-
code and keyboard blue background ethical hacking concept
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Digital blue background. Information code. Binary computer code. 3d rendering
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Hacker on the phone screen with a folder infected with a Trojan. From the folder, connections go to the messenger application which are hacked and taken over. Flat design vector illustartion.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Network security system. Personal Data information on Tablet.Information and cyber security Technology Services. Internet Technology.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Hacker using keyboard on dark background
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Girl hacker in a hoodie using a laptop. Abstract digital polygonal hack woman in blue on technology dark background. Cybersecurity or cyber attack concept. Computer scam. Low poly vector illustration
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Landscape View of Yushan Main Peak And Tongpu Valley From the North Peak of Jade Mountain At Sunrise, Yushan National Park, Chiayi Taiwan
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Tea Bag Aroma Life Hack For Smelly Shoes
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Macro stone Nephrite mineral on white background
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Nagging wife complains to her husband
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Life Hacks. Computer keyboard and a coffee mug on a white table
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
klacz konia arabskiego na zbliżeniu
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Hands operating a laptop with a vigilant eye on a hacker's silhouette in the background, illustrating the battle against cyberattacks. Hacker Defense
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Cybersecurity cybercrime internet scam, online business secure payment, Cyber security platform VPN computer privacy protection data hacking malware virus attack defense, network system hacked warning
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Hacker security cyber attack smartphone. Digital mobile phone isolated on black. Internet web hack technology. Login and password, cybersecurity banner concept.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Green emerald marble seamless glitter texture background, counter top view of tile stone floor in natural pattern.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
stop theft. thief inside stop icon. business metaphor for stop cyber criminal movement vector illustration
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
hacking US election America democracy
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
virus bot robot hacker danger piracy error background pirate attack artificial intelligence concept flat horizontal banner copy space vector illustration
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
pirate sits with laptop at desk - vector illustration
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Danger sign. Hacked system or cyber attack. Vector illustration.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Computer Hacker in Hoodie. Obscured Dark Face. Concept of Hacker Attack, Virus Infected Software, Dark Web and Cyber Security.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
hacker doing a crypto scam or phishing
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Woman holding semiprecious stones in her hand on dark grey background
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
pop style graphic image of hacker on a red background
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Antique of Jade statue on white background.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Data theft. Malware. Virus stealing information. Cyber attacker trying to hack computer.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
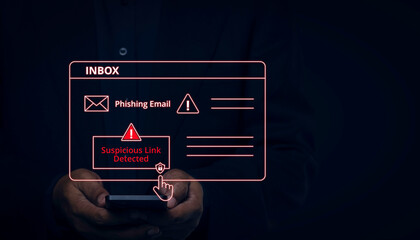
Suspicious Email Link Detected, Cybersecurity Warning, digital warning interface, phishing email and a suspicious link detection alert. Concept for cybersecurity, email threats, phishing prevention
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
green stone jade crystal texture abstract nature wallpaper decorate background
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Selective focus on male athletes hand holding onto hack squat machine handle
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
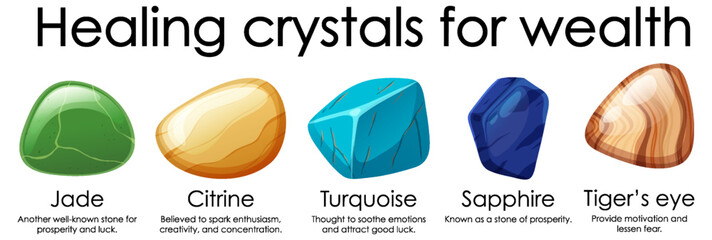
Healing crystals for wealth collection
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Jade Editable Vector Text Effect.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Set of different colored crystals, geometric mineral stones. Collection of gemstones isolated on a plain background vector illustration.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Phishing or hacking attack concept. Fake login screen to hack username, password. Cyber security, steal personal information. 3D laptop with fake login screen
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
malware detection , virus monitoring , security assessment
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Green white marble wall surface gray pattern graphic abstract light elegant for do floor plan ceramic counter texture tile silver background.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Hacking hunting for crypto currency
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
dwa brązowe konie na pastwisku
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Hacker laptop icon. Simple illustration of hacker laptop vector icon for web design Vector Black silhouettes. with white background
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Beautiful dark green viridian vintage color trends feather texture background
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
greenstone industrial jewelery
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Facial beauty treatment with jade rollers.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Celadon ceramic dishes , Thai Celadon on white background
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Open source intelligence. OSINT. Open data access. Open source analysis. Cyber analytics. Data gathering. Wireframe hand places an element into a composition visualizing OSINT. Vector illustration.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Self made moisturizer and green jade face roller and essential oil on marble cutting board on stone off white table. Facial massage. Green plant is Cylindric Sedge or Cyperus retrorsus. spikelet.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Green jade goden pothos plant and white clock
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Surface of jade stone background or texture.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Virus and scam theme with hand pressing tablet computer screen
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
cybercrime, hacking and technology crime - male hacker in dark room using laptop computer for cyber attack
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Green white marble wall surface gray pattern graphic abstract light elegant for do floor plan ceramic counter texture tile silver background.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Privacy safety concept . Mixed media
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Dark blue green teal jade cyan aqua abstract watercolor. Colorful art background for design. Color gradient, ombre, mix. Grunge. Stains, blur, daub.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Ransomware Malware Attack And Breach
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Life hacks - gears concept - 3D illustration
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Face massage. Smiling woman using jade roller for skin care
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
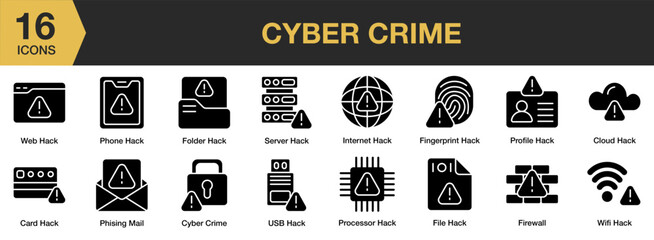
Cyber Crime solid icon set. Includes web hack, server, profile, wifi, processor, internet, and More. Solid icons vector collection.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Information privacy. Vector illustration. Information privacy is metaphorical key unlocks protection and safety personal data Safeguarding access to sensitive information is crucial for maintaining
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Woman hand holding facial jade massage roller or gua sha over the white background.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Communication and phishing concept
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Facial jade roller icon in silhouette. Skin care and relaxation massage. Anti aging tool pictogram for web, mobile, decoration, logo template. Isolated vector illustration in trendy graphic style
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
System hacked warnings alert Cyber attacks on a computer network, viruses, Spyware, Malware, or Malicious software. Cyber security and cybercrime concept. Compromised information Internet.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Cyberattack cybercrime hacker smartphone. Internet web hack technology. Digital mobile phone in Scammer hand. Data protection, secured internet access, cybersecurity banner, Stealing data information.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Cyber crime and intellectual property rights concept. Abstract low poly style. Vector illustration.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
view form top of Jade Dragon Snow Mountain
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Fraud icons. Abstract digital hacker icon set in futuristic glowing dots style. Skull, bag, unlock, data server, broken shield, and bank card with red glitch dangerous particles. Vector illustration.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Chinese name stamp jade carved block craftsmanship
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Beige abstract poster with light spot. Gradient mesh grid background. Green banner. Vector illustration
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Bitcoin security. Protecting Cryptocurrency from Hacking. Secure Bitcoin Wallet. Digital Currency Theft Concept. Flat Vector illustration
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Hacker using network interface in city
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Judge gavel with laptop computer on wooden background
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Protection concept of digital and technological.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
online thief hack important financial data credit card password
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Geisha figurine made of jade isolated on white background. Statuette of nephrite in the Oriental style. Vector cartoon close-up illustration.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Dzikie konie pastwisko zachód słońca
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Glitch noise static television VFX. Visual video effects stripes background, CRT tv screen no signal glitch effect
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Hack. Hacker stealing confidential data, personal information and credit card detail. Hacking concept.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Young woman using jade roller at home
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Abstract Red Background with Binary Code. Malware, or Hack Attack Concept
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Digital blue background. Information code. Binary computer code. 3d rendering
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
jade flower progressing to bonsai
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
piękne konie na łące, pastwisko i ogrodzenie
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Ransomware Malware Attack. Business Computer Hacked
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Online banking alert system provides fraud protection and warning for phishing attacks, virus threats, bug detection, password security, and hacking risk shielding account datum
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Hacker online phishing password from businessman on fake web template. Cyber crime attack against digital security system technology. 3D vector.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Login and password. Login via mobile app. Login via password or touch ID. Access to personal data through a password code or touch ID. Signed in with your device. Vector
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
klacz konia arabskiego na zbliżeniu
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Ludzie jadący konno po polu. Horse riding.
Do ulubionych favorite_border
Usuń z ulubionych favorite