-
Young inexperienced developer in office requests help from team to fix hacking attempt on corporate network. Intern assisted by colleagues to investigate unauthorized access alerts, camera A
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Hand drawn set of house plant in a pot. Outline room plant collection. vector illustration
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Jade Plant in watercolor style, vector illustration, isolated on white background.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Cybersecurity defense and system protection from hackers, secure digital systems, cyberattack prevention, IT security solutions, and risk mitigation for safe digital operations. Muxer
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
PNG Geometric Tech Overlay with Transparent Background
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
PENETRATION TEST inscription, cyber security concept. 3d illustration
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Deep forest green paper background with a smooth matte texture and subtle geometric patterns..
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Digital binary code matrix background with digits moving across the screen. Data decoding and encoding algorithms in the digital age. Vector illustration.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Bright green waves radiate from center. Dark background creates dramatic contrast. Text reads background design. Modern, dynamic visual.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
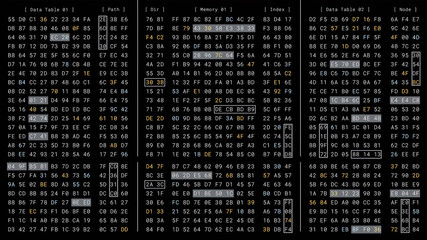
Computer binary matrix memory code encryption process in high security cloud server, cybersecurity data information programming technology software, digital hex number UI display interface monitor
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Cybersecurity shield, data encryption icons, cloud protection, and secure network interface. Concept of digital security and cyber defense technology.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Luxury skincare korean beauty products - creams, balm and mud mask jars with jade stone face roll massager - Facial roller massaging therapy.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Konie, konie na pastwisku konie na padoku, konie w górach
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Guasha face massage in beauty salon, massage technique for stimulating pressure points on the face, using jade stone roller
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Girl massaging her cheek with a jade roller
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Ransomware Malware Attack. Business Computer Hacked
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Variegated jade plant in the succulent garden
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Abstract virtual code skull hologram on modern architecture background, cybercrime and hacking concept. Multiexposure
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Business threat or problem, challenge or survive to win, survive and struggle to face business competition, defensive business woman using shield to face boxing glove with spring
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
The concept of credit card theft. Hackers with credit cards on laptops use these data for unauthorized shopping. Unauthorized payments from credit card owners. In the hacker's secret office
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
With a jade bracelet and ring young beautiful woman.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Cyber security hacker concept. Internet web hack technology. Blurred Hacker man hand isolated on black with flare ray flash effect. Data protection, secured internet access, cybersecurity.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Unsecure and buggy programming code filled with errors and strange logic. Code contains insecure queries, broken validation, weird functions, and programming flaws for demonstration. Vouch
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Happy millennial black woman making face massage with jade roller
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Network data security isometric vector illustration. Online server protection system concept with datacenter or blockchain. Secure bank transaction with password verification via internet.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Half-naked brunette woman smiling while showing jade roller
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Blank T Shirt color jade dome on invisible mannequin template front and back view on white background
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Protection network security computer and safe your data concept, Businessman holding shield protect icon. lock symbol, concept about security, cybersecurity and protection against dangers
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Digital piracy - skull in explosion of hacked data
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Hacker Solid Editable Icons set. Vector illustration in modern thin solid style of hacker icons: hacker, fraud, phishing, etc
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Konie, konie na pastwisku konie na padoku, konie w górach
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Guasha Face Lymph Drain Massage with Jade Stone Roller
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Light pink blurred background made of pink jade or Nephrite
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Portrait of relaxed young woman using jade roller for massaging her face, posing with eyes closed isolated over beige background
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Cambodia country map made from digital binary code
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Concept of cyber crime and cyber security. Hand using laptop and show malware screen with phishing email, hack password and personal data. hackers, Virus Trojans, Encription Spyware or Malware.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Jade Dragon Snow Mountain is surrounded by clouds and mist all year round. Blue Moon Valley is located at the foot of Jade Dragon Snow Mountain, a magical blue
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Transparent Background jade Illustration Png. Transparent Clipart Image of watercolor green crystal ready-to-use for site, article, print. Heart chakra stone, healing crystal
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Young woman using natural jade face roller on light blue background, space for text
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Hacker tablet cyber security. Digital mobile phone in hacker man hand isolated on black banner. Internet web hack technology. Data protection, secured internet access, cybersecurity.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Email security system identifies phishing attempts, detects suspicious messages, and protects users from data theft and malware through intelligent monitoring and alerts. Parse
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Infographic banner with jade roller facial massage exercise. Young black girl brunette face with massage directions.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Abstract technology background. Lines texture. Motion dots. Black backdrop. Futuristic wallpaper. Blue and violet color.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Half-naked black woman massaging face with jade roller
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Celadon ceramic dishes , Thai Celadon on white background
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
System hacked modern glitch concept 3d illustration
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
abstract background, fashion fake stone texture, green onyx jade agate or marble slab with wavy lines, painted artificial marbled surface, artistic marbling illustration
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
after boiled. soaked in ice water and cut the potato skin. make it easily pull the skin off, quick way to peel potatoes, kitchen hack
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Jade facial roller for anti-aging skin care massage, serum bottle and cream jar on white marble table.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Konie, konie na pastwisku konie na padoku, konie w górach
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Green jade Rare and expensive For making jewelry
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Beautiful woman massages her face using a green jade roller for elastic perfect skin, isolated on blue background with space for text. Facial jade roller
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
payment fraud via mobile application, fake money, financial theft landing page
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Back rear view photo of coder developing new security system to protect digital data base from being hacked using laptop as an additional work device
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Green and white stratified red stone patterned with natural jade marble stone texture nature layer background
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Gardener holding jade tree branch with roots for replanting
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
dark green marble texture use for background. luxury interior stone tile background. Statuario dark green marble background. emerald stone texture color.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
abstract green background. geometric arrow illustration for banner, digital printing, postcards or wallpaper concept design.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Beautiful dark green viridian vintage color trends feather texture background
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Unsecure and buggy programming code filled with errors and strange logic. Code contains insecure queries, broken validation, weird functions, and programming flaws for demonstration. Latch
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Portrait of incognito hacker using computer for organizing massive data breach attack on corporate servers. Secret location surrounded by displays, servers and cables.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
jade coin three dimension
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Chinese Jade Princess in an Asian Classical Garden
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
abstract green marble surface texture background
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Spa composition of green jade Gua sha and roller, white flower, small branch of green leaves on the white towel and green bamboo napkin. Freshness. Flat lay
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Macro stone garnet mineral, Uvarovite in rock on a white background
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Mobile banking login screen with red alert signs and network threat background. Concept for smartphone fraud, financial hacking, or identity theft risk.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Konie, konie na pastwisku konie na padoku, konie w górach
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Maori New Zealand Greenstone pounamu jade Koru (spiral fern) shape pendant on cross section of timber log
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Islandia interior konie Landmannal
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
PENETRATION TEST inscription, cyber security concept.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Krajobraz naturalny, pastwisko i hodowla koni w Belgii.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Fluid Art. Liquid dark turquoise abstract drips and wave. Marble effect background or texture
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Code Injection Hacks in Web Applications. Code-injection attacks manipulate specific system variables. opportunity for hackers to access sensitive information. 3D render
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Beautiful red jade gemstone on white background
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Abstract computer code background
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Dwa konie na polanie we mgle
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
White criminal anonymous mask calling to credit card owner to threaten ransom with privacy information all database, making password encryption by programming hack trying to make insecure. Pecuniary.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Banner pattern made of jade gua sha facial roller on pastel green background. Facial massage kit for lifting massage therapy made from natural stones, personal skin care anti-aging tools
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Haking into crypto world . Mixed media
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Green marble pattern texture abstract background / texture surface of marble stone from nature / can be used for background or wallpaper / Closeup surface marble stone wall texture b
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Unamused face three-dimensional emoji. Dissatisfied emoticon isolated on transparent background. 3D rendering
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Green background white marble wall surface gray background pattern graphic abstract light elegant white for do floor plan ceramic counter texture tile silver background.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Watercolor hand-drawn illustration of strongylodon macrobotrys or green jade flower on white background
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
3d editable text effect hacked theme premium vector
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Jade vine or Emerald vine flower blooming. Strongylodon macrobotrys. The turquoise flowers of strongylodon macrobotrys, also known as jade vine, emerald or turquoise jade vine, lying on the ground
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Certified Ethical Hacker - CEH - icon set & web header banner
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Polished green jade gemstone sphere
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Green Jade marble stone texture, different shades of green jade tiles from Mahamuni Buddha Temple in Mandalay, Myanmar
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Computer programmers or hackers use usb to get information from their laptops to hack the corporate secret.
Do ulubionych favorite_border
Usuń z ulubionych favorite