clipart Image of watercolor green crystal ready-to-use for site, article, print. Heart chakra stone, healing crystal
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
hacksaw tool icon silhouette vector art illustration
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Antivirus system protection icon Vector logo outline
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
abstract green marble surface texture background
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
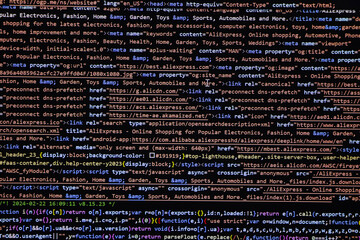
Programming code abstract screen of software developer. Computer script
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
VPN hack concept with faceless hooded male person
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Night, man or frustrated by laptop or error for project deadline mistake, 404 or phishing website. Anxiety, hacked or security engineer with stress for financial crisis, digital fraud or online scam
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Beautiful european woman uses jade roller to massage her face
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
crassula jade plant in a white pot
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
potted crassula ovata, jade tree plant, close up
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Login page to unlock a password to hack information for the website. digital crime prevention by anonymous hackers. Cyber crime personal secure concept with login icon
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Hacker security cyber attack smartphone. Digital mobile phone isolated on black. Internet web hack technology. Login and password, cybersecurity banner concept.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Virus malware detected concept, viruses attack warning signs, hacking alert messages vector
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
polished Nephrite (green jade) gemstone isolated
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Ransomware malware wannacry risk symbol hacker cyber attack concept computer virus infection infographic. Vector online hacker risk illustration
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Life hacks written on lightbox in office as flatlay
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Abstract technology background. Lines texture. Motion dots. Black backdrop. Futuristic wallpaper. Blue and violet color.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
white flower jade plant flower
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Developer man hand using laptop with triangle caution malware warning icon hologram. Scam virus spyware malware antivirus concept, cybersecurity, cyber crime, hack password
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Ancient jade carving of terra-cotta
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Global networking and connection
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
konie arabskie w janowie podlaskim
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Gardener preparing jade tree cuttings for propagation
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Crassula ovata (Jade Plant,Money Plant,Friendship Tree) succulent plant in a tropical garden.Selective focus.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
A male hacker is using a computer to hack data to demand ransom from victims.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Abstract Elegant dark green background with mottled vintage texture in old fancy background design, texture of colored parchment paper.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Closeup surface art tone abstract marble pattern at colorful marble stone wall texture background
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Attention Danger Symbol on Dark Red Glitched Background. Computer Virus. System Hacked Error Sign. Malware, Ransomware, Data Breach Concept. Vector Illustration.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Cybercrime Multiple Style Icon Set Collection.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
jade mineral characterized by its predominantly white coloration.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Binary code on flag of Korea North. Program source code or Hacker concept on North Korean flag. North Korea digital technology security, hacking or programming
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Massage set "Guasha" jade green, roller and scraper on the white background
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Jade roller and gua sha massager with cream and serum bottles at pastel background. Long banner format.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Happy millennial black woman making face massage with jade roller
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Woman in athletic shape performing hack squats in busy modern gym, working on leg strength, balance, and overall lower body conditioning. Fitness and weight training for women concept
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Young woman with dark long hair moving jade stone roller on her face during massage procedure while sitting on bed in the morning
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
theft and ciphering of data from servers using ransomware, server security breach warning, 3d rendering
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Illustration of succulent. Decorative home plant. Natural image.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Processor Virus Infection
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Jade Tree, Concrete Potted Succulent Plant, Space for Text
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Macro stone Nephrite mineral on black background
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Security icons set isolated on white background. Cybersecurity icons set for digital protection and data security concepts. A collection of flat design icons representing cybersecurity elements
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
dwa białe konie biegnące galopem po plaży
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Abstract Elegant dark green background with mottled vintage texture in old fancy background design, texture of colored parchment paper.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Hacker Solid Editable Icons set. Vector illustration in modern thin solid style of hacker icons: hacker, fraud, phishing, etc
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Abstract Technology Machine Code Background. Random Binary Hexadecimal Code. Matrix with Digits. Vector Illustration. Hacking, Cryptography, Malware, Reverse Engineering, Data Analysis Backdrop.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Password computer forget many access account account hacked
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Business concept, enterprise system alert, display alert data in database and system, prevent business data damage problem.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Programming coding screen, web developer coding screen
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Lijiang Jade dragon snow mountain of Yunnan, China
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Green jade bevel extrude 3d style isolated letters
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Concept of cyber security or private key, abstract digital key in technology background with internet icons, Security Concept background
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Darkweb, darknet and hacking concept. Hacker with cellphone. Man using dark web with smartphone. Mobile phone fraud, online scam and cyber security threat. Scammer using stolen cell. AR data code.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Computer screen over server room background. Concept of Hacker Attack, Virus Infected Software, Dark Web and Cyber Security.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Cyber Crime Concept, Phishing Scam Application on Mobile Phone Screen Communication Messages, Vector Flat Illustration
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Cute young women smiling at camera, using jade roller and facial gua sha while posing together isolated over beige background
Do ulubionych favorite_border
Usuń z ulubionych favorite