-
Jade stone green gemstone with shape of egg, semiprecious jewelry chinese souvenir related to massage and fortune
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Digital Glitch Effect 3D Abstract Background In Ultra High Definition Quality. Dynamic Vivid Color Striped Conceptual Art Illustration
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Beautiful woman using green jade roller for face massage . Daily Jade Roller Facial Massage Routine
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
POV - horse carriage ride through golden field. View from horse carriage. Summer view at sunset
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Broken glass radial cracks shards silhouette set, Geometric circles decay grunge texture, Vector illustration.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
cyber threat risk management , hacking protection , malware and virus prevention
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
A woman applies a jade roller to her face, showcasing a glowing, healthy complexion.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
2d illustration cyber crime and internet privacy hacking.Network security,cyber attack,computer virus,ransomware and malware concept
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
skull in the digital matrix on the BCD stream on the screen. computer matrix numbers.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Beautiful woman with jade massage roller. Vector line art
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
You have been hacked! Text inscription in a distorted glitch style on a black background. Vector illustration.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
jade Dragon snow mountain Lijiang city
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
matrix style binary code digital falling numbers blue background
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Young woman using gua sha stone in bathroom mirror reflection
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
healthy green crassula ovata succulent jade plant lucky money tree indoor on window-sill
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Plastic bank credit cards and fishhook on computer keyboard
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Biohacking flat lay concept. Top-down view of still life and word Bio Hacking on chalkboard
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Jade market in Hong Kong 香港の翡翠市場
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Close-up of woman's hand wearing a jade rings
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Phishing concept background, Phishing email, Data Breach, Theft, Steal. Data Hacking Background
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Baishui river at Jade Dragon Snow Mountain
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Fliegenhaube für das Pferd
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Chinese jade bracelet features
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Weight Loss Hacks phrase on the sheet.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Blue green abstract background. Gradient. Toned rough cracked stone surface. Teal background with space for design.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Top view photo of eucalyptus rose quartz roller and gua sha on isolated white background with copyspace
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Face jade roller, gua sha, eucalyptus branches on stone surface. Flat lay, top view, overhead.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Creative code skull sketch and hands typing on computer keyboard on background, theft of personal data and malware concept. Multiexposure
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Guasha Face Lymphatic Drainage Massage with Jade Stone Roller
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
źrebak konia arabskiego z klaczą
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
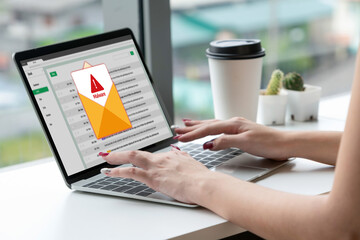
Cyber attacking concept. Malware alert showing on computer screen display scam and threat detection on computer system or online server to be removed snugly.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
China digital technology flag
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Hacker with mobile phone using computer in dark room
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Necklace made from natural green onyx stone, agate (layered chalcedony), gray-blue Labrador beads stone and jade beads on an old brown linen cloth. Onyx stone is powerful energy talisman.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Ancient mayan jade necklace
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Protect mechanism, system privacy
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
encrypted programming security hacking code data flow stream on display new quality numbers letters coding techno joyful video 4k stock image
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Faceless thief or hacker stealing login password, money, email, privat messages and credit cards using virus. Flat criminal illustration of hacker coding bug to hack data. Internet security of thief
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Life Hacks, message on note paper, computer and coffee on table, 3D rendering
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Mountain background vector. Minimal landscape art with gold line art texture. Abstract art wallpaper for prints, Art Decor, wall art and canvas prints.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Hacker in mask hacking computer system password, breaking into online server, anonymous attacking database. Cybercrime, woman hacker stealing information portrait at night time
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Green emerald marble seamless glitter texture background, counter top view of tile stone floor in natural pattern.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Shocked young business woman in white shirt posing isolated on grey background. Achievement career wealth business concept. Mock up copy space. Hold say cloud with lightbulb, put hand prop up on chin.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Automobile hack computer program.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Glitch pixel background with cyberpunk screen effects and digital noise patterns. Retro VHS static overlay and neon error lines for gamer designs. Futuristic 80s retrowave aesthetic vaporwave.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
thick, fleshy green leaves and reddish stem of Portucalaria Affra, an easy to care succulent plant, also known as elephant bush or dwarf jade.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Scenic view of Blue Moon Valley and Jade Dragon Snow Mountain in Lijiang, China
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Guasha stone line icon set, face massage concept, soft skin health products vector icons, facial jade stone roller, oil, creme emblems, anti-aging gua sha tool symbols isolated on white background
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Camera lens with purple backlight. Side view of the lens of camera on purple background. Purple camera Lens close Up.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Ethical hacking concept with faceless hooded male person
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Closeup surface abstract marble pattern at the marble stone floor texture background in black and white tone
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Thief and hacker icons in hood and mask, flat and outline styles. Crime and cyber security symbols for danger themes
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Programming coding screen, web developer coding screen
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Medical Hospital Malware Ransom Extortion Breach
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Jade : Beautiful green jade bracelet isolated on white background
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
A computer popup box screen warning of a system being hacked, System hacked alert after cyber attack on computer network. internet virus cyber security and cybercrime. hackers to steal the information
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Abstract glitch effect background. digital art. pixel glitch texture. Data visualization concept. digital distortion and noise effect. banner or poster. Vector Illustration.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Programmer and woman Sitting on Computer Monitor with Blocked Account on Screen, Cyber Attack. Censorship Blocking or Ransomware Activity Security. Flat vector Illustration.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
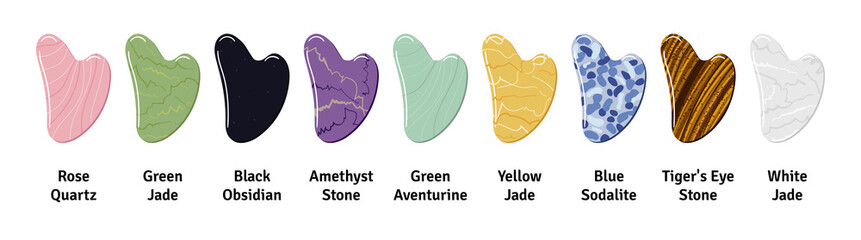
Big set of different gua sha stones with title are made of quartz, aventurine, jade, amethyst, sodalite. Facial gua sha massage tools, Chinese skin care. Hand drawn vector illustration.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Green blue abstract background. Toned mountain texture. Close-up. Marble pattern effect. A combination of jade color and rough rock texture. Green stone background.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
cartoon jaded rabbit face
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
adware attack concept with alert notification of phishing advertisement on laptop screen, vector flat illustration
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Abstract digital cloud skull on blue background. Cloud computing, hacking and data theft concept. 3D Rendering.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Natural green jade nephrite mineral stones beads. Green and grassy natural background made of round stone beads
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Hand drawn sketch of Succulent. House plant Crassula ovata, jade plant. Vector illustration of Money tree in flower pot isolated on white background. Black Line drawing. Vintage engraving.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
piękne konie na łące, pastwisko i ogrodzenie
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Computer coding prompt cyber security futuristic artificial intelligence in business finance, AI-powered analyze big data, showing charts and performance metrics for strategic planning.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Hacking Detected. Concept meaning activities that seek to compromise affairs are exposed Entering New Programming Codes. 3d illustration
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Software source code. Programming code. Programming code on computer screen. Developer working on program codes in office. Source code
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Creative Woman At Work. Business Hack
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Pearls and Jade Pothos Plant
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Springbrunnen - Park - Stadtpark - Zossen - Deutschland - Brandenburg - Park - Brunnen - Fountain
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Self made moisturizer and green jade face roller with pieces of ice. Exotic fern leaves and water drops on off white background. Monochromatic white green look. Facial massage, handmade cosmetics.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
view form top of Jade Dragon Snow Mountain
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Close up hands Hackers. Hacking to steal important information. Use a computer to release malware viruses Ransom and harass organizations. He sitting in the dark room with neon light
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Cityscape panorama with security system.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Hacker hand touches binary code and hacks abstract database, firewall, computer internet server, social network account, theft of data. Binary code abstract programming background, vector
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Cyber attacking concept. Malware alert showing on computer screen display scam and threat detection on computer system or online server to be removed brisk.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
matrix style binary code digital falling numbers background
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Blue green rock texture. Toned cracked crumbled rough mountain surface. Close-up. Dark teal color. Colorful background for design. Fantasy, fantastic, mystic.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Haking into crypto world . Mixed media
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Creative shot of trendy pink jade roller.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Hack. Hacker stealing confidential data, personal information and credit card detail. Hacking concept.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Young surprised shocked woman wears shirt casual clothes holding index finger up with great new idea looking camera isolated on plain pastel light blue background studio portrait. Lifestyle concept.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Glitched computer screen with random broken encoding, ascii art and console window like in retro PC of 80s-90s. Concept of ransomware, Code Injection and cyber security.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Cybersecurity cybercrime internet security, VPN computer privacy protection cyber security platform 3D AI robot hacking malware virus attack defense, online network IoT digital technology
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
HACK - Glowing Neon Sign on stonework wall - 3D rendered royalty free stock illustration. Can be used for online banner ads and direct mailers..
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Do ulubionych favorite_border
Usuń z ulubionych favorite