-
Vector isolated cartoon illustration of home potted succulent jade bonsai plant.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Skin care beauty concept with face roller on green background
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Rough natural green tone color paint on blank eco environmental friendly cardboard box paper texture background with space minimal style
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
PENETRATION TEST inscription, cyber security concept. 3d illustration
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Beautiful african woman smiling and massaging face skin with jade roller isolated on yellow
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Cosmetic skin care products, jade stone face massager, creams, gel and oil. Roller massage of the face. Flat lay, top view
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
gift box with rose quartz jade roller and stone on pastel pink background with festive lights
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Guasha Face Sculpting Technique with Jade Stone in Beauty Salon
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Binary code background. Falling, streaming binary code background. Digital technology wallpaper
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Trendy Halftone Collage Protect your personal data. Two Hands with key and laptop. Protecting computer from hacker attacks. Metaphor illustration. Digital security. Vector contemporary art
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Grunge HACKED round stamp seals isolated on a white background. Round seals with grunge texture in red and blue colors. Vector rubber overlay of HACKED label inside circle form with stripes.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
konie arabskie, klacz ze źrebięciem
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Ethical Hacking icon set. Includes symbols for hacker, fraud, security, crime, hack, cyber and more. Hacking linear icon. Icons for UI design. Outline and solid pictogram.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Presentation background vector design Banner background design with circle, arrow, square, stroke Dotted pattern background with jade colour
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Houseplant Crassula jade plant money tree in white pot in home - home gardening concept
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Young sly man trying to breach the system while giving bad commands on laptop in empty dark office
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Glitching computer screen, glitch programming code. Virtual environment, programm function failure and data loss, critical code mistake, hacker attack or hardware malfunction concept vector background
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
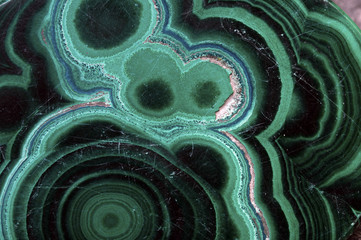
collection of various Jade natural mineral gem stones and samples of rock isolated on white background
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
3D rendering. Abstract background concept of cyber security and attack, system crash.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Green Burmese Imperial Jade Ring. And art background
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Epipremnum aureum Pearls and Jade Pothos on wooden table
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Padlock Security cyber digital concept Abstract technology background protect system innovation vector illustration
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Data breach banner web icon vector illustration concept with icon of computer, security, attack, hacker, algorithm, access, digital and confidence
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Abstract digital cloud skull on blue background. Cloud computing, hacking and data theft concept. 3D Rendering.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Binary Code backgrounds, a sequence of zero and one number on a blue background. Numbers of the computer matrix. The concept of coding and cybersecurity
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Massage set "Guasha" jade green, roller and scraper on the white background
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Galop, wyspa Olchon, jezioro Bajkał, Syberia, Rosja
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Wanted Hacker is Coding Virus Ransomware Using Abstract Binary Code. Cyberattack, System Breaking and Malware Concept.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Abstract Technology Machine Code Background. Random Binary Hexadecimal Code. Matrix with Digits. Vector Illustration. Hacking, Cryptography, Malware, Reverse Engineering.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Set of checkmarks on green shield and cross on red shield icon. Accepted and unaccepted security. Protection guarantee and safety shield. Minimalist cartoon icon. Trendy and modern vector in 3d style.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Cyber crime and internet privacy hacking. Network security, Cyber attack, Computer Virus, Ransomware and Malware Concept. 3d illustration
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
jade jewelry, jade stone, jade, green jade, gemstone, leaves, water, white, nature, green
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Fluid Art. Liquid Velvet Jade green abstract drips and wave. Marble effect background or texture
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Skin care concept with green face roller on white background
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Padlock of Cyber Security Digital Data, Technology Global Network Digital Data Protection, Future Background Concept. 3D Rendering
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Krajobraz wiejski Podlasia. Konie na łące, Podlasie, Polska
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Blue glowing binary code rain background. Futuristic matrix style with data stream, abstract computer system, digital tech effect and cyber security information pattern. Vector illustration
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Set of retrofuturistic posters for hackathon (also known as a hack day, hackfest, datathon or codefest) event with set of 1-bit pixel art illustrations of human heads and glitched elements.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Rose Quartz jade roller and Gua Sha massager on white towel. Massage tool for facial skin care, SPA beauty treatment concept
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Futuristic Glitch background. Abstract pixel noise glitch error video damage like Vhs glitch. Pattern for wallpaper design. Screen error effect. Abstract background. Medical background. Cosmic
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Celadon ceramic dishes , Thai Celadon on white background
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Laptop with e-wallet and hacker with big magnet attack computer. Theft of money from electronic accounts.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Jade Buddha Temple, Shanghai, China
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
AI monitors network to issue real-time alerts for cybersecurity incidents. Alert warning showing red cyber for data breach, network threat, emphasis on security risk, caution, digital protection Vouch
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
skull in the digital matrix on the BCD stream on the screen. computer matrix numbers.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
rose quartz facial roller and massage stone gua sha isolated on white background, flat lay
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Green onyx necklace, agate (layered chalcedony), and jade beads on an grey natural background. Onyx stone is powerful energy talisman. Retro composition.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Anonymous hacker and face mask with smartphone in hand. Man in black hood shirt trying to hack personal data from mobile phone. Represent cyber crime data hacking or personal data stealing concept.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Life hacks - gears concept - 3D illustration
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
klacz konia arabskiego na zbliżeniu
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
hacker attack , cyber threat risk management , malware and virus prevention , security awareness
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Russia digital technology flag
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Worried surprised elderly woman holding card, look at smartphone, feels stressed, bad online bank service, overspending, bankruptcy risk, hacked virtual wallet, theft, money steal, crime, e-bank fraud
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Abstract virtual code skull hologram on US flag and skyline background, cybercrime and hacking concept. Multiexposure
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Illustration vector isolated of chinese gods, chinese mythology, jade emperor, sky god
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Cybersecurity cybercrime internet scam business, Cyber security platform privacy protection 3D AI robot safety icon, computer virus attack defense, identity privacy data hacking protection firewall
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
hooded hacker solar winds hack concept
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
hacker at work with graphic user interface around
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Beautiful abstract color yellow and green marble on black background and gray and green granite tiles.Polygonal Mosaic Background with terrazzo flooring.Radient 4k hd high resolution stripes polygon
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Lijiang, China, watch the Lijiang performance and climb the jade dragon mountain
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Imperial green jadeite jade Guan Yin (Avalokitesvara) and Smiling Buddha pendant. Beautiful Chinese style Burmese jadeite jade jewelry
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Laptop Bug solid glyph icon
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Cyber security destroyed. Padlock red opens on code connection dark red background.Cyber attack and Information leak concept.Vector illustration.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Jade roller and gua sha stone massager at pastel background. Anti-aging therapy. Top view.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Life hack written on tablet in office as flatlay
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Life Hacks, message on note paper, computer and coffee on table, 3D rendering
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
stop theft. thief inside stop icon. business metaphor for stop cyber criminal movement vector illustration
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Virus warning alert on computer screen detected modish cyber threat , hacker, computer virus and malware
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Man doing machine hack squat exercise. Flat vector illustration isolated on white background
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
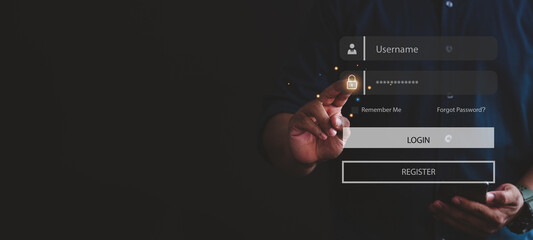
you have been hacked. Vector hacker icon or pictogram. Keylogger, cyber security concept. Technology data. Hybrid, and warfare, DDoS attack. Cyber war. Hackers, criminals. login and password. Digital
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Amazed African employee read news seated at desk
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Abstract virtual binary code illustration on flag of China and blurry skyscrapers background. Big data and coding concept. Multiexposure
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Businessman protecting data personal information. Cyber security data concept. Padlock and internet technology.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Stadnina koni / Kaszuby / pomorskie / Polska
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Technicians in AI server hub panicked by hacking attempt stealing sensitive company data. Team of data center IT experts fighting computer virus triggered by security systems, camera A
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
OTP phishing hacking online. Computer data fishing hack crime. Scam concept
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Pretty woman massaging face with jade roller and looking at round cosmetic mirror in bathroom
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Uncooked Jade Rice in a Measuring Cup
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Cyber background constructed with different symbols. Digital futuristic backdrop. Abstract visualization of programming. Vector illustration.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Business with laptop computers protected The idea is to hack phishing cell phones with passwords to gain access to online security and fraud risks.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Smiling senior woman massaging her face with a jade roller while looking in the mirror
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Jade : Green jade (jadite) scupture in cubbage shaped, symbol of wealthy, rich, treasure and lucky in Chinese traditional culture. Jade isolated on white background.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Hacker security cyber attack smartphone. Digital mobile phone isolated on black. Internet web hack technology. Login and password, cybersecurity banner concept.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Cute Colorful Typography Lettering productivity hacks
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Young insighted smart proactive woman of African American ethnicity she wear blue shirt casual clothes holding index finger up with great new idea isolated on plain pink background. Lifestyle concept.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Hand painted watercolor background. Black blue green modern abstract art background. Dark turquoise aquarelle background with copy space for design. Web banner.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Email security system identifies phishing attempts, detects suspicious messages, and protects users from data theft and malware through intelligent monitoring and alerts. Parse
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Tea Bag Aroma Life Hack For Smelly Shoes
Do ulubionych favorite_border
Usuń z ulubionych favorite