-
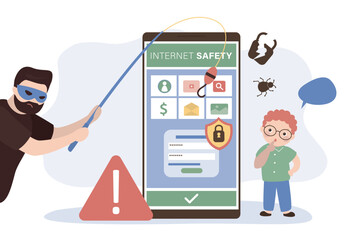
A hacker wearing a mask to cover his face is using computer to hack data to get ransom from victims.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Data security technology blue background, Ai big data secure, crime hack digital tech, abstract privacy hi tech binary code, virus attack data, internet network connection theft, illustration vector
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
cyber pirate robot hacking someone
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Green gemstone natural mineral fluoride or green beryl isolated
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Binary code on flag of Korea North. Program source code or Hacker concept on North Korean flag. North Korea digital technology security, hacking or programming
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Matrix background. Cyber security with binary code. Rapidly falling randomly green numbers. Decoding algorithms hacked software. Big data visualization.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
konie - źrebię ssące matkę
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Hacker with laptop in city, security
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Abstract futuristic cyberspace with a hacked array of binary data, broken falling binary code, matrix background with digits, big data neural network, well organized layers
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Grunge aged life hack sign on wood
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Web banner with phrase You Have Been Hacked. Concept of cyber attack, hacking or spyware
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Crassula ovata (Jade Plant,Money Plant,Friendship Tree) succulent plant in a tropical garden.Selective focus.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Green jade roller and gua sha stone for facial massage and on grey background. Home beauty and selfcare accessories. Face roller for anti age wrinkle treatment. Top view, flat lay.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Cybersecurity threat, phishing email scam concept. Man hand on phone, data breach danger. Hacker attack, internet fraud, password stealing. Spam message, virus, security risk warning.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Green jade face roller and gua sha scraper with leaves on light blue background. Massage tool for facial skin care, SPA self and beauty care treatment concept.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Life hacks written on lightbox in office as flatlay
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Woman gardeners watering jade plant in plastic pots on wooden table. Concept of home garden. Spring time. Taking care of home plants
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Jade face roller for beauty facial massage therapy, Self made skincare products with natural dill. Flat lay on off white background. Water rings, splashes. Copy-space, text place.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
White Water River waterfall and Jade Dragon Snow Mountain, Lijia
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Cartoon hacker character. Cyber threat for internet privacy and cybersecurity, phishing and hacking vector illustration set
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Beautiful new guinea creeper or scarlet jade vine blossoming in the garden tunnel
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Hacker attack icons. Hacker line icon set. Cyber, attack, software, virus, scam, hacker, fraud, hacker attack related icons. Editable stroke, thin line icons set
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
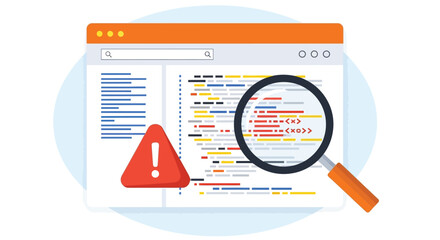
System hacked alert after cyber attack on computer network. compromised information. internet virus cyber security, cybercrime. hackers to steal the information is cybercriminal. attack, crime, cyber
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Red binary code background with cyber breach data matrix. Digital hacker attack warning with streaming numbers and malware threat elements. Technology security concept with dark futuristic design.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
red cyber hack notification alert in green matrix binary data falling with corrupted data lines background banner template
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Criminal attempting to hack computer system and getting access denied. Hacker breaking into online server unsuccessfully while doing illegal activity in abandoned warehouse
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
System hacked modern glitch concept 3d illustration
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Cybersecurity Glitch Lock and Shield Symbol on Dark Background Representing Data Protection, Firewall and Secure Access. System Under Hackers Attack. Ransomware Lock Vector Illustration.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Man enjoying head spa treatment with jade eye mask
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
sample of rough white nephrite mineral on black
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Abstract Elegant dark green background with mottled vintage texture in old fancy background design, texture of colored parchment paper.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Deep forest green paper background with a smooth matte texture and subtle geometric patterns..
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Digital security concept illustrating a cybersecurity breach, with a red unlocked padlock indicating data exposure among secure systems, emphasizing system vulnerability and risk Vouch
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Vertical scanlines glitch effect overlay, VHS screen lines, TV static interference pattern. Retro CRT monitor noise texture isolated on white. Motion blur speed stripes for video transition effects.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Earthen terracotta pot holding lush jade succulent plant
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Hand Holding a Smartphone with Multiple Glowing Red Alert and Warning Icons for Email Spam and Cyber Security Breach
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Hand drawing green jade texture seamless pattern background
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Warning alert Banners notification set icon. fraud notice alert. Malware hack attack atention banner pop up. vector
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Cyber crime awareness illustration, laptop security breach, malware alert, password hacking, digital threat icons, cartoon-style vector for online safety
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Set of heavy duty leg press and hack squat gym machines isolated on transparent background png
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Konie na pastwisku w Michałowie
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Binary code on flag of Korea North. Program source code or Hacker concept on North Korean flag. North Korea digital technology security, hacking or programming
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Fitness girl preparing to do squats on the hack machine in the gym.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Computer screen with code showing error warning symbol and magnifying glass for debugging
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Male criminal wearing mask and hood to hack computer system, breaking into company servers to steal big data. Masked man looking dangerous and scary, impostor creating security malware. Handheld shot.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Lock icon set, collection of icon in editable strokes and flat versions
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Dark Programmer Screen with Hello World Application and Dynamic Syntax Highlighting in Advanced Development Environment.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Growth hack and viral campaign marketing icons, business strategy expansion and social media megaphone promotion, simple black and white vector set
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Falling binary code matrix background. Digital stream of zeros and ones for data, cybersecurity, and technology concept.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Digital binary code matrix background with digits moving across the screen. Data decoding and encoding algorithms in the digital age. Vector illustration.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Cyber Security and Data Protection Solid Icons Set with Shield, Fingerprint, VPN, Firewall, Hacker, Lock and Bug Symbols
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
System hacked alert A computer whose system has been hacked due to a cyber attack on the computer network, therefore, an icon is displayed on the virtual screen.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Collection of outline icons representing various cybersecurity threats, protection measures, and digital risks.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
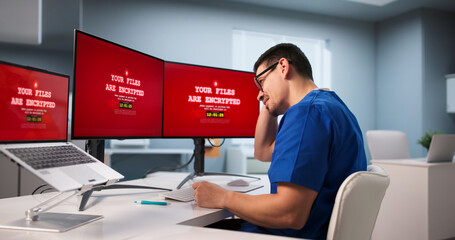
Hospital's Cybersecurity Breached By Malicious Cyber Attack
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Glitch noise static television VFX. Visual video effects stripes background, CRT tv screen no signal glitch effect
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Little child with mobile phone is under cyber attack on internet. Anonymous hacker hacks into boy cellphone and steals data and passwords. Cyber crime,
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Beautiful young african woman making face massage with jade roller
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Hand painted green watercolor background.Set of abstract green watercolor water splash on a white background,Ink paint brush stain. Green splatters spot. Watercolor pastel splash
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Solid black silhouette of a facial jade roller massage tool for skincare routine Vector illustration
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Colorful VHS Glitch Screen Effect. Abstract Technology Background
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
System hacked warning alert. Cyber security on mobile app. Man using mobile phone with warning alert due to fraud, system hacked due to cyber attcak, unknown call
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Glitch background. Abstract screen with noise effect. Failure television and monitor. Technical problem computer. Digital hacking. Warning bug lost connect, disconnection, hack. 3D rendering.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Lock icon web design element. line icon
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Glitch effect with red pixel distortion and code, digital abstract vector background. Cyber punk screen interference with hack attack pattern and grain noise scratch texture, error display
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Online criminals analyzing script codes to hack government system, attacking sensitive sever and causing security breach. People hacking network and stealing information at night.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
AI assists in creating intelligent email security solutions that detect phishing attempts, analyze suspicious messages, and prevent digital threats to protect users and o Parse
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Gamer Signs Triangle Circle Square Plus Banner Background. Geometric Design for Banners, Web Pages, Presentations. Purple Blue Bright Game Background. Vector Illustration.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Polished green jade dollar sign symbol, isolated on transparent background
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
User Receiving a Critical Email Security Alert Danger Notification on a Mobile Phone Warning of Cyber Threat
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
red cyber hack notification alert in green matrix binary data falling with corrupted data lines background banner template
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Digital Cyber Security Network Protection Concept.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Minimalist red data stream glitch effect on white background for technology and cybersecurity concepts
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Dark jade green crystal texture, abstract emerald stone rock background, organic mineral surface, 3d render
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Troubled Graphic Artist Battles Cyber Attack
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
A stream of binary matrix code on the screen. numbers of the computer matrix. The concept of coding, hacker or mining of crypto-currency bitcoin. Vector illustration.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Dark emerald green background with a heavy film grain texture featuring soft organic ripples and flowing leaf-like shadows for moody abstract botanical aesthetic
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
outline cyber icons set - hack, code injection, risk. editable vector for web and mobile ui
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Pro tip bold outline call to action sticker. Professional expert advice. Insider knowledge. Helpful useful hack. Black and white text. Bubble lettering. Playful design word. Ranchers font used
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Chinese cloud set vector collection, auspicious decorative elements, classic Asian curling cloud motifs, cultural artwork patterns, elegant ornamental designs
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
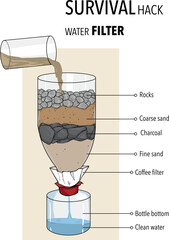
Survival hack water fılter vector illüstration
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Surface of jade stone background or texture.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Lock and Unlock symbol. The padlock shows protect and unprotected status. Cybersecurity and data protection technology. Icon element for app and web. Vector illustration.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Dark royal green gradient seamless pattern with noise texture. Luxury deep turquoise and jade silk bg with soft transitions and effect ombre. Vector gradient mesh illustration.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Abstract red tech background with seamless geometric pattern on black background. Vector realistic illustration of futuristic wallpaper design with convex digital grid, data breach warning display
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Diverse men working together to break security server, planning data breach with malware and trojan virus. Male hackers doing cyberterrorism attack and stealing passwords, phishing.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Cybersecurity threat alert protects data. Cyber security threat alert prevents access, alert warns breach, defends system, and cyber security threat alert identifies risk. Latch
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Abstract background with neon glitch texture, digital tv noise. computer screen damage. 3d rendering.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Zimowa iluminacja świetlna w Krynicy-Zdroju.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Majestic, snow-capped peaks of a prominent mountain range, possibly the Jade Dragon Snow Mountain, standing tall against a clear, vibrant blue sky, showcasing a serene natural landscape.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
data breach icon set collection in solid glyph dual color style. pack contain leak, hack, breach, malware, spyware, intrusion, phishing, ransomware, attack, theft icon
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Stream binary code. Binary code matrix. Background on screen from numbers 0 and 1. Computer matrix. Numbers on screen. Binary code. Graphic data, decryption, algorithm, encryption element.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Cybersecurity Breach Vector. Broken Shield with Lock and Warning Icon.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Dark teal paper texture background with emerald, jade geometric corners gradient layers, copy space for banner presentation
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Concept of cyber attack, system hack, and data breach. Digital security threats, unauthorized access, and sensitive data exposed in online networks.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Collection of green gemstones in various shapes and sizes on dark background emeralds and jade precious stones
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Laptop compromised by ransomware attack with padlocks and chains surrounding it
Do ulubionych favorite_border
Usuń z ulubionych favorite