-
Manager supervising server farm admins alerted by hack warning, securing systems from cyberattack accessing confidential data. Teamworking data center colleagues defending rigs during security breach
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Lock icon. Premium thin line vector illustrator. Vector EPS10
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
abstract damaged shape seamless pattern on jade green color
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Woman enjoying self-care routine with jade roller and eye patches
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Digital Software Development Background Featuring Hello World Code in Next-Generation Programming Language with Structured Editor Interface.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Set of minimalist line art characters including senior citizens and young adults using smartphones to search for information and feeling confused or worried in daily life
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Indoor Cactus and Succulent Houseplant Collection with Potted Desert Plants, Aloe Vera, Prickly Pear, Jade Plant and Decorative Botanical Vector Illustration Set
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Purple abstract pixel texture bg video screen. Tv pattern background with square noise effect. Futuristic broadcast neon gradient banner for television. Modern vhs led static display element
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Cybersecurity alert warning showing red cyber for data breach, network threat, and cyber security system vulnerability with emphasis on security risk, caution, digital protection Marrow
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Droplets of crude on fishing hook in transparent form polygon. Oil trap as bait from War Crisis. Banner vector with copy space for text. Vector EPS10.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Cyber security data protection business technology privacy concept. glowing animation. digital interface on cyan color background. and 3d illustration
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Lock icon style design pack on white background. Thin line and clipart style
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Cybersecurity Alert: A dynamic collection of warning signs and alerts, embodying the essence of digital security and network protection.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
phishing alert banner web icon vector illustration featuring icons of fake email, suspicious link, warning shield, hacked account, spam message.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Cyber security alert with smartphone and warning lock icon showing system hack attack, data protection risk, mobile privacy threat and online security vulnerability concept in digital technology era.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Hacker icon. Simple high quality pictogram. Modern solid style
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Laptop with e-wallet and hacker with big magnet attack computer. Theft of money from electronic accounts.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Abstract geometric shapes overlap, creating dynamic blue, green gradient. Modern design suitable for backgrounds, banners, presentations.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
rose quartz facial roller and massage stone gua sha isolated on white background, flat lay
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Concept of hacker attack, fraud investigation, internet phishing attack, evil win, personal privacy data, hacking and stealing email and money with tiny people. Vector illustration in flat design
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
massage stone jade gouache scraper light background.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Digital security concept with bank building shield and padlock.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Glitch abstract background with distortion effect, bright dynamic strokes, blue and red color lines for design concepts, wallpapers, presentations, posters, prints and web. Vector illustration.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Modern Developer Programmer Screen with Computer Programming Language Code with Color Syntax Highlighting. Vector Illustration.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Programming code abstract screen of software developer. Computer script
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Digital Binary Code on Dark Red Background. Hacking
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Spa background with jade roller and massage natural oil
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Computer Hacker in Hoodie. Obscured Dark Face. Concept of Hacker Attack, Virus Infected Software, Dark Web and Cyber Security.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
piękne konie na łące, pastwisko i ogrodzenie
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Butterstone butter jade stone yellow and green tones on wooden underground
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Jade Dragon Snow Mountain
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
digital shield with padlock symbol on blue background. cyber security and personal data privacy protection
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Cyber security protects against breaches, hacks, and network attacks using strong infrastructure and proactive digital defense strategies. Vouch
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Technology background. Big data concept. Binary computer code. Vector illustration.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
pop style graphic image of hacker on a red background
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Interior View With Statues Of Jade Emperor Pagoda In District 1 Of Ho Chi Minh City, Vietnam. This Pagoda Was Built In 1892 By Chinese And Very Famous In Ho Chi Minh City.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
greenstone industrial jewelery
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Fingerprint scanning concept
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
konie arabskie, klacz ze źrebięciem
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Secure internet access and personal information security. PROTECT YOUR PASSWORD. 3d illustration
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Security Breach Icon Set With Multiple Style Collection
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Beautiful happy young woman 20s in bra use jade face roller with natural quartz stones do massage reflected in mirror in bathroom do morning routine Skin care healthcare cosmetic procedures concept
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Modern Developer Programmer Screen with Computer Programming Language Code with Color Syntax Highlighting. Vector Illustration.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Panoramic web banner of Fingerprint scan provides security access with biometrics identification.Futuristic Technology in Cyber security and data protection,RPA,5g,big data,iot,vr,mixed virtual.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Woman recording beauty tutorial using jade roller for social media
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Mint, grey, and gold stone marble texture. Alcohol ink technique abstract vector background. Modern paint in natural colors with glitter. Template for banner, poster design. Fluid art painting
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Suspicious Smoke Rises From Power Plant
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Grupa pięknych szlachetnych koni na jesiennym pastwisku
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Portrait of man looking at camera with beard using jade roller while massaging face isolated on grey background with copy space. Skin care treatment. Beauty
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Fluid Art. Liquid dark turquoise abstract drips and wave. Marble effect background or texture
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Crispy fried pork floss, white jade mushrooms, and enoki mushrooms
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Cybersecurity protects digital systems from hackers with IT security, attack prevention, and risk management for safe online operations. Latch
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Protection concept. Protect mechanism, system privacy.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Green jade Rare and expensive For making jewelry
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Lock icon - editable stroke vector illustration eps10.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Hacker using keyboard on dark background
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Abstract green background. Bright lines intersect, creating dynamic visual effect. Modern design elements present. Simple, elegant composition.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Green jade is a beautiful mineral that symbolizes harmony and prosperity.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Hacker inserting USB in computer after managing to steal sensitive data, close up. Scammer uploading storage drive into PC after obtaining sensitive information from users using malware, camera A
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Software source code. Programming code. Programming code on computer screen. Developer working on program codes in office. Source code
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
elder woman granny is using gua sha and jade roller for facial massage. anti wrinkle aging,rejuvenation procedures. portrait of old lady, with headband on head and mirror in hand.beauty skin care
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Closeup shot of a historic jade vase relic in China
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Epipremnum aureum Pearls and Jade Pothos on wooden table
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
jade vine rarest plant in the world
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Green foil metallic wall with glowing shiny light, abstract texture background
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
hacker doing a crypto scam or phishing
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
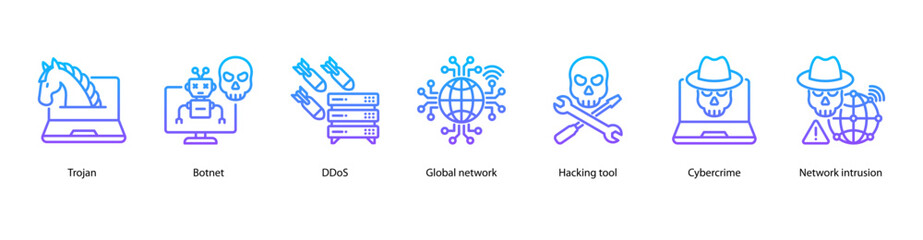
Cybercrime Attacks web banner illustration featuring Trojan, Botnet, DDoS, Global network, Hacking tool, Cybercrime, and Network intrusion.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Craftsman carving jade stone with a water cooled diamond dremel in Beijing China
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
The Jade Emperor statue in Hat Yai, Thailand
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Mobile Security protection, cybersecurity expert using virtual laptop of Mobile Security system on structure smartphone encryption threat detection data privacy platform. Secure access control.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
artificial intelligence filled icons set. editable glyph icons such as streaming, woofers, network hub, synchronizing, wireless keyboard, domotics, passkey, user protection vector.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Defense business related icons set. Including cybersecurity, shield, firewall, lock, encryption, antivirus, data protection, and prevention. Editable stroke. outline icons.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Crassula ovata jade plant isolated on white background
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Cybercrime concepts The hacker's hand is holding a credit card with a blurry computer background. Stolen data and use it for payments and shopping on laptop.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Close-up hacker hands working on laptop, selecting password, access granted
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Web browser window with virus detection alert on laptop screen. Internet threat warning. Concept of malware, ransomware, hacking, or cybercrime. Dangerous website. Flat technology vector illustration.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Programming Coding modern icon set. Contains such icons as development, web, coding, develop, program and more. Program modern icon set. Minimalist icons collection. Editable vector illustration.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Tropical flowers, the Strongylodon Macrobotrys emerald turquoise Jade Vine inside a greenhouse in Hiroshima in Japan. Ornamental plant with greenish-blue claw-shaped flowers.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
cyber security technology protection key lock data information blue background. vector illustration fantastic technology.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Gua Sha massager isolated from background, green jade stone for face and body care.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Cyber attack hacker concept. Internet web hack technology. Digital laptop in hacker man hand isolated on black. Data protection, secured internet access, cybersecurity banner.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
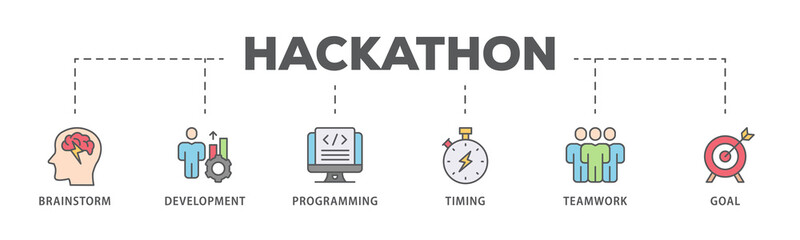
Hackathon banner web icon illustration concept for design sprint-like social coding event with icon of brainstorm, development, programming, timing, speed, teamwork, and goal
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
3D Isometric Flat Vector Illustration of Computer Crime, Cyber Security Breach. Item 4
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Suspicious Email Link Detected, Cybersecurity Warning, digital warning interface, phishing email and a suspicious link detection alert. Concept for cybersecurity, email threats, phishing prevention
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Chinese translation: Happy Mid Autumn Festival banner with mooncakes, jade rabbits, flowers, moon, clouds. Traditional holiday in Taiwan, Japan, Korea, Vietnam. Oriental greeting bg. 3D illustration
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Black glitch background with pixelated noise effect. Vector realistic illustration of abstract video rewind pattern on damaged screen background, retro tv display, signal distortion, hacker attack
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Internet line icons set with Security, Business, Cyberspace, Mail, Password, AI, Network, Notebook, Cloud, Server and more. Editable Stroke
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Hands operating a laptop with a vigilant eye on a hacker's silhouette in the background, illustrating the battle against cyberattacks. Hacker Defense
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Glitched silhouette, bitmap effect, error signal, technical problem. Hacked system or cyber attack. Vector illustration.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Surprised woman points finger up as she finds amazing idea online. Happy lady in curlers and face mask sitting on sofa, browsing Internet blog on laptop and learning good life hacks and practical tips
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Life Hacks Blue Lines Blob Rounded Square Black Background Text
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Set of vector hand-drawn illustrations. Abstract shapes in pastel color, linear drawing. Space for text, template, frame. Sheet mask, cream packaging, jade facial massager. Skincare, beauty routine
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
A green jade for making ornaments on the ground.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
adware attack concept with alert notification of phishing advertisement on laptop screen, vector flat illustration
Do ulubionych favorite_border
Usuń z ulubionych favorite