-
Grunge red security notice word square rubber seal stamp on whtie background
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
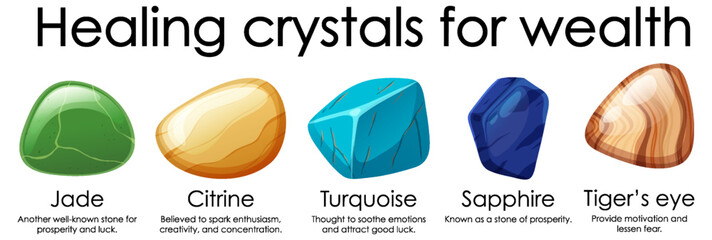
Healing crystals for wealth collection
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Abstract Technology Binary Code Dark Red Background. Cyber Alert
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Hand cleans red shoes with a toothbrush. life hack for the care of suede.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Client with her eyes closed receiving a facial massage with jade roller in the spa salon. Massage cabinet in the professional beauty clinic. Girl facial
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Aging process - old senior woman hands wrinkled skin
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Emerald Green Peridot or jade Earrings
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Cybersecurity logo icon set with shield, padlock, biometric ID, network protection. Digital defense symbols for secure data, AI systems, cloud, antivirus, and privacy tech. Vector illustration.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Hand and warning caution 404 page not found error system or problem computer network or firewall protection for cyber threat attack security risk alert hacker or cybercrime safety or virus prevent.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Warning, power grid hacked, shutting down message on screen, electricity meter. Futuristic electricity meter device
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
golden facial cream mask with a brush, jade roller and silicone beauty mask on pink background
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Protection concept of digital and technological. Protect mechani
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Faceless thief or hacker stealing login password, money, email, privat messages and credit cards using virus. Flat criminal illustration of hacker coding bug to hack data. Internet security of thief
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Full body elderly woman 50s year old wear shirt big huge blank screen mobile cell phone smartphone with area point index finger up isolated on plain pastel light blue color background studio portrait
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Skincare concept. Top view photo of rose quartz roller and eucalyptus on white marble background with copyspace
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Closeup person's hands pruning Jade houseplant with garden shears
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
konie Arabskie, Arabian horses in dynamics
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Unsecure and buggy programming code filled with errors and strange logic. Code contains insecure queries, broken validation, weird functions, and programming flaws for demonstration. Latch
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Hand touch with virtual screen. cyber security concept, Login, User, identification information security and encryption, secure Internet access, cybersecurity,
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Succulent mix with cactus, crassula and haworthia.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Green face roller and gua sha massager made from natural jade nephritis stone isolated on white background.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Abstract digital background with binary code. Hackers, darknet, virtual reality and science fiction.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Natural jade mineral gem stone beads isolated on white background.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Glitched silhouette, bitmap effect, error signal, technical problem. Hacked system or cyber attack. Vector illustration.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
System hacked, computer warning sign. Random letters, signs, computer code, bits and bytes. System message, cyber attack, threat, network security, virus, computer crime. 3D illustration
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
malware detection , virus monitoring , security assessment
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
E-mail phishing attack concept. Digital online cyberattack with fraudulent scam emails that contain web links to malicious websites. Malware scam isolated on white background vector illustration
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Coding background, Application development and code programming. Technology business computers concept
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Creative glowing big data glitch background. Unique Design Abstract Digital Pixel Noise Glitch Error Video Damage. 3D Rendering.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
seamless pattern with abstract flowers
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Natural wellness and anti aging skin care with beauty jade roller, gua sha , bath salt and eucalyptus branch on marble background. Spa, face massage, relaxation concept. Top view, flat lay
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Open red padlock on steel chains, mock up
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Closeup of Blooming White Champaca Flower In Sunlight
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
3D Conceptual Illustration of Cyber Attack Alert
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Hand typing on laptop keyboard, green numbers on display. Hacker forcing the system. Programmer writes the code. Technology communication, informatics, security protection, hacker, cyber crime concept
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Processing of jade. Industrial jewelry manufacturing. Sacred stone of China
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Skin care concept with face rollers on light gray background
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
AI strengthens cyber security with artificial intelligence threat detection, AI-based protection layers, and virtual assistant alerts against breaches. Kernel
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Hacker attack landing page template. Internet piracy technologies, cybercrime concept. Hacker sits in front of monitors.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
bitcoin wallet hacked message on smart phone screen. cryptocurrency theft concept
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Baishui river at Jade Dragon Snow Mountain
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
life hacks word written on wood block. life hacks text on table, concept
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Hacker working with computer in dark room with digital interface around. Image with glitch effect.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Glitch noise static television VFX. Visual video effects stripes background, CRT tv screen no signal glitch effect
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Cyber attack in process with hacker
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Binary code on flag of South Africa. Program source code or Hacker concept on South African flag. South Africa digital technology security, hacking or programming
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Abstrct lines purple vertical with light effect on dark background.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Jade Plant flowers (Crassula ovata)
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Cybersecurity internet and networking concept. Close up of hand holding smartphone information security and encryption, secure access to user's personal information, secure Internet access.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Young woman looking into the mirror and using jade face roller at home
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
hacked glitch neon editable text effect
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
digital background, a information on a popup, system hacked 3d-illustration
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Natural pink marble onyx, High resolution texture background, polished slab
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
A business professional engages with multiple email notifications and alerts, highlighting the importance of swift communication and security in a contemporary office scenario. Gantry
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
broken security lock on computer keyboard with hacked symbol
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Natural jade face roller and ice cubes on grey background, closeup
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Jade facial roller on pink background with copy space
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Young fun woman 20s in casual clothes hold in hand makizushi sushi roll served on black plate traditional japanese food holding index finger up great new idea isolated on plain pastel pink background
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
men using smartphones warning alert, email hack SMS spam, fake text message phishing.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Cyber crime and internet privacy hacking. Network security, Cyber attack, Computer Virus, Ransomware and Malware Concept.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
cyber concept infographic design template. included biometric recognition, theft, hack, biometric identification, spyware, crime icons
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Text sign showing Productivity Hacks. Conceptual photo Hacking Solution Method Tips Efficiency Productivity Blackboard with white letter pink base much green paper lobs big white lob
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Hacker with folded arms and abstract glowing human brain hologram on blurry background. Neurology research, hacking, data theft and artificial intelligence concept.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
China flag - 3D realistic waving flag on matrix digital background with binary code
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
top view of person hands close cover or block the laptop webcam, being afraid of spy hack the camera
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Ethical Hacking word cloud conceptual design isolated on white background.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
abstract background, fake stone texture, blue green malachite jasper agate or marble slab with veins, wavy lines fashion print, painted artificial marbled surface, artistic marbling illustration
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Angry businessman shouting at his laptop
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
system hacked alert , hacker attack , cyber crime detection
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Warning alert icon with a hacked system. malicious software, virus, spyware, malware, or cyberattacks on computer networks. Security on the internet and online scam. Digital data is being compromised.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Unsecure and buggy programming code filled with errors and strange logic. Code contains insecure queries, broken validation, weird functions, and programming flaws for demonstration. Vouch
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Massage quartz roller for the face of natural nephritis with serum oil with monstera leaves on beige background.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Bonsai Portulacaria isolated on a white background. Portulacaria afra or Elephant Bush is a small-leaved succulent from South Africa. Bonsai tree
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Jade face massage roller and gua sha on pink background.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
macro photography of sample of natural mineral from geological collection - raw Teisky Jade (Hantigyrite, khakassian serpentine) rock from Magnetite, Serpentine, Hematite minerals isolated on white
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Shocked young business woman in white shirt posing isolated on grey background. Achievement career wealth business concept. Mock up copy space. Hold say cloud with lightbulb, put hand prop up on chin.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Jade vine, colourful of flower in the garden.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Life Hacks. Computer keyboard and a coffee mug on a white table
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
konie na wybiegu, jesienny poranek
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Hackathon - word from wooden blocks with letters, hackathon hack day, hackfest or codefest event concept, random letters around, white background
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Hacker using creative glowing big data interface.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
view form top of Jade Dragon Snow Mountain
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Computer System Hacked and virus screen.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Night, cybersecurity and hands typing with phone for texting, internet troll or person cyberbullying. Dark comment, social media netizen or keyboard warrior for smartphone, online bullying or hacking
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Phishing, Password Cracking on laptop screen concept illustration flat design vector eps10. simple and modern graphic element for landing page, app or web ui, icon, infographic
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Error Message with Browser interface. Website window mockup, internet screen frame, browser tab on Glitch noise static television.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Natural jade face roller and ice cubes on grey background, flat lay. Space for text
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Succulent houseplant Crassula in a pot on white background
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Woman controlling social media
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
AI secures systems using virtual assistant alerts, artificial intelligence protection tools, and proactive AI cybersecurity defense solutions. Kernel
Do ulubionych favorite_border
Usuń z ulubionych favorite