-
Abstract grunge jade green background with golden patina
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Mountain landscape in Jade Dragon Snow Mountain (Yulong Snow Mountain) located at Lijiang, Yunnan, China.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Dark green polygonal crystal Background. Hexagonal dark mosaic cement stone concrete tile wall texture background. Dark jade stone background with rock pattern, macro. Texture of abstract backdrop.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Warning icon on a digital LCD display with reflection. Concept of cyber attack, malware, ransomware, data breach, system hacking, virus, spyware, compromised information and urgent attention.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
PC security concept. Secure connection, privacy and protection. Traffic Encryption, VPN. Bunch of keys to open padlock and get access to hack privacy, activities and user data. Illustration
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
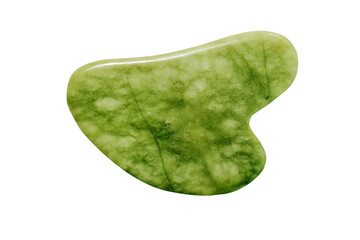
Jade roller for face massage. Green gua sha facial massager tools on the marble white background with copy space flat lay. Anti age, lifting and toning treatment, acupressure. Eustoma flowers
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Trader in office receives system hacked warning alert after unauthorized access detected on client trading account. Prop firm worker worried by hacker breaching trading platform account cybersecurity
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
natural specimens of uncut jade rocks cutout
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Spam SMS fake phishing message from scammer concept. Red alert hack system, email hack.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Set of futuristic posters with 8-bit pixel art illustrations of glitched human heads. Covers for hackathon (also known as a hack day, hackfest, datathon or codefest) event.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Real jade is green carved jade.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Nature mineral of jade stone on white background.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Bieszczady Wschodnie - Pikuj, Ukraina
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Ethical Hacking icon set showing virus, exposing vulnerabilities, and hacker. CEH - icon set and web header banner. System Cyber security and safety data concept . System hacking with info message.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Binary code with the words You have been hacked
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Padlock, lock or locked icon for social media, mobile application, password, UI template. website
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Blue Abstract Matrix Vortex Technology Background. Binary Computer Code Dynamic Spiral. Programming, Coding, Hacker Concept. Binary Numbers Moving in Spiral. Vector Illustration. Sci-fi Background.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Cyber security hacker smartphone. Internet web hack technology. Digital mobile phone in hacker man hand isolated on black banner. Data protection, secured internet access, cybersecurity.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
skull of death on smartphone screen. Hacked mobile phone on laptop computer
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Happy Chinese New Year 2024. Dragon gold zodiac sign inside jade green on red background with lanterns, cloud and flower for festival card design. Vector. (Translation : happy new year 2024, dragon)
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
jade from China isolated on white background
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Decorative indoor plant crassula in a pot
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Smiling woman massaging her face with jade roller massager and looking at round cosmetic mirror
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Green jade face roller and Gua Sha scraping for beauty facial massage therapy
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Green marble pattern texture abstract background / texture surface of marble stone from nature / can be used for background or wallpaper / Closeup surface marble stone wall texture b
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Elegant Green Onyx Marble Texture Natural Semi Precious Stone Design
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Digital database cyberspace. Decoding algorithms hacked software. Cyber security with moving particles. Big data visualization. 3d rendering.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Hacker icon symbol collection on white background.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Face massage. Beautiful woman is getting massage face using jade facial roller for skin care
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Digital background blue matrix. Binary computer code. Hacker concept. 3d rendering
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
massage stone jade gouache scraper isolated on white background.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
konie interior Islandia Landmannal
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Green onyx pattern background of a green marble texture backdrop,
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Facade View Of Jade Emperor Pagoda In District 1 Of Ho Chi Minh City, Vietnam. This Pagoda Was Built In 1892 By Chinese And Very Famous In Ho Chi Minh City.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
wordmark logo about hack, hack logo wordmark simple editable, vektor, wormark logo
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Excited young man guy 20s in casual black t-shirt posing isolated on yellow wall background studio portrait. People lifestyle concept. Mock up copy space. Holding index finger up with great new idea.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Real jade is green jade for making jewelry.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Ransomware Cyber Attack Showing Personal Files Encrypted
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Maw sit sit jade from Burma isolated on white background
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
abstract background, fashion fake stone texture, green onyx jade agate or marble slab with gold glitter veins, wavy lines, painted artificial marbled surface, artistic marbling illustration
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Digital code pattern. Matrix binary malware code. Algorithmic big data background.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
jade facial roller isolated on white background
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
greenstone industrial jewelery
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Man with hacked laptop by hacker cartoon vector illustration graphic design
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
swim ring isolated on transparent backgroundA smooth, polished teal jade ring isolated on transparent background
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Crassula ovata, commonly called jade tree, is a succulent plant.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
abstract green marble surface texture background
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
System hacked alert on computer screen after cyber attack on network. Cybersecurity vulnerability on internet, virus, data breach, malicious connection. Employee working in office.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Abstract background in technology. Padlock placed on the circuit board is part of the concept of securing safety in digital systems using advanced technology to protect against cyber attacks from hack
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
The code is on a laptop on a wooden table in front of the window in the dark with a view of the lights of the night city, color lighting in the room, home decor
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Woman gardeners transplanting jade plant in plastic pots on wooden table. Concept of home garden. Spring time. Taking care of home plants
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Chinese jade bracelet features
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Alerts flash on smartphone screen as person touches display amidst digital icons, signaling cybersecurity concerns.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Hacked. Internet crime concept. Computer display with message YOU HAVE BEEN HACKED. Network security data protection.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
HUD Warning Spam Interface Vector with Alert Display Screen UI and Critical Danger Alarm Caution.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Ransomware Malware Attack And Breach
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
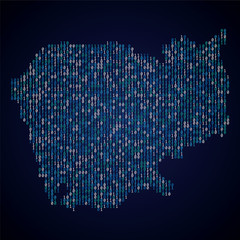
Cambodia country map made from digital binary code
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Hacked information concept
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Crassula ovata is a evergreen house plant. Also known as jade plant or money tree.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
cyber security concept, Login, User, identification information security and encryption, secure Internet access, cybersecurity, secure access to user's personal information,
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
White jade bangles on a wooden cubes over a table
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Sześć koni wielkopolskich w równym szeregu, szyku na łące, konie wyścigowe
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Warning of a system hacked. Virus, cyber attack, malware concept. 3d rendering.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Green jade roller and gua sha stone for facial massage and eucalyptus branch on marble background. Home beauty and selfcare accessories. Face roller for anti age wrinkle treatment. Top view, flat lay.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Wave jade golden line seamless pattern vector illustration. Geometric outline wavy Chinese style background
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
green stone jade crystal texture abstract nature wallpaper decorate background
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Real jade Natural sparkling green color
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Crassula ovata. Close up of flowers on a jade plant crassula ovata
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Cybersecurity Digital Shield with Secure Network Icons
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Plastic bag taped on the wall. Simple life hack for drilling without making a mess.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
High-resolution image of vibrant green jade plant succulent leaves. Perfect for botanical, nature, and plant-themed projects.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Technology stream binary code. Digital illustration. White matrix background. Programming, coding, hacking and encryption.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
dorożka nocą na rynku w Krakowie
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Close Up Of Woman Using Mobile Phone Text Messaging Using Thumbs On Keypad
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Face roller and gua sha stone massager on white background with green leaves. Top view
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
polished Jadeite (green jade) gem stone isolated
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Woman with healthy fresh clean skin using jade face roller
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
dark green marble texture use for background. luxury interior stone tile background. Statuario dark green marble background. emerald stone texture color.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Digital Binary Code on Dark Red BG. Data Breach
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Very close-up on the leaves of a Jade tree
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
System hacked warning alert on laptop. error 404 alerts on a laptop, caution of spam in website digital Cyber attack on computer network, Virus, Spyware, Malware or Malicious software. Cyber security
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Face massage jade roller with cosmetic product on white marble background
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Abstract Technology Machine Code Background. Random Binary Hexadecimal Code. Matrix with Digits. Vector Illustration. Hacking, Cryptography, Malware, Reverse Engineering, Data Analysis Backdrop.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
young beautiful woman in dressing room performing facial massage with jade roller
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Fluid Art. Liquid Velvet Jade green abstract drips and wave. Marble effect background or texture
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Profile shot of a strong athletic woman doing squats in hack squat gym machine
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
word system hacked computer
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Facial jade massage rollers and gua sha massager
Do ulubionych favorite_border
Usuń z ulubionych favorite