-
Abstract fluid art background with dark emerald green marble texture. Liquid acrylic painting backdrop with gradient
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
A hooded figure hacks a computer surrounded by dollar signs
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
jade roller, skincare tool vector.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Hacker wearing mask and hood to hack computer system, breaking into company servers to steal big data. Masked man looking dangerous and scary, impostor creating security malware.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Green Matcha Powder in White Ceramic Bowl with Fresh Tea Leaves
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Cyber Deception Icons Illustrating Security Threats and Strategies.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Email phishing icon set. Black vector symbols
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Cyber lock background and technology web services for business and internet project.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Purple abstract pixel texture bg video screen. Tv pattern background with square noise effect. Futuristic broadcast neon gradient banner for television. Modern vhs led static display element. Eps10
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Personal data breach and cybersecurity concept. Broken padlock protecting human figure is attacked, held by a man using tablet. Identity theft protection, web scam, information leak, exposed, or hack
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Cybersecurity Icons Representing Digital Security Concepts.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Cybersecurity Icons Representing Digital Safety and Protection.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Green jade chess king piece polished smooth, isolated on transparent background
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Suspicious Individual Wearing Balaclava Hacks Into Smartphone PIN
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Cyber security shield with lock.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
TV Glitch Texture. Abstract VHS Noise Background. Screen Interference Pattern for Retro Video Overlay.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
hardware outline icon set featuring handheld console, phishing, sound card, cyber security icons.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Digital Network Security Shield Protecting Servers Data.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Ransomware concept. Illustration of office man in panic because his device got hacked and his files were encrypted. Cybercrime attack flat vector isolated on white background
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Computer Hacker in Hoodie. Obscured Dark Face. Concept of Hacker Attack, Virus Infected Software, Dark Web and Cyber Security.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Hacker using the Internet hacked abstract computer server, database, network storage, firewall, social network account, theft of data
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Encryption specialist looking at alert message to hack system, trying to break into computer server and database. Male thief planting trojan virus to create malware, hacking network.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Abstract blue background from jade surface.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Text effect jade green glossy
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Surprised woman points finger up as she finds amazing idea online. Happy lady in curlers and face mask sitting on sofa, browsing Internet blog on laptop and learning good life hacks and practical tips
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
PC security concept. Secure connection, privacy and protection. Traffic Encryption, VPN. Bunch of keys to open the padlock and get access to hack privacy, activities and user data. Illustration
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Life Hacks Blue Lines Blob Rounded Square Black Background Text
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Binary Code backgrounds, a sequence of zero and one number on a blue background. Numbers of the computer matrix. The concept of coding and cybersecurity
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Fluid Art. Liquid Velvet Jade green abstract drips and wave. Marble effect background or texture
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Mid autumn festival greeting card, invitation with jade rabbit, moon silhouette, chrysanthemum flowers and ornamental clouds.Vector illustration background with Asian pattern.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Elegant green background texture, old vintage grunge design, green Christmas background, St Patrick’s day color, textured paper backgrounds
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
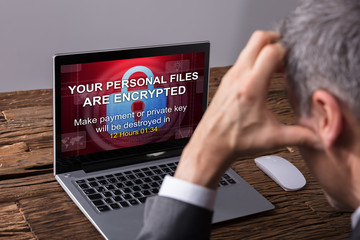
Looking At Laptop Screen Showing Personal Files Encrypted Text
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
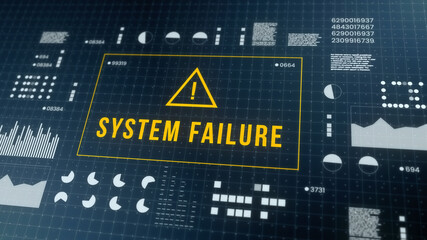
Abstract Modern tech of Programming code screen with Warning alert of System hacked. Virus, Malware, Cyber attack, and Internet cyber security Concept. 3D illustration.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Mint, grey, and gold stone marble texture. Alcohol ink technique abstract vector background. Modern paint in natural colors with glitter. Template for banner, poster design. Fluid art painting
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
A diverse group of professionals collaborates to address cybersecurity risks, analyzing data and discussing warning signs in a modern office environment, promoting teamwork. Raster
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Cyber World icon set. Contains related to digital, web, network, website, security and more. Cyberspace simple icon. UI icons set in a thin style. Pixel perfect. Editable stroke.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Web browser window with virus detection alert on laptop screen. Internet threat warning. Concept of malware, ransomware, hacking, or cybercrime. Dangerous website. Flat technology vector illustration.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
jade vine rarest plant in the world
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Face lift anti-aging treatment with jade roller. Woman with perfect skin of her face after massage.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Male hacker trying to break into government network, coding computer virus on database late at night. Young spy planning data breach to hack computer system, stealing sensitive information.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Programming Coding modern icon set. Contains such icons as development, web, coding, develop, program and more. Program modern icon set. Minimalist icons collection. Editable vector illustration.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Hand holding a saw with a black handle isolated on white background
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Stones for massage and recovery of health. Yellow jade on the massage table column.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Interior View With Statues Of Jade Emperor Pagoda In District 1 Of Ho Chi Minh City, Vietnam. This Pagoda Was Built In 1892 By Chinese And Very Famous In Ho Chi Minh City.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Password hacking ransomwares technology security illustration
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Abstract binary code background. Artificial intelligence, big data and digital technology concept. 3D render illustration.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Fluid Art. Liquid dark turquoise abstract drips and wave. Marble effect background or texture
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
A stream of binary matrix code on the screen. numbers of the computer matrix.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Green marble, jade stone textured
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Phishing scam concept with smartphone and credit card on hook. 3D Rendering
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Gua Sha massager isolated from background, green jade stone for face and body care.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
System failure security fail computer breakdown hacking warning message hacked alert. Cyber attack network fail. Digital illustration.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
cyber crime phishing mail , security awareness to protect important data hacking
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Luxury marbling background vector. Emerald green marble design with golden texture.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Modern glitch transition with hacked and skull
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Jade Plant with Dense Succulent Green Leaves in Hanging Basket
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Frustrated hacker in secret hideout dejected after failing to attack victims using malware. Annoyed scammer feeling upset after being unable to hack computer systems, camera B
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Fingerprint scanning concept
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Natural jade face roller and ice cubes on grey background, closeup
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
collage of woman with towel on head using jade roller and gua sha on face isolated on grey
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Haking into crypto world . Mixed media
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Life hack written on tablet in office as flatlay
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Quick tips badge. Vector illustration
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Chinese jade bracelet features
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Cyberattack trolling and broadcast on screen 3d illustration
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Glitch noise static television VFX. Visual video effects stripes background, CRT tv screen no signal glitch effect
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Protection network security computer and safe your data concept, Businessman holding shield protect icon. lock symbol, concept about security, cybersecurity and protection against dangers
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Skin care tools background.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Data phishing hacking online. Scam envelope concept. Computer data fishing hack crime
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Hacker Man holding an smartcar concept 3d rendering
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Annoyed woman drilling into her boyfriend's head
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Glitched silhouette, bitmap effect, error signal, technical problem. Hacked system or cyber attack. Vector illustration.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Illustration concept of data stealing from the computer.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Hooded cybercriminal uses laptop to hack internet in cyberspace, black background, internet personal data security concept. Hacker on a black background with space for text
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Zaprzęgi konne na drodze do Morskiego Oka w Tatrach,
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Abstract Red Binary Software Programming Code Background. Malicious Hack Malware Ransomware Concept. Data Leak Breach. Random Binary Data Matrix Wide Vector Illustration.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Blue Moon Valley showing waterfall, clear blue lake and stunning mountain backdrop of Jade Dragon Snow Mountain, Lijiang, China
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Real jade That is the original jade ball Green and rare, expensive
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
warning signs to be aware of the dangers of being hacked by hackers,Internet malware viruses are destroying computer data.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Frustrated Businesswoman Looking At Her Computer Screen
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Vector set of realistic isolated red rubber stamp of Hacked logo for template decoration on the transparent background.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Cables plugged into a box
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
konie - klacz i źrebak na łące
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
cyber crime phishing mail , security awareness training to protect important business data hacking
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
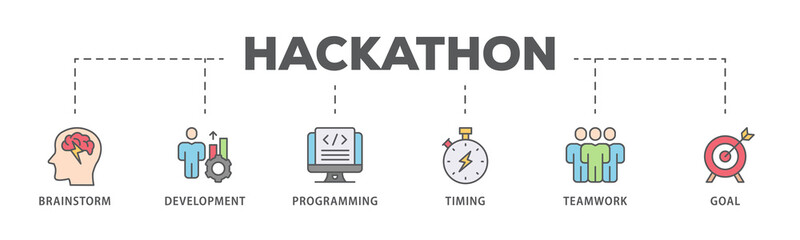
Hackathon banner web icon illustration concept for design sprint-like social coding event with icon of brainstorm, development, programming, timing, speed, teamwork, and goal
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Vector isolated cartoon illustration of home potted succulent jade bonsai plant.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Nice green jade neocaridina shrimp in freshwater aquarium pets
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Hacking and cryptocurrency concept
Do ulubionych favorite_border
Usuń z ulubionych favorite