-
Digital security concept illustrating a cybersecurity breach, with a red unlocked padlock indicating data exposure among secure systems, emphasizing system vulnerability and risk Vouch
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Man doing machine hack squat exercise. Flat vector illustration isolated on white background
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Young insighted smart proactive woman of African American ethnicity she wear blue shirt casual clothes holding index finger up with great new idea isolated on plain pink background. Lifestyle concept.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Innovation, network, technology, security, information, privacy, internet, software, neural, system, secure. The world innovation technology on up hand. information privacy and neural system.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Increasing Security level. Cyber security concept. Wireframe hand is pulling up to the maximum position circle progress bar with the secure shield icon. Enhance data protection. Vector illustration.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
hacked glitch neon editable text effect
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
compromised election or foreign hackers nterference concept
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
collection of various Jade natural mineral gem stones and samples of rock isolated on white background
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Beautiful abstract color yellow and green marble on black background and gray and green granite tiles.Polygonal Mosaic Background with terrazzo flooring.Radient 4k hd high resolution stripes polygon
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
AI powered System hacked alert after cyber attack on computer network compromised information concept. hand using latop computer internet virus cyber security and cybercrim.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Indoor potted jade plant illustration
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Woman using jade roller on cheeks
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Real jade That is the original jade ball Green and rare, expensive
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
African woman cover mouth with hands reading awful news online
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Writing note showing Life Hacks. Business concept for technique adopted analysisage ones time and daily activities Blank White Huge Oval Shape Sticker and Megaphone Shouting
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
greenstone industrial jewelery
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Hand and warning caution 404 page not found error system or problem computer network or firewall protection for cyber threat attack security risk alert hacker or cybercrime safety or virus prevent.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Idea theft, plagiarism, man in mask stealing light bulb idea from another owner. Hacker works on laptop. Anonymous criminal, intellectual property. Cartoon flat isolated vector concept
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Jade facial roller on pink background with copy space
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
A focused businesswoman utilizes a laptop, with digital email icons and warning alerts showcased above, symbolizing modern communication and cybersecurity challenges. Gantry
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Green jade face roller, natural stone for skin care, on white backdrop. Tool for facial lifting massage, trendy therapy
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Pair of silver earring with circle jade closeup
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Electronic spamming concept with faceless hooded male person
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Retro CCTV or VHS Video White Noise Abstract Grunge Background. CRT Scanlines Vibration Glitch. Video Damage Overlay Texture. Nostalgic Vintage 80s 90s Surveillance or TV Tech Vector Illustration.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Urgent Warning Cyber Hack Threats Targeting Businesses in Urban Environments - Comprehensive Guide to Protect Your Digital Assets
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
sample of raw teyskiy jade rock on white marble
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Glitch noise static television VFX. Visual video effects stripes background, CRT tv screen no signal glitch effect
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Abstract Elegant dark green background with mottled vintage texture in old fancy background design, texture of colored parchment paper.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Hacker using creative glowing big data interface.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Dollar plant or money tree
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Jade Bangle isolated on white background
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Quick tips badge. Vector illustration
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
cybersecurity for business managed the document privacy to protection online data by lock icon virtual screen technology.protecting personal data on laptops interfaces prevent mail from scammer hacker
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Black hood hacker force demands ransom by holding out his hand on table where sensitive data is hacked in a dark room in the background. Cyber security and cyber crime concept. Hacking and phishing
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Cyber security or cybercrime attack and threats to the Internet personal information computer network or key lock login to privacy website protection or email access identity concepts.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Computer processing work Notify a security alarm error.computer system notification,Warning System hacked,3d rendering
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Facial massage kit - amethyst and jade gua sha face rollers on stone concrete background. Natural stone face massager, skin care concept
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
slab of green Nephrite stone on white
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
A diverse group of professionals stands together, symbolizing teamwork and cybersecurity in a digital landscape, highlighting the importance of data protection for businesses. Cyphers
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
set from raw minerals and ores with names isolated on white background
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Cute Colorful Typography Lettering productivity hacks
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Jade pendant isolate on black background. Icy blue Burmese jadeite Jade carving with Happy Buddha, longevity peace, lucky bird, Chinese coins, ruyi, peony and pearls. Rare color jadeite jade
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
A woman uses a jade roller on her face, a popular beauty treatment.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Group of hackers steal personal information from computer. Internet thieves hack laptop security system, get secured data and passwords. Web robbery and fraud. Vector illustration.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Malware concept. Concept of virus, piracy, hacking and security. Website banner of e-mail protection, anti-malware software. Computer Viruses Attack, Errors detected, Warning signs, Stealing data.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Jade Buddha temple, Shanghai, China. 02/05/2019
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Open red padlock on steel chains, mock up
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Vollblut Araber Stute auf Weide
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
green cosmetic rollers. Tools and means for face care.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Amazed African employee read news seated at desk
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Green jade marble watercolor background
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Rough natural green tone color paint on blank eco environmental friendly cardboard box paper texture background with space minimal style
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Glitching computer screen, glitch programming code. Virtual environment, programm function failure and data loss, critical code mistake, hacker attack or hardware malfunction concept vector background
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
green nephrite ball on black background
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
konie spacerujące po śniegu
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Facial massage kit on stone concrete background - jade gua sha tool and face roller with cosmetic moisturizer or face cream tube and blooming sakura branch. Natural stone face massager, mockup
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Jade gua sha tool, spa stones and eucalyptus branches on grey table, flat lay
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Unsecure and buggy programming code filled with errors and strange logic. Code contains insecure queries, broken validation, weird functions, and programming flaws for demonstration. Latch
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Jade roller isolated on white background.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Eco friendly natural cleaning tools and products, bamboo dish brushes and lemon with baking soda. Zero waste concept. Plastic free.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Wifi connection signal icon with hacker attack icon in the circle. vector illustration isolated on modern background.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Hacker holding mobile phone
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
User Man Vector Icon Glitch
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
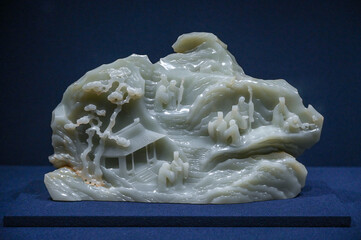
Jade carving decorative crafts in ancient China
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Flat green beans isolated on white background.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
concept of computer security
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Grunge HACKED round stamp seals isolated on a white background. Round seals with grunge texture in red and blue colors. Vector rubber overlay of HACKED label inside circle form with stripes.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Cyber crime and internet privacy hacking. Network security, Cyber attack, Computer Virus, Ransomware and Malware Concept. 3d illustration
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
jade jewelry, jade stone, jade, green jade, gemstone, leaves, water, white, nature, green
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Spam SMS fake phishing message from scammer concept. Red alert hack system, email hack.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Cybercrime email Spam concept. E-mail Popup Warning Window: The computer shows a malware screen that comes with email, hack passwords from bank accounts, and personal data cybersecurity
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
jade from China isolated on white background
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
yellow marble on a white background
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Wanted Hacker is Coding Virus Ransomware Using Abstract Binary Code. Cyberattack, System Breaking and Malware Concept.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Abstract virtual code skull hologram on blurry contemporary office building background, cybercrime and hacking concept. Multiexposure
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
A united group of hands symbolizes teamwork and collaboration in a digital transformation project, highlighting technology and coding in a modern business environment. Trope
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Beautiful Asian woman uses jade roller to massage her face
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Hacker with hidden face in a hoodie uses a mobile phone to hack the system
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Glitch noise static television VFX. Visual video effects stripes background, CRT tv screen no signal glitch effect
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Virus bot robot hacker. Network piracy danger. Errors on monitor screen. Pirate attack artificial intelligence concept
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Tropical flowers, the Strongylodon Macrobotrys emerald turquoise Jade Vine inside a greenhouse in Hiroshima in Japan. Ornamental plant with greenish-blue claw-shaped flowers.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Chinese translation: Happy Mid Autumn Festival banner with mooncakes, jade rabbits, flowers, moon, clouds. Traditional holiday in Taiwan, Japan, Korea, Vietnam. Oriental greeting bg. 3D illustration
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
2plus3blog Kozia Góra Szyndzielnia Bielsko Biała Bystra
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
cyber crime phishing mail , security awareness to protect important data hacking
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Flat lay white jade face roller, gua sha, serum, moisturizer cream, flowers on stone background. Skin and facial treatments concept.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Ransomware Malware Attack. Business Computer Hacked
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
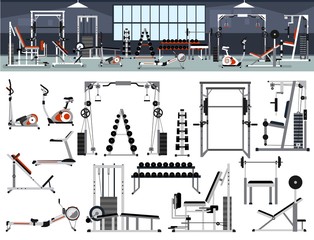
Gym interior builder. Fitness center design in flat style with power rack,Bench Press, Pull-Down, Pec Deck, Dumbbells, Exercise Bike, Leg Curl, Hack Squat, Leg Extension,leg abduction, Smith Machines.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Young insighted smart proactive woman she in red shirt casual clothes glasses holding index finger up with great new idea isolated on plain pastel green background studio portrait. Lifestyle concept
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Rose Quartz jade roller and Gua Sha massager on white towel. Massage tool for facial skin care, SPA beauty treatment concept
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Galop, wyspa Olchon, jezioro Bajkał, Syberia, Rosja
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Cyber security concept, Login, User, identification information security and encryption, secure Internet access, cybersecurity, secure access to user's personal information,
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
View of Yulong Mountain with blue sky and white cloud
Do ulubionych favorite_border
Usuń z ulubionych favorite