-
Privacy concept: Cctv Camera on computer keyboard background
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Lijiang: Jade Dragon Snow Mountain
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Houseplant Crassula jade plant money tree in white pot in home - home gardening concept
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Woman sitting on couch reading message on computer feels shocked
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
hacked exclamation pc board
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
skull of death on smartphone screen. virus alert on mobile phone on tablet computer
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
jade jewelry, jade stone, jade, green jade, gemstone, leaves, water, white, nature, green
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Hacker Attack Concept Icon Set 3d Isometric View. Vector
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Rose quartz facial massage roller with essential oil on monstera leaf. Face massage tool, anti-aging, anti-wrinkle beauty skin care concept. Flat lay, top view
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Pagaz w dolinie A4 coloring book
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
white digital matrix of binary code numbers background
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Pixel glitch effect background - colorful distorted digital noise, random horizontal lines, strips, blocks. Retro futuristic design, abstract glitched texture for web pages. Neon colors on dark.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Pixel bitmap texture pattern. Geometric pixel pattern. Abstract bitmap retro design. Vector illustration
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Skincare concept. Top view photo of rose quartz roller and eucalyptus on white marble background with copyspace
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Digital world cyber hack glitch
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Futuristic Glitch background. Abstract pixel noise glitch error video damage like Vhs glitch. Pattern for wallpaper design. Screen error effect. Abstract background. Medical background. Cosmic
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Hacker with laptop stealing user login. Hacker sitting at the desktop and hacking user personal data. Hacker attack and web security
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Crassula ovata, bonsai tree on green background with copy space
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
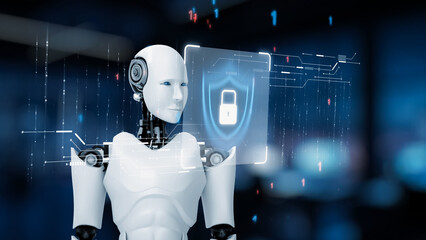
AI strengthens cyber security with artificial intelligence threat detection, AI-based protection layers, and virtual assistant alerts against breaches. Kernel
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Green marble pattern texture abstract background / texture surface of marble stone from nature / can be used for background or wallpaper / Closeup surface marble stone wall texture background.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Jade vine, colorful of flower in the garden.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Natural green jade nephrite mineral stones beads. Green and grassy natural background made of round stone beads
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Hacker man steal information
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Krajobraz wiejski Podlasia. Konie na łące, Podlasie, Polska
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Wanted Hacker is Coding Virus Ransomware Using Abstract Binary Code. Cyberattack, System Breaking and Malware Concept.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Abstract digital cloud skull on blue background. Cloud computing, hacking and data theft concept. 3D Rendering.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Anonymous hacker and face mask with smartphone in hand. Man in black hood shirt trying to hack personal data from mobile phone. Represent cyber crime data hacking or personal data stealing concept.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Small kid child girl housewife chef cook baker mother's helper wear yellow apron toque cap holding index finger up with great new idea isolated on pastel plain pink background. Cooking food concept.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Hacker doing illegal activities in secret underground base, uploading USB flash drive containing data obtained from victim after tricking it into installing ransomware program, camera B
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Cyber security destroyed. Padlock red opens on code connection dark red background.Cyber attack and Information leak concept.Vector illustration.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Redhead beauty girl massage facial healthy glowing skin with pink quarz roller, jade lifting tool for better skin tone, blood flow balance, treating dark circles and puffiness on young and fresh skin
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Green face roller and gua sha massager made from natural jade nephritis stone over marble background.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Infecting a laptop with a Computer Virus via usb stick, free copy space
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Digital locker icon in a Server room data center - 3d rendering
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Golden Bitcoin floating above of hacker's hand in dark background. Finance, business, e-commerce or cyber crime concept
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
illustration of counting tax hacks with paperworks, calculator and money on top of table and purple background
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
AI strengthens cyber security with artificial intelligence threat detection, AI-based protection layers, and virtual assistant alerts against breaches. Kernel
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Young sly man trying to breach the system while giving bad commands on laptop in empty dark office
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Concept of hacker attack, fraud investigation, internet phishing attack, evil win, personal privacy data, hacking and stealing email and money with tiny people. Vector illustration in flat design
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
jade buddha figure for lifestyle graphics
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Clever life hacks solution light bulb icon label banner graphic design vector illustration for easy living
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Binary Code backgrounds, a sequence of zero and one number on a red background. Numbers of the computer matrix. The concept of coding, cybersecurity and crime, and cryptocurrency
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Ransomware Business Computer Malware Privacy Breach
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
2d illustration abstract binary skull
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Ancient mayan jade necklace
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
reclining statue in the The Jade Buddha Temple shanghai china
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Stadnina koni / Kaszuby / pomorskie / Polska
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Jade Light Prism Whisps: Abstract background featuring delicate jade light whisps and a soft prism effect. Use as a gentle, subtle overlay. on black or Transparent.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
desembocadura de un pequeño Río en Playa jacó, Costa Rica. Jaco Beach, Costa Rica
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Epipremnum aureum Pearls and Jade Pothos under sunlight on wooden table
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Digital background. Big data. Hacker concept. Abstract matrix. Computer generated many numbers. Vector Illustration
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Flowering jade plant in a pot
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Girl in bandage on head uses beauty gua sha jade quartz roller. Satisfied smile. Perfect glowing skin, massage.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Set of outline Strongylodon flower bunch or turquoise Jade vine, bud and leaves in black isolated on white background.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Warning alert icon with a hacked system. malicious software, virus, spyware, malware, or cyberattacks on computer networks. Security on the internet and online scam. Digital data is being compromised.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Phishing email alert concept showing digital envelope with warning sign represents data theft, network breach, and email security threats. Parse
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Concept of cyber crime and cyber security. Hand using laptop and show malware screen with phishing email, hack password and personal data. hackers, Virus Trojans, Encription Spyware or Malware.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Security Breach Icon Set With Multiple Style Collection
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
System hacked alert with skull symbol abstract 3d illustration
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Green jade lifting roller for face massage isolated on white
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Illustration vector isolated of chinese gods, chinese mythology, jade emperor, sky god
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Jade, gemstone for stone healing
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
A dark royal green gradient seamless pattern with a noise texture. A luxurious jade and dark turquoise silk background with soft transitions and an ombre effect.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Green jade is a beautiful mineral that symbolizes harmony and prosperity.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
A vivid VHS screen image with a square-like depiction of visual disturbances. Vector abstract illustration.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Wyoming jade isolated on white background
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Attention Danger Hacking. Symbol on Map Dark Blue Background. Security protection, Malware, Hack Attack, Data Breach Concept. System hacked error, Attacker alert sign computer virus. Ransomware.Vector
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Hacker hacked remote server or datacenter. Anonymous steals passwords, data or money. Hacker attack on cloud storage. Cyber security, crime on internet. Unreliable security system.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
3d illustration of cubic human form on technology background.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
The Highest Mountain on Taiwan Island - Mt.Jade Mountain/YUSHAN Landscape
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Jade vine, colourful of flower in the garden.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Aging process - old senior woman hands wrinkled skin
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
hacker attack , cyber threat risk management , malware and virus prevention , security awareness
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Abstract virtual binary code illustration on flag of China and blurry skyscrapers background. Big data and coding concept. Multiexposure
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Aggressive violent hacker trying to hack network in office, feeling mad about hacking system failure. Dealing with hardware error trying to steal server information, irritated thief. Handheld shot.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
A group of professionals engaged in a discussion about email alerts and notifications. Digital icons highlight communication, emphasizing information security in a modern office. Gantry
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
3d Cyber security concept. Personal data protection, encryption technology, access code to cloud storage Cloud technology on digital circuit board. Vector illustration
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
futuristic binary code tech concept background with light effect
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
chinese new year jade green background
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Abstract green bokeh background with soft light circles and blurred texture in various shades.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
OTP phishing hacking online. Computer data fishing hack crime. Scam concept
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Young woman using jade face roller at home
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
hand holding a jade mineral
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Golden bitcoin cryptocurrency on computer circuit board
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Turquoise background with imitation of gold marble
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Jade roller and gua sha stone massager at pastel background. Anti-aging therapy. Top view.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Abstact grunge sci-fi background with geometic pixelated figures and patterns.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Money Heist Of Digital Bank Account
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Woman smiles while rolling jade roller on cheek against grey backdrop.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Portrait of beautiful young woman looks in the mirror using facial gua sha jade board at home. Lifting, skincare and lymphatic drainage of the skin concept.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
hooded hacker solar winds hack concept
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Creative code skull hologram and hands typing on computer keyboard on background, cybercrime and hacking concept. Multiexposure
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Woman gardeners transplanting jade plant in plastic pots on wooden table. Concept of home garden. Spring time. Taking care of home plants
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Innovative Concept of Digital Communication with Light Bulb and Email Icons Representing Ideas and Connectivity in Modern Networking Sigmoid
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
coffee cup with Colombian emeralds and jade , jewelry
Do ulubionych favorite_border
Usuń z ulubionych favorite