-
Nephrite (Jadeite, Axestone)
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Hacker security cyber attack smartphone. Digital mobile phone isolated on black. Internet web hack technology. Login and password, cybersecurity banner concept.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Cityscape panorama with security system.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Phuoc An Hoi Quan Pagoda, Ho Chi Minh City, Saigon, Vietnam,
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
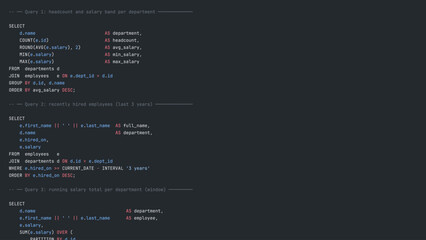
Unsecure and buggy programming code filled with errors and strange logic. Code contains insecure queries, broken validation, weird functions, and programming flaws for demonstration. Latch
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Ransomware Malware Attack And Breach
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Natural texture of a blue-green mineral slice, highlighting the organic patterns and crystal formations
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Text effect jade green glossy
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
jade marble,marble of various colors
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Jade Plant with Dense Succulent Green Leaves in Hanging Basket
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Password hacking ransomwares technology security illustration
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
hacksaw tool icon silhouette vector art illustration
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Plisoviy, plush, satin malachite mineral stone on a white background close-up.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
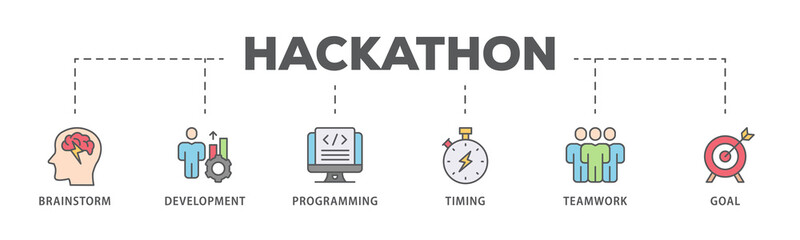
Hackathon banner web icon illustration concept for design sprint-like social coding event with icon of brainstorm, development, programming, timing, speed, teamwork, and goal
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Computer Hacker in Hoodie. Obscured Dark Face. Concept of Hacker Attack, Virus Infected Software, Dark Web and Cyber Security.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
pop style graphic image of hacker on a red background
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Abstract futuristic cyberspace with a hacked array of binary data, broken falling binary code, matrix background with digits, big data neural network, well organized layers
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Majestic, snow-capped peaks of a prominent mountain range, possibly the Jade Dragon Snow Mountain, standing tall against a clear, vibrant blue sky, showcasing a serene natural landscape.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Futuristic blue digital data vortex with glowing circular HUD interface, cyber technology network background with streaming particles
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Security icons depicting locks shields and surveillance a black silhouette
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Botnet icon set. Stealing Data, Robot, Spam, Server, Malware, Cyber Security, Devices, Internet. Duotone color solid and editable outline icons
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Man holding glowing cyber security shield guard blue. Digital cybersecurity and protection concept. Data security system, Anti hack defense, Preventing data theft, Malware and Virus attack protection
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
abstract damaged shape seamless pattern on jade green color
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Modern Developer Programmer Screen with Computer Programming Language Code with Color Syntax Highlighting. Vector Illustration.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Email phishing icon collection. Vector design pack
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Digital Shield Protects Against Cyber Attack Threat.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Masked male individual works on laptop at night, attempting to breach corporate systems. Anonymous hooded man appears to hack software company, representing cybercrime and digital security threats.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Colorful VHS Glitch Screen Effect. Abstract Technology Vector Background in Retro Style
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
phishing alert banner web icon vector illustration featuring icons of fake email, suspicious link, warning shield, hacked account, spam message.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Neolithic jade bi disc artifact displayed in close-up under museum lighting
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Woman recording beauty tutorial using jade roller for social media
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
64luxurious light green onyx marble texture background with soft white mineral veins organic mineral patterns, creating a sophisticated and calming aesthetic.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Hibiscus and Jade Plant in Terracotta Pots Cartoon Vector Illustration Isolated on White Background
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Cyber security breach, system hack warning concept with locked data and login interface on smartphone. Ideal for cyber attack, data protection, online security, hacking risk, digital privacy visuals.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Abstract bubbles overlap, creating vibrant green, blue hues. Soft gradients suggest depth, light interplay. Minimalist design, modern aesthetic.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Hacker icon with editable stroke eps 10 vector illustration. Outline drawing.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
A comprehensive set of modern cybersecurity and digital protection line icons for online safety concepts
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Collection of colorful security icons representing various lock concepts and cybersecurity elements in a grid layout
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Konie, konie na pastwisku konie na padoku, konie w górach
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Cybersecurity, data protection, cloud computing, online safety, internet risks, digital troubleshooting. Warning sign near a browser URL bar with question mark and cloud icon. Cybersecurity and data
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Phone Scammers, mysterious man with phone, cyber theft and fraud, mobile phone used for hacking, secret attacks on privacy.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Technology, Internet, business and network concept. Privacy alert.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Active and mobile lifestyle, sports as hobby and way of life. Female sports club visitor exercises on hack squat machine. Client performs exercises, combines dynamic and static loads on body.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Modern Developer Programmer Screen with Database SQL Programming Language Code with Color Syntax Highlighting. Vector Illustration.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Data security data protection business technology privacy concept. Hi tech motion graphic technology. digital interface on cyan color background. and 3d illustration
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Skin care products in the bathroom. Face cream, serum bottle, jade roller and stack of towels.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Abstract green bokeh background with soft light circles and blurred texture in various shades.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Lock icons vector. Line and glyph design with editable stroke
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
phishing alert banner web icon vector illustration featuring icons of fake email, suspicious link, warning shield, hacked account, spam message.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Man using mobile banking security breach alert on smartphone screen, system hack warning, phishing email risk, cyber attack on financial data, online fraud protection and cybersecurity threat concept
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Woman recording beauty tutorial using jade roller for social media
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
A small jade plant in a red decorative pot on a white rooftop wall overlooking the city.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Flat Vector Set of Hibiscus Flower Plant and Jade Succulent in Terracotta Pots Isolated on White
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
collection of black silhouette of various axes with different designs
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Cyber security alert with smartphone and warning lock icon showing system hack attack, data protection risk, mobile privacy threat and online security vulnerability concept in digital technology era.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Cyber Security and Data Protection Solid Icons Set with Shield, Fingerprint, VPN, Firewall, Hacker, Lock and Bug Symbols
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
vibrant mint green marble surface featuring organic dark green veining for luxury branding, web backgrounds, interior design mockups
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Set of breach icon collection in multiple style. Icon suitable for web and mobile application
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
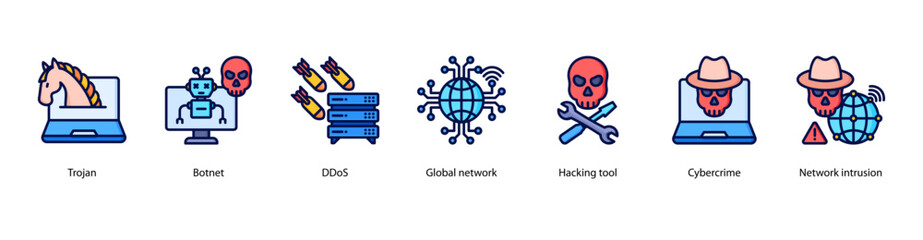
Cybercrime Attacks web banner illustration featuring Trojan, Botnet, DDoS, Global network, Hacking tool, Cybercrime, and Network intrusion.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Set of three stylized teal green leaf icons in different minimalist designs perfect for nature, ecology, and wellness branding
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Abstract green light streaks form dynamic pattern. Dark background enhances bright geometric shapes, creating modern visual effect.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Dense Red Binary Array - Repeating Code Fragments on Dark Background
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Purple abstract pixel texture bg video screen. Tv pattern background with square noise effect. Futuristic broadcast neon gradient banner for television. Modern vhs led static display element
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Critical Error Warning Message Windows. Vintage User Interface Operating System Fail. Vector Illustration.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Cyber security data protection business technology privacy concept. glowing animation. digital interface on cyan color background. and 3d illustration
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Droplets of crude on fishing hook in transparent form polygon. Oil trap as bait from War Crisis. Banner vector with copy space for text. Vector EPS10.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Concept of cybersecurity. Protection shield symbol inside a transparent sphere shield with a hexagon pattern on digital glowing background. Personal data protection and phishing. vector illustration.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Cybersecurity Shield Lock Digital Protection Icon.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Vector streaming binary code yellow background. Data and technology, decryption and encryption, computer background numbers 1,0. Coding or Hacker concept. Vector illustration. eps 10
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Konie, konie na pastwisku konie na padoku, konie w górach
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Woman recording beauty tutorial using jade roller for social media
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
PENETRATION TEST inscription, cyber security concept. 3d illustration
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Isolated green jade plant in blue pot, houseplant, nature botanical, garden, fresh, eco, trendy
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Cybersecurity alert warning showing red cyber for data breach, network threat, and cyber security system vulnerability with emphasis on security risk, caution, digital protection Marrow
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Manager supervising server farm admins alerted by hack warning, securing systems from cyberattack accessing confidential data. Teamworking data center colleagues defending rigs during security breach
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Lock icon. Premium thin line vector illustrator. Vector EPS10
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Lock icon vector. EPS 10 editable vector bundle
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Comprehensive line icons for cybersecurity protocols login access and identity verification
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Cute Cartoon Indoor Plant Duo Vector with Hibiscus Blossom and Jade Succulent in Terracotta Pots
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Security and protection icon set flat design vector illustration scalable graphic art isolated on white
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Abstract green background. Flowing lines create dynamic visual effect. Modern design elements suggest energy, motion, technology.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Fractured Binary Matrix - Irregular Code Intrusion on Dark Field
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
A layered abstract image about digital security
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Modern Developer Programmer Screen with Computer Programming Language Code with Color Syntax Highlighting. Vector Illustration.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Crispy fried pork floss, white jade mushrooms, and enoki mushrooms
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Technology stream binary code. Digital illustration. White matrix background. Programming, coding, hacking and encryption.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Green jade dumpling gyoza spinach dough, Jade colored dumpling creative fusion dim sum, Steamed green dumpling vibrant
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Positive elderly woman in great shape using hack squat machine in busy gym, showing healthy aging, mobility, and active lifestyle
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Global malware rise alert with a megaphone and a virus.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
phishing alert banner web icon vector illustration featuring icons of fake email, suspicious link, warning shield, hacked account, spam message.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Woman enjoying self-care routine with jade roller and eye patches
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Business data privacy infographic icon flow process which consists of Privacy Policy Development, Data Privacy Compliance, Privacy Monitoring, Privacy Adjustment
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Cybercrime Attacks web banner illustration featuring Trojan, Botnet, DDoS, Global network, Hacking tool, Cybercrime, and Network intrusion.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Diverse hands collaborate on gears while a digital alert displays a system hack warning. This image symbolizes the importance of teamwork in tackling cybersecurity threats. Trope
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Lock icon simple outline style. Editable stroke EPS 10
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Digital tunnel with particles
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Glitch VHS grunge texture with pixel noise. Retro analog video error background design.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
A jade ribbon butterfly (Papilio polytes) is gathering nectar among the flowers in the park.
Do ulubionych favorite_border
Usuń z ulubionych favorite