-
greenstone industrial jewelery
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Emerald paper texture background with olive green semicircle and copy space for banner, presentation, template
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
fishing hacker icon set multi concept
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Modern Programmer Coding Screen with Hello World Program with Modern Programming Language Syntax Highlighting in Digital Code Editor Environment. Vector Illustration.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Broken Padlocks: Blue and Yellow Security Breach Illustration.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Crassula ovata, jade plant close-up. House plant in pot on the table by the window. Lush, fresh green leaves of houseplant. Succulent in home garden.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Fraud Detection icons set multiple style collection. Editable stroke
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Green jade face roller, natural stone for skin care, on white backdrop. Tool for facial lifting massage, trendy therapy
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Green matrix background. Falling numbers on screen. Technology stream binary code. Digital vector illustration. Hacking concept.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Real jade That is the original jade ball Green and rare, expensive
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Gold mountain background vector. Mid century landscape art with sun and moon, Sea and Ocean. Modern contemporary art design for acrylic canvas , digital Prints, wallpaper, Poster, metal poster prints
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Beauty treatment. Attractive young women looking at camera, using jade roller and facial gua sha while posing together isolated over beige background
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Businesswoman uses laptop with computer network notifications data breach.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Malware concept. Concept of virus, piracy, hacking and security. Website banner of e-mail protection, anti-malware software. Computer Viruses Attack, Errors detected, Warning signs, Stealing data.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Abstract blue background from jade surface.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Purple abstract pixel texture bg video screen. Tv pattern background with square noise effect. Futuristic broadcast neon gradient banner for television. Modern vhs led static display element
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Green white marble wall surface gray pattern graphic abstract light elegant for do floor plan ceramic counter texture tile silver background.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
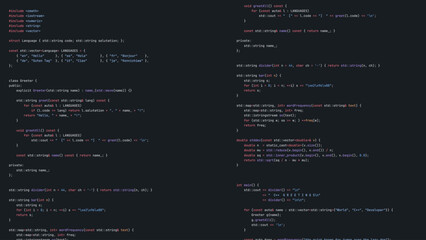
Unsecure and buggy programming code filled with errors and strange logic. Code contains insecure queries, broken validation, weird functions, and programming flaws for demonstration. Latch
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
3D Illustration of orange purple digital glitch and hex code on black background. Cyber pattern in digital matrix wallpaper texture concept as a neon sci fi effect and data flow scheme.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
.Big financial data theft concept. Anonymous Panorama Hackers Are Hacking Highly Protected Financial Data Through Computers
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
White paper texture background with emerald, teal geometric corners gradient layers, copy space for banner presentation
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
hacker cash money icon set multi concept
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Professional Code Editor Interface Featuring Hello World Script with Contemporary Programming Syntax Highlighting. Innovative Software Development Background.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Cybersecurity Icons Set Digital Security Protection Data Privacy.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Konie Na Wybiegu Ze Stajnią z Cegły w Tle
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Blue Binary Data Software Programming Code Background. Random Parts of Program Code. Digital Data Technology Concept. 1 0 Machine Code. Random Binary Data Matrix Wide Vector Illustration.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Modern Vector streaming binary code red background. Data and technology, decryption and encryption. background illustration
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Facial massage kit - amethyst and jade gua sha face rollers on stone concrete background. Natural stone face massager, skin care concept
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Concept of cyber crime and cyber security. Hand using laptop and show malware screen with phishing email, hack password and personal data. hackers, Virus Trojans, Encription Spyware or Malware.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Woman using jade roller on cheeks
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Data Security system concept, Businessman use mobile phone with text hacked and security icon screen, innovation technology, cloud computing, internet network communication
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Hand holding of a green jade ring on a black background
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Cybercrime email Spam concept. E-mail Popup Warning Window: The computer shows a malware screen that comes with email, hack passwords from bank accounts, and personal data cybersecurity
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Bored Teenage Girl Being Told Off By Mother
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Purple abstract pixel texture bg video screen. Tv pattern background with square noise effect. Futuristic broadcast neon gradient banner for television. Modern vhs led static display element
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Asian woman using jade roller for skincare facial routine
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
AI strengthens cyber security with artificial intelligence threat detection, AI-based protection layers, and virtual assistant alerts against breaches. Kernel
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Facial Jade Roller Icon Set - Beauty Massage Tool Symbol for Skincare and Wellness Routine
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
cybersecurity for business managed the document privacy to protection online data by lock icon virtual screen technology.protecting personal data on laptops interfaces prevent mail from scammer hacker
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Cyber security concept, databases, big data, internet server, cloud storage and virtual networks. Isometric server room under the protection. The server room is protected by an antivirus cheat. Vector
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Hand holding a saw with a black handle isolated on white background
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Cyborg hand protection Privacy server from hacker.Data security protection interface used by robot.Cyber Digital security,Smart system and web security Data Business Technology concept.3D rendering
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Technology matrix background. Cyber security with falling numbers on screen. Vector binary code. Digital system. Decoding data. Hacked concept.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Set of luxury skin care cosmetics. Flat lay black face roller, jar or moisturizer cream, gua sha, essential oil, serum on stone table.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Digital database cyberspace. Flow of colored particles. Decoding algorithms hacked software. Futuristic digital background. 3d rendering.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Abstract Vector streaming binary code red background. Data and technology, decryption and encryption. vector design
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
close up of portulacaria afra, elephant bush or dwarf jade plant, with rain drops
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Green jade roller and gua sha stone for facial massage and isolated on transparent background. Facial massage tool. Green quartz jade roller
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Hacker using the Internet hacked abstract computer server, database, network storage, firewall, social network account, theft of data
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Digital illustration with a blue background depicting a lock in the center, surrounded by gears, circuits and binary code. Ideal for cybersecurity and data protection topics.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Spam SMS fake phishing message from scammer concept. Red alert hack system, email hack.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
System hacked alert after cyber attack on computer network. compromised information concept. internet virus cyber security and cybercrime.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Fraud icons. Abstract digital hacker icon set in futuristic glowing dots style. Skull, bag, unlock, data server, broken shield, and bank card with red glitch dangerous particles. Vector illustration.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Jade pendant isolate on black background. Icy blue Burmese jadeite Jade carving with Happy Buddha, longevity peace, lucky bird, Chinese coins, ruyi, peony and pearls. Rare color jadeite jade
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Purple abstract pixel texture bg video screen. Tv pattern background with square noise effect. Futuristic broadcast neon gradient banner for television. Modern vhs led static display element
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Black hood hacker force demands ransom by holding out his hand on table where sensitive data is hacked in a dark room in the background. Cyber security and cyber crime concept. Hacking and phishing
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
AI strengthens cyber security with artificial intelligence threat detection, AI-based protection layers, and virtual assistant alerts against breaches. Kernel
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Concept of hacker attack, fraud investigation, internet phishing attack, evil win, personal privacy data, hacking and stealing email and money with tiny people. Vector illustration in flat design
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Green Marble Liquid Texture Pattern Abstract High Quality Background
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Cybersecurity network defense grid background, dark honeycomb with red alert nodes. Tech backgrounds for SOC reports, firewall sites. Cybersecurity visuals for security teams. Vector illustration
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Hacker accessing sensitive information on laptop surrounded by warning signs and malware symbols in a digital environment
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Blue Binary Data Software Programming Code Background. Random Parts of Program Code. Digital Data Technology Concept. 1 0 Machine Code. Random Binary Data Matrix Wide Vector Illustration.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Horizontal scanlines glitch effect overlay, VHS screen lines, TV static interference pattern. Retro CRT monitor noise texture isolated on white. Motion blur speed stripes for video transition effects.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Ransomware malware attack and data breach. Businessperson using laptop with spam virus on warning caution for notification on internet security protect.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Professional software engineer working on cybersecurity with shield hologram and AI assistant on computer screen. Concept of data protection, network security, and digital innovation.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Portulacaria afra, known as elephant bush, dwarf jade plant, porkbush and spekboom
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
2plus3blog Kozia Góra Szyndzielnia Bielsko Biała Bystra
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Ransomware Cyber Attack Using Malware
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Pixel bitmap texture pattern. Geometric pixel pattern. Abstract bitmap retro design. Vector illustration
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
cybercrime, hacking and technology crime - male hacker in dark room using laptop computer for cyber attack
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Brücke - Stadtpark - Zossen Brandenburg - Deutschland - Bridge in a Green Woodland - High quality photo
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Notification virus access on the computer system, prevention of malware infection on the computer, notification of the computer when a virus is detected on the Internet, computer virus removal.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Hacking and cryptocurrency concept
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Purple abstract pixel texture bg video screen. Tv pattern background with square noise effect. Futuristic broadcast neon gradient banner for television. Modern vhs led static display element
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
System information message. Installation process. Vector Illustration.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Unsecure and buggy programming code filled with errors and strange logic. Code contains insecure queries, broken validation, weird functions, and programming flaws for demonstration. Vouch
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Indoor potted jade plant illustration
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
white digital matrix of binary code numbers background
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Simple lock icon on white and blue backgrounds security concept.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Jade roller and facial massage tool doodle icons. Skincare treatment set.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Design Vector streaming binary code red background. Data and technology, decryption and encryption. vector illustration art
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
compromised election or foreign hackers nterference concept
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Cyber security hacker smartphone. Internet web hack technology. Digital mobile phone in hacker man hand isolated on black banner. Data protection, secured internet access, cybersecurity.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Digital yellow pixel pattern background with glowing squares - cyber grid for game interface, tech wallpaper, streaming overlay and futuristic design project with neon mosaic texture on dark surface.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Hacker hacked remote server or datacenter. Anonymous steals passwords, data or money. Hacker attack on cloud storage. Cyber security, crime on internet. Unreliable security system.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Woman sitting on couch reading message on computer feels shocked
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Ransomware Cyber Attack Showing Personal Files Encrypted
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Woman doing self massage with rose quartz face roller
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
2d illustration abstract binary skull
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Creative abstract binary code hologram and hand with mobile phone on background, AI and machine learning concept. Multiexposure
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Infecting a laptop with a Computer Virus via usb stick, free copy space
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Golden bitcoin cryptocurrency on computer circuit board
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Close up of hacker hands using laptop with glowing forex index chart with grid on dark background. Market, finance and online trading concept.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Conceptual hand writing showing Life Hacks. Business photo text Strategy technique to analysisage daily activities more efficiently.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Australia Circular Flag with Cyber Attack Titles - 3D Illustration
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Unsecure and buggy programming code filled with errors and strange logic. Code contains insecure queries, broken validation, weird functions, and programming flaws for demonstration. Latch
Do ulubionych favorite_border
Usuń z ulubionych favorite