-
DDoS ATTACK inscription, online attack concept inscription, online security concept.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Digital yellow pixel pattern background with glowing squares - cyber grid for game interface, tech wallpaper, streaming overlay and futuristic design project with neon mosaic texture on dark surface.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Emerald Grunge Mosaic. A vibrant green abstract pattern with distressed textures, ideal for nature-themed backgrounds, artistic web design, or creative digital overlays.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Green jade bevel extrude 3d style isolated letters
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Hacker icon element for design projects and web designs
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Cyber security technology for business and internet project with lock image
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Concept of internet privacy and cyber protection. 3D digital world map inside a glowing sphere with shield and lock icons. Cyber attacks and protect against viruses. Network and data safety. Vector.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
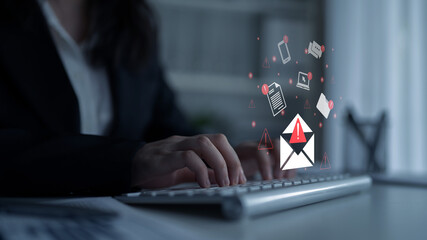
Phishing email alert concept showing digital envelope with warning sign represents data theft, network breach, and email security threats. Parse
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Latin woman using a jade roller on her cheek, taking care of her skin during a beauty routine
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Dark backdrop features vibrant green gradients, soft shapes. Text BACKGROUND present, minimalist design, modern aesthetic.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
3D Illustration of orange purple digital glitch and hex code on black background. Cyber pattern in digital matrix wallpaper texture concept as a neon sci fi effect and data flow scheme.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Safety concept: target and Phishing on wall background
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Closeup surface marble pattern at marble stone wall texture background
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Binary numbers fall like digital rain on a blue background. Futuristic cyber stream, abstract tech pattern, software code, matrix effect and information security design. Vector illustration
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Hacker. firewall hack on pc cyber thief. vector horizontal banners with place for personal text
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Technology concept is attacked, computer cybersecurity defense system is hacked or destroyed. Interfering internet network. The unlocked red padlock stands out in the center of a small binary polygon.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
A jade plant (crassula ovata) sitting on the windowsill and soaking up the sunshine.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Skin care concept with green face roller on white background
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Gold mountain background vector. Mid century landscape art with sun and moon, Sea and Ocean. Modern contemporary art design for acrylic canvas , digital Prints, wallpaper, Poster, metal poster prints
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Beauty treatment. Attractive young women looking at camera, using jade roller and facial gua sha while posing together isolated over beige background
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
jade gemstone mineral on collection
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Digital yellow pixel pattern background with glowing squares - cyber grid for game interface, tech wallpaper, streaming overlay and futuristic design project with neon mosaic texture on dark surface.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Hanging bunch of outline Strongylodon flower or Jade vine in pastel turquoise colored isolated on white background.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Abstract floral pattern with bold outlines and layered organic shapes
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Data Security system concept, Businessman use mobile phone with text hacked and security icon screen, innovation technology, cloud computing, internet network communication
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
System hacked warning alert with hand touching digital red triangle on futuristic interface background in cyber attack concept scene.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Illustration of a jade magatama
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Unsecure and buggy programming code filled with errors and strange logic. Code contains insecure queries, broken validation, weird functions, and programming flaws for demonstration. Latch
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Green Jade Crassula ovata Plant Leaves in Natural Light
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
jade emperor taoism line icon vector. jade emperor taoism sign. isolated contour symbol black illustration
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Young insighted smart proactive woman of African American ethnicity she wear blue shirt casual clothes holding index finger up with great new idea isolated on plain pink background. Lifestyle concept.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Jade roller for face massage. Pink gua sha facial massager tools. Anti age, lifting and toning treatment, monochrome beauty industry banner with copy space, wellness, wellbeing concept
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Concept of hacker attack, fraud investigation, internet phishing attack, evil win, personal privacy data, hacking and stealing email and money with tiny people. Vector illustration in flat design
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Hacker Head Logo Vector Template Illustration Design. Mascot Hacker Logo design
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
collection of various Jade natural mineral gem stones and samples of rock isolated on white background
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Young african american woman with closed eyes using facial jade roller as skin treatment
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Cyber crime and internet privacy hacking. Network security, Cyber attack, Computer Virus, Ransomware and Malware Concept. 3d illustration
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
close up of portulacaria afra, elephant bush or dwarf jade plant, with rain drops
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Hand holding of a green jade ring on a black background
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Woman Protecting Her Business From Cyber Security Breach
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Cybersecurity phishing attack and data protection icon set
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Digital yellow pixel pattern background with glowing squares - cyber grid for game interface, tech wallpaper, streaming overlay and futuristic design project with neon mosaic texture on dark surface.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
AI software on laptop used by Chinese security service programmer to commit terrorism attacks. Artificial intelligence tech used by CCP government to hack neighbor countries, isolated over China flag
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Power grid hacked, shutting down message on screen, futuristic electric meter. Futuristic electricity meter device
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Australia Circular Flag with Cyber Attack Titles - 3D Illustration
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Technology background. Big data concept. Binary computer code. Vector illustration.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Quick tips badge. Vector illustration
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
A diverse group of professionals stands together, symbolizing teamwork and cybersecurity in a digital landscape, highlighting the importance of data protection for businesses. Cyphers
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Hooded hacker threatens a laptop with a caution folder icon.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Ethical Hacking icon set. Includes symbols for hacker, fraud, security, crime, hack, cyber and more. Hacking linear icon. Icons for UI design. Outline and solid pictogram.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Lijiang, China, watch the Lijiang performance and climb the jade dragon mountain
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Cyber security hacker smartphone. Internet web hack technology. Digital mobile phone in hacker man hand isolated on black banner. Data protection, secured internet access, cybersecurity.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Woman doing self massage with rose quartz face roller
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Jade Buddha Temple, Shanghai, China
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Green abstract background with fluid light patterns and vertical lines.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Kraftpakete bei der Arbeit
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Green jade marble watercolor background
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Rough natural green tone color paint on blank eco environmental friendly cardboard box paper texture background with space minimal style
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Jade Emperor Pagoda, a Buddhist temple in District 1, Ho Chi Minh City, Vietnam
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Vertical scanlines glitch effect overlay, VHS screen lines, TV static interference pattern. Retro CRT monitor noise texture isolated on white. Motion blur speed stripes for video transition effects.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Abstract digital background with a green glitch pixel texture. black backdrop. binary code. data transfer concept. vector illustration. and technology concept. tech or cyber design.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Digital yellow pixel pattern background with glowing squares - cyber grid for game interface, tech wallpaper, streaming overlay and futuristic design project with neon mosaic texture on dark surface.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Skin care products in the bathroom. Face cream, serum bottle, jade roller and stack of towels.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Businessman using laptop with electronic email hacking and spam warning symbol. cyber attack network, virus, spyware, Cyber security and cybercrime.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Real jade is green jade for making jewelry.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Hackathon - word from wooden blocks with letters, hackathon hack day, hackfest or codefest event concept, random letters around, white background
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
AI strengthens cyber security with artificial intelligence threat detection, AI-based protection layers, and virtual assistant alerts against breaches. Kernel
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Abstract tech vector background with red halftone light effects, glowing digits and pixel data pattern. Modern digital fintech design with mesh texture and convex bubble elements
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Abstract High Technology horizontal background with place for text. Modern technology banner design in sci-fi style. Website header concept. Flat style. Vector illustration
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Pferd - Bauernhof - Reiten - Horse - Allgäu
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Grunge red security notice word square rubber seal stamp on whtie background
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
abstract green marble surface texture background
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
fishing hook phishing hack username and password
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Konie Na Wybiegu Ze Stajnią z Cegły w Tle
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Caucasian young adult woman smiling while holding jade facial roller in hand, standing against plain background, demonstrating skincare routine and self care concept
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Email Spam concept. Person use smartphone with virtual screen of Spam email notification, warning notification and spam message.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Abstract virtual code skull hologram on US flag and skyline background, cybercrime and hacking concept. Multiexposure
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Futuristic geometric banner set. Modern technology banners collection in cyberpunk style. Futuristic hi-tech badges for digital products promotion
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Abstract Technology Binary Code Dark Red Background. Cyber Alert
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Green marble patterned texture background
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Glitching computer screen, glitch programming code. Virtual environment, programm function failure and data loss, critical code mistake, hacker attack or hardware malfunction concept vector background
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Vector Abstract digital artwork, a seamless allover pattern of layered amorphous shapes in varying shades of jade and teal green, with a dark, almost obsidian, splotch at the center. Design
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Danger sign. Hacked system or cyber attack. Warning symbol on the screen. Vector illustration.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Internet scam, online fraud concept set. Cyber crime, personal data phishing. Hackers, thieves hack accounts, theft digital money, cheats people. Flat isolated vector illustration on white background
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Debugging firewall. Antivirus scanning. Malware fixing. Virus attack, trojan search, bugs detection. System protection. Threat diagnostic. Crash tester. flat design modern illustration
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Home plant succulent crassula or jade bonsai
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
A focused businesswoman utilizes a laptop, with digital email icons and warning alerts showcased above, symbolizing modern communication and cybersecurity challenges. Gantry
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Cyborg hand protection Privacy server from hacker.Data security protection interface used by robot.Cyber Digital security,Smart system and web security Data Business Technology concept.3D rendering
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Computer hacker hood touches touchscreen with lock symbol and binary code. Light waves on abstract binary background hacker silhouette. Hacking computer system, database server, data theft, vector
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
green nephrite ball on black background
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Man doing machine hack squat exercise. Flat vector illustration isolated on white background
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Green jade Carving It is a beautiful dragon.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Geometric Triangular Pattern Matrix Effect. Red Black Triangle Background Halftone Mosaic Style for Fintech Cybersecurity, Hacker Attack, Computer Fraud, Scammer and Phishing. Vector illustration
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Ransomware Cyber Attack Showing Personal Files Encrypted
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
User Man Vector Icon Glitch
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Beautiful abstract color yellow and green marble on black background and gray and green granite tiles.Polygonal Mosaic Background with terrazzo flooring.Radient 4k hd high resolution stripes polygon
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
AI powered System hacked alert after cyber attack on computer network compromised information concept. hand using latop computer internet virus cyber security and cybercrim.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Abstract Binary Code Dark Background. Cyber Space
Do ulubionych favorite_border
Usuń z ulubionych favorite