-
Cyberattack cybercrime hacker smartphone. Internet web hack technology. Digital mobile phone in Scammer hand. Data protection.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Data breach , system hack warning , security awareness
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Danger sign. Hacked system or cyber attack. Vector illustration.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Asian programer focused on writing code encounters unexpected compiling error, being hacked in software development office. Coder having system failure and dealing with hackers.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Attention Danger Symbol on Dark Red Glitched Background. Computer Virus. System Hacked Error Sign. Malware, Ransomware, Data Breach Concept. Vector Illustration.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
jade editable text effect
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Flat design illustration. Laptop on desk hacked by virus message. Virus infects tiles and other employees' computers by taking over their connection.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
black jade logo design with simple style
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Scam alert notification set icon. fraud notice alert. malware hack attack atention banner pop up. vector
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
jade gem stone as natural mineral rock
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Abstract background with binary code. Hackers, darknet, virtual reality and science fiction concept.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Hacker security cyber attack smartphone. Digital mobile phone isolated on black. Internet web hack technology. Login and password, cybersecurity banner concept.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Interior View With Statues Of Jade Emperor Pagoda In District 1 Of Ho Chi Minh City, Vietnam. This Pagoda Was Built In 1892 By Chinese And Very Famous In Ho Chi Minh City.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
abstract green marble surface texture background
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
piękne konie na łące, pastwisko i ogrodzenie
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
encrypted programming security hacking code data flow stream on display new quality numbers letters coding techno joyful video 4k stock image
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Jade vine or Emerald vine flower blooming. Strongylodon macrobotrys. The turquoise flowers of strongylodon macrobotrys, also known as jade vine, emerald or turquoise jade vine, lying on the ground
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Maori New Zealand Greenstone pounamu jade Koru (spiral fern) shape pendant on cross section of timber log
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Binary Code backgrounds, a sequence of zero and one number on a green background. Numbers of the computer matrix. The concept of coding and cybersecurity
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
skull of death on smartphone screen. Hacked mobile phone on laptop computer
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Abstract background algorithm binary programming code on blue. Concept digital data technology. Vector illustration.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Shady Hacker Binary code Design. Full vector Background
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Security Vulnerability Log4J
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Real jade Natural sparkling green color
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Konie walczące ze sobą na pastwisku
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Hacker hack and steal personal account information concept. Male in hood open someone social media account and another man hold magnet to attract victim's picture, message, chat and location.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
horses in the fog, konie na polanie, pastwisku o poranku w mglisty jesienny dzień
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Verdant green marble background with intricate white and light green veins, showcasing a luxurious and elegant natural stone texture for interior design and architectural concepts.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Jade Buddha Temple, Shanghai
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
jade stone isolated on white
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Close-up of a man using smartphone with virtual password input and login button. Concept of secure mobile authentication, user access control, and cybersecurity protection.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Konie, szlak turystyczny, Morskie Oko, Poland
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
abstract Elegant dark green background with mottled vintage texture in old fancy background design, green color, watercolor background.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Woman massaging face with jade stone
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Half-naked brunette woman massaging face with jade roller
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
bonsai jade plant in a clay pot
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Defi hacked concept. Silhouette of a hacker with a computer and text on a dark digital background. Horizontal. Vector EPS10.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Cybersecurity Threat, Warning, and Data Protection Concept. illustration depicts a cybersecurity threat, showing warning signs, a protected browser, and a distressed user, conveying internet security
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
In the middle of the night, a young businessman checks his email when he receives a notification that he has been hacked. Concept of cyber crime, hack password from bank accounts and personal data.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Reclining Buddha in Jade Buddha temple. Shanghai, China
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
konie na łące w Tykocinie, zagroda, Podlaskie,
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Real jade Natural sparkling green color
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Businessman hold low poly polygon shield with a padlock icon.Secure Access System Concept.Business Financial Warranty for Investment.antivirus concept.Technology security.Protection network,safe data.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Cyber security concept. System hacked warning alerts on a computer notebook screen. Cybercrime, virus, online hacking, cyber attack, malicious malware or software.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Dwa konie na pastwisku - part2
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Hacker in hoodie using laptop with digital warning symbols and b
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Hacked. Glitched. Abstract Digital Background.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
jade stone isolated on white background
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Network piracy danger. Errors on monitor screen. Pirate attack artificial intelligence concept. Folder with virus files.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Woman in athletic shape performing hack squats in busy modern gym, working on leg strength, balance, and overall lower body conditioning. Fitness and weight training for women concept
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
A stream of binary matrix code on the screen. numbers of the computer matrix.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Abstract Elegant dark green background with mottled vintage texture in old fancy background design, green color, watercolor background.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Iran digital technology flag
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Surface of jade stone background or texture.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Happy Chinese New Year 2024. Dragon gold zodiac sign inside jade green on red background with lanterns, cloud and flower for festival card design. Vector. (Translation : happy new year 2024, dragon)
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
System hacked, warning alert message on screen of hacking attack, vector. Spyware or malware virus detected warning red message window on computer display, internet cyber security and data fraud
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
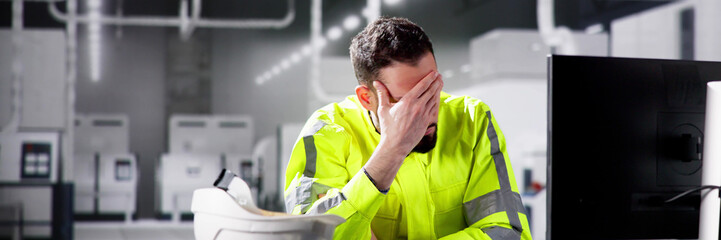
Depressed, man or anxiety with laptop or error for project deadline mistake, news or phishing website. Night, hacked or security engineer with stress for startup crisis, digital fraud or online scam
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
jade gem stone as natural mineral rock
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Green jade roller and gua sha stone for facial massage and eucalyptus branch on marble background. Home beauty and selfcare accessories. Face roller for anti age wrinkle treatment. Top view, flat lay.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Ransomware Malware Attack. Business Computer Hacked
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Abstract background algorithm binary programming code onl dark. Concept digital data technology. Vector illustration.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Bieszczady, Konie na łące. Mglisty wiosenny poranek
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Low angle shot of a male athlete training at the gym, using hack squat machine
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Beautiful nature view Jade Dragon Snow Mountain with soft white cloud on blue sky background and soft sunlight in morning, Shangri-La City or Xiang Ge Le La at Yunnan, China
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Dark Green or Jade marble texture background. High-quality natural stone with intricate Grey veins, ideal for elegant surfaces, flooring, and interior design projects. Close-up photo.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
An ornate alphabet with the effect of carved green jade
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Set of hacker and cyber criminal stealing confidential data with laptop computer illustration concept
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Binary Code backgrounds, a sequence of zero and one, black numbers, on a white background. Numbers of the computer matrix. The concept of coding and cybersecurity
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Abstract polygonal hacker with laptop on technology dark background. Cyber attack and cyber security concepts. Computer hacking. Digital technology. Man in hoodie. 3D low poly vector illustration.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
jade mineral characterized by its predominantly white coloration.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Surface of jade stone background or texture.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Green marble pattern texture abstract background / texture surface of marble stone from nature / can be used for background or wallpaper / Closeup surface marble stone wall texture background.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Hacker security cyber attack smartphone. Digital mobile phone isolated on black. Internet web hack technology. Login and password, cybersecurity banner concept.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
konie na łące, piękny jesienny krajobraz
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Beautiful dark green viridian vintage color trends feather texture background
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Końska rodzina, konie i natura, lato
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Digital background of Internet Security, system hacked
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Shocked Engineer In Automated Semiconductor Assembly Line
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Woman with vitiligo uses a green jade roller, close-up. Facial treatment with skin features
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
The emerald gemstone jewelry.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Night, cybersecurity and hands typing with phone for texting, internet troll or person cyberbullying. Dark comment, social media netizen or keyboard warrior for smartphone, online bullying or hacking
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
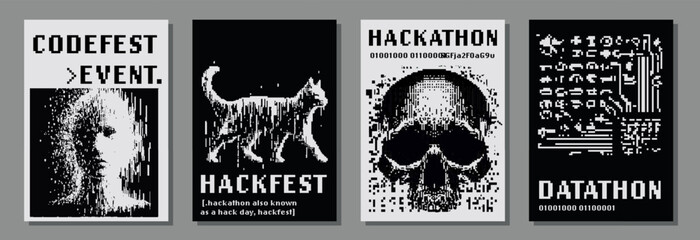
Set of retrofuturistic posters for hackathon (also known as a hack day, hackfest, datathon or codefest) event with pixel art illustrations of glitched human head and skull.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Closed up green jade with diamond and gold ring isolated
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Zaprzęgi konne na drodze do Morskiego Oka w Tatrach,
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Coding background, Application development and code programming. Technology business computers concept
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Half-naked brunette woman massaging face with jade roller
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Global networking and connection
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Small pink flowers of Crassula ovata, commonly known as jade plant, lucky plant, or money tree, is a succulent plant that is native to the KwaZulu-Natal and Eastern Cape provinces of South Africa
Do ulubionych favorite_border
Usuń z ulubionych favorite