-
Binary code background texture with sparkles. Deepth feeling with nodes. Cyber security.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Skin care concept with face roller on gray textured table
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Beautiful variegated jade plant in a greenhouse. The leaves vibrant mix of yellow green hues. Cactus adding to the greenhouse atmosphere. It highlights the beauty of cultivated botanical specimens
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
jade from Russia isolated on white background
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Web banner with phrase Hacked. Concept of cyber attack, hacking, malware or spyware
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Jade plant growing in white cup on white wooden background. Succulent houseplant, crassula ovata, commonly known as jade plant, friendship tree, lucky plant or money tree
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Bitcoin gold coin digital currency close up
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
horse Arab gallop stud dynamics
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Phone security concept. Smartphone locked with chain and padlock on yellow background. Mobile security and data privacy
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Red hair young girl doing beauty routine with gua sha quartz roller at home. Redhead beautiful woman using facial massage natural stone in bedroom. Beauty routine and skincare concept.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
view of Spekboom (Portulacaria afra) plant bonsai in flower pot, known as elephant bush, dwarf jade plant and porkbush.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Concept of cyber crime, hand using laptop and show malware screen that comes with email, hack password and personal data. hackers, Viruses, Worms, Trojans, Ransomware, Spyware, Adware, Botnets
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Dangerous hooded hacker in his hideout place which has a dark atmosphere, multiple displays
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Gua sha stone, jade roller, clear perfume, white glass eye dropper serum bottle / still life arranged with green wildflowers and isolated on white surface / natural clean beauty concept
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
X Danger Symbol on Dark Red Glitched Background. Computer Virus. System Hacked Error Sign. Malware, Ransomware, Data Breach Concept. Vector Illustration.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Cyber attack security network protection business technology concept. Safe online data UI authorized universal access illustration background.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Code Injection Hacks in Web Applications. Code-injection attacks manipulate specific system variables. opportunity for hackers to access sensitive information. 3D render
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Close-up of two raw jade mineral stones, isolated on white background
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Konie na pastwisku w pięknym świetle zachodzącego słońca
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Nephrite (Jadeite, Axestone)
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Green Jade Comb With Traditional Carved Bat Design
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Male hacker trying to break into government network, coding computer virus on database late at night. Young spy planning data breach to hack computer system, stealing sensitive information.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Two jade carvings of chinese brush holders
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Abstract digital background with ones and zeros. Vector graphic pattern with binary code. vector eps 10
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Digital Security Concept with Email Alerts and Cyber Risk Icons Displayed on Tablet, Representing Modern Technology and Data Protection in Business Environment Sigmoid
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Deep Forest Green Abstract Backdrop. Dark Green Texture Background.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Futuristic green digital matrix space with binary code streams and glowing horizon line, symbolizing data transfer, cybersecurity, virtual networks, artificial intelligence vector background
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
hacking server icon set multi concept
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Security icons for network protection.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Businessman holding magnifying glass detected online phishing scam hooked on computer screen. Scam alert on cyber crime on SMS fraud link, credit card, password hacking and fake message. Vector.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Lock icon. vector graphics pack.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Smooth polished ivory jade bi disc pendant with cord, isolated on transparent background
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
AI Vulnerability and Manipulation Risks Concept Illustration Showing a Humanoid Robot Exposed to Prompt Attacks
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Collection of beauty and wellness tools for skincare.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Phishing Email Icon with Skull, Cyber Attack and Online Scam Warning Illustration
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Phishing icon set. Contain icons related to phishing, scam, thief, cybercrime, password hacking, money theft, data leakage, and more. Editable stroke. Vector illustration
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Scam alert notification set icon. fraud notice alert. malware hack attack atention banner pop up. vector
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Lock icon line and flat vector collection for ui, ux designs
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Blue crystal cluster gemstone mineral.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Vertical scanlines glitch effect overlay, VHS screen lines, TV static interference pattern. Retro CRT monitor noise texture isolated on white. Motion blur speed stripes for video transition effects.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Business concept, enterprise system alert, display alert data in database and system, prevent business data damage problem.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Collection of eight unique line art succulent and cactus illustrations isolated on a white background
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Minimal jade roller tool dual roller ends elegant design for skincare massage Vector illustration
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
3D illustrastion - Data Matrix Warning Sign System Hacked
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Green marble stone surface. Luxury jade texture for product display.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Hacker icons in trendy linear style vector. Vector illustration
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Virus warning alert on computer screen detected modish cyber threat , hacker, computer virus and malware
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
A stream of binary matrix code on the screen. numbers of the computer matrix. The concept of coding, hacker or mining of crypto-currency bitcoin. Vector illustration.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Cyber security safety online data protection Set of flat design vector illustration concepts for online security and data protection.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Phishing Icon Set - Fishing Hook in Chat Bubble for Cyber Security Alert
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Lock icon. vector graphics pack.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Auspicious Chinese cloud icon pack, traditional curling cloud motifs, Asian cultural decorative elements, elegant ornamental festival patterns, classic cloud art graphics
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Black and white line icons of shield and lock with circuit board elements for cybersecurity and finance concepts
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Technology stream binary code. Digital illustration. White matrix background. Programming, coding, hacking and encryption.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Coding vector line icon set. Coding icon set in linear style. Pictograms of development, software, programming, program, website, web and more. Editable stroke.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Digital Security Shield with Data Flow and Growth Charts.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
System Hacked Error Dark Red Glitched Background. Digital Scam, Fraud, Computer Virus, Malware, Ransomware, Data Breach Concept. Vector Illustration.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Hacker icon vector clipart in black colors. suitable for graphic work
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
A man holding smartphone with hacking scam warning and fake bank support message, phishing, online fraud, cybersecurity awareness, call center scammer, identity theft, online security threats.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Abstract digital background with ones and zeros. Vector graphic pattern with binary code. vector eps 10
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Solid black silhouette of a skincare jade roller dual roller beauty tool Vector illustration
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Phishing icon set. Editable stroke. Contain icons related to phishing, scam, thief, cybercrime, password hacking, money theft, data leakage, and more.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Cybersecurity icons collection digital security and data protection concepts.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
AI Line Data Network Technology Background, Abstract Dynamic Effect Stream, Energy Flow. Digital Transformation Tech, Artificial Intelligence Blue BG, Business Transform Concept. Vector Illustration
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Email security system identifies phishing attempts, detects suspicious messages, and protects users from data theft and malware through intelligent monitoring and alerts. Parse
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Phone Scammers, mysterious man with phone, cyber theft and fraud, mobile phone used for hacking, secret attacks on privacy.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Dark green abstract fog background texture for mysterious designs.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Purple abstract pixel texture bg video screen. Tv pattern background with square noise effect. Futuristic broadcast neon gradient banner for television. Modern vhs led static display element
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Horizontal scanlines glitch effect overlay, VHS screen lines, TV static interference pattern. Retro CRT monitor noise texture isolated on white. Motion blur speed stripes for video transition effects.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Shield Protecting Against Cyber Threats.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Cyber security icons set for websites and applications on white background, digital protection and network safety symbols.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Portulacaria afra variegata succulent plant grow in botanical garden
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Digital Security Padlock Icon Represents Data Protection.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Security icons and symbols collection.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Futuristic binary matrix code background with copy space for information. Vector illustration.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Cybersecurity concept with shield and data flow.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Cyber Security Network Protection Shield Server Data.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
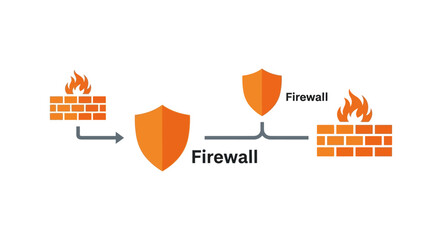
Firewall network security protection concept.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
outline cyber icons set - hack, woman online, dos attack. editable vector for web and mobile ui
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Cybersecurity Hacker technology and cyber threats with computers and digital globe in front, showing cyber theft, virus attacks and data extortion over a global high-speed internet network.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Portulacaria afra, commonly known as elephant bush, spekboom, or dwarf jade plant, is a succulent shrub native to South Africa, valued for its hardiness, carbon absorption, and ornamental appeal.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
A dark blue silhouette of a person with an unlocked padlock symbol on their chest
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Team of cybercriminals fixing computer system cyberattack, using trojan virus to hack server. Diverse thieves programming app, cybersecurity technology, database spyware protection.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Digital Network Security Shield Protecting Servers Data.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Personal data breach and cybersecurity concept. Broken padlock protecting human figure is attacked, held by a man. Identity theft protection, web scam, information leak, warning alert, and hacker hack
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Mature man massaging face with jade roller in bathroom
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Suspicious Email Link Detected, Cybersecurity Warning, digital warning interface, phishing email and a suspicious link detection alert. Concept for cybersecurity, email threats, phishing prevention
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Cybersecurity concept showing login attempts and security threats.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Hackathon icon set Aqua Orange Flat concept for design sprint-like social coding event with icon of brainstorm, development, programming, timing, speed, teamwork, and goal
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Padlock on protection shield with wireframe sphere on a white background. Cybersecurity and data network protection concept. Secure technology and personal data security. Vector illustration.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
System Hack Icon Set Multiple Style Collection
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Horizontal scanlines glitch effect overlay, VHS screen lines, TV static interference pattern. Retro CRT monitor noise texture isolated on white. Motion blur speed stripes for video transition effects.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Cyber lock background and technology web services for business and internet project.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Illustration of skincare serum, cream and jade roller.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Cybersecurity Icons Representing Digital Safety and Protection.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Cyber security shield with lock.
Do ulubionych favorite_border
Usuń z ulubionych favorite