-
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Tea Bag Aroma Life Hack For Smelly Shoes
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
stop theft. thief inside stop icon. business metaphor for stop cyber criminal movement vector illustration
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
HACK - Glowing Neon Sign on stonework wall - 3D rendered royalty free stock illustration. Can be used for online banner ads and direct mailers..
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Computer Hacker in Hoodie. Obscured Dark Face. Concept of Hacker Attack, Virus Infected Software, Dark Web and Cyber Security.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Stadnina koni / Kaszuby / pomorskie / Polska
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Hacker security cyber attack smartphone. Digital mobile phone isolated on black. Internet web hack technology. Login and password, cybersecurity banner concept.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Privacy concept: Cctv Camera on digital background
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Online banking alert system provides fraud protection and warning for phishing attacks, virus threats, bug detection, password security, and hacking risk shielding account datum
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Banner of data breach web vector illustration concept with icons of computer, security, attack, hacker, algorithm, access, digital, confidence
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
green marble stone texture background material part-1.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Hands operating a laptop with a vigilant eye on a hacker's silhouette in the background, illustrating the battle against cyberattacks. Hacker Defense
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Green emerald marble seamless glitter texture background, counter top view of tile stone floor in natural pattern.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Macro stone Nephrite mineral on white background
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Abstract blue background from jade surface.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Attention Danger Hacking. Symbol on Map Dark Blue Background. Security protection, Malware, Hack Attack, Data Breach Concept. System hacked error, Attacker alert sign computer virus. Ransomware.Vector
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
3d rendered illustration of Digital Computer station v2. High quality 3d illustration
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Life Hacks Green Blue Horizontal
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Jade dragon snow mountain,
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Beautiful dark green viridian vintage color trends feather texture background
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Medical Hospital Malware Ransom Extortion Breach
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
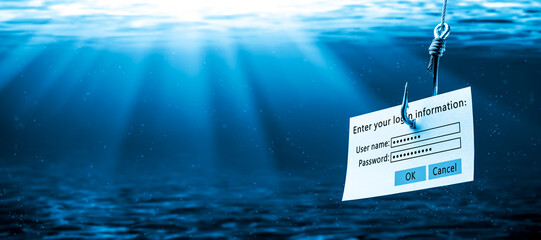
Login Information Attached To Large Hook Under Water With Sunlight - Phishing Concept
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Mint, grey, and gold stone marble texture. Alcohol ink technique abstract vector background. Modern paint in natural colors with glitter. Template for banner, poster design. Fluid art painting
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Jade Plant with Dense Succulent Green Leaves in Hanging Basket
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Computer Hacker in Hoodie. Obscured Dark Face. Concept of Hacker Attack, Virus Infected Software, Dark Web and Cyber Security.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Green white marble wall surface gray pattern graphic abstract light elegant for do floor plan ceramic counter texture tile silver background.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Jade Editable Vector Text Effect.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Hacking hunting for crypto currency
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Set of hacker and cyber criminal stealing confidential data with laptop computer illustration concept
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
greenstone industrial jewelery
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Creative code skull sketch and hands typing on computer keyboard on background, theft of personal data and malware concept. Multiexposure
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
China digital technology flag
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Self made moisturizer and green jade face roller and essential oil on marble cutting board on stone off white table. Facial massage. Green plant is Cylindric Sedge or Cyperus retrorsus. spikelet.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Beautiful Crassula ovata, Jade Plant,Money Plant, succulent plant in a modern flower pot on a white table on a light background. Home decor and gardening concept. Selective focus.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Surprised woman points finger up as she finds amazing idea online. Happy lady in curlers and face mask sitting on sofa, browsing Internet blog on laptop and learning good life hacks and practical tips
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Landscape View of Yushan Main Peak And Tongpu Valley From the North Peak of Jade Mountain At Sunrise, Yushan National Park, Chiayi Taiwan
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Life Hacks Blue Lines Blob Rounded Square Black Background Text
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
skull in the digital matrix on the BCD stream on the screen. computer matrix numbers.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Green jade goden pothos plant and white clock
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Plastic bank credit cards and fishhook on computer keyboard
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Abstract glitch effect background. digital art. pixel glitch texture. Data visualization concept. digital distortion and noise effect. banner or poster. Vector Illustration.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Hacking concept. Attention warning attacker alert sign malware red background. Vector illustration
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
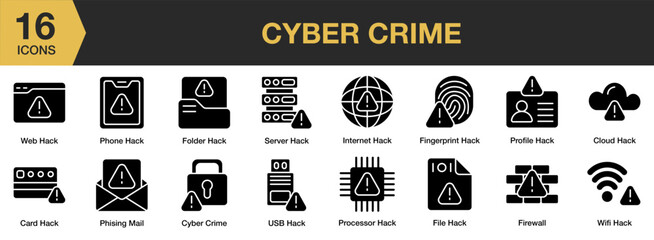
Cyber Crime solid icon set. Includes web hack, server, profile, wifi, processor, internet, and More. Solid icons vector collection.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
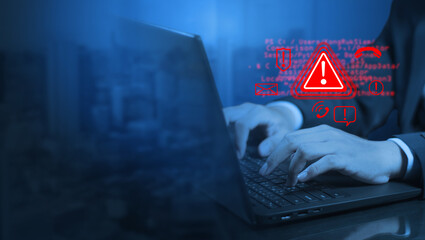
System hacked warnings alert Cyber attacks on a computer network, viruses, Spyware, Malware, or Malicious software. Cyber security and cybercrime concept. Compromised information Internet.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
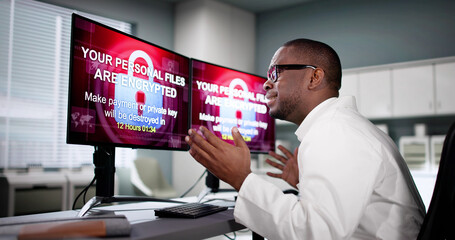
Ransomware Malware Attack And Breach
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Surface of jade stone background or texture.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Jade stone green gemstone with shape of egg, semiprecious jewelry chinese souvenir related to massage and fortune
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Virus and scam theme with hand pressing tablet computer screen
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Face massage. Smiling woman using jade roller for skin care
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Fingerprint scanning concept
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Fluid Art. Liquid Velvet Jade green abstract drips and wave. Marble effect background or texture
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Illustration of a jade magatama
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Facial jade roller icon in silhouette. Skin care and relaxation massage. Anti aging tool pictogram for web, mobile, decoration, logo template. Isolated vector illustration in trendy graphic style
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Life hacks - gears concept - 3D illustration
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Cyber crime and intellectual property rights concept. Abstract low poly style. Vector illustration.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Woman hand holding facial jade massage roller or gua sha over the white background.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Communication and phishing concept
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
jade flower progressing to bonsai
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Crassula plant in the pot on wooden background
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Abstract binary code background. Artificial intelligence, big data and digital technology concept. 3D render illustration.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
A criminal man thief holding folder data to running away from open door on scren laptop. Laptop hacker, cyber attack, online ransomware or malware to stealing personal data.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Scenic view of Blue Moon Valley and Jade Dragon Snow Mountain in Lijiang, China
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
hacked glitch neon editable text effect
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Black dark emerald jade green abstract luxury background. Silk satin fabric. Gradient ombre color. Curtain drapery fold line. Shiny glow glitter light. Design. Wide banner. Panoramic.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Jade Dragon Snow Mountain is surrounded by clouds and mist all year round. Blue Moon Valley is located at the foot of Jade Dragon Snow Mountain, a magical blue
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
thick, fleshy green leaves and reddish stem of Portucalaria Affra, an easy to care succulent plant, also known as elephant bush or dwarf jade.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Information privacy. Vector illustration. Information privacy is metaphorical key unlocks protection and safety personal data Safeguarding access to sensitive information is crucial for maintaining
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Chinese name stamp jade carved block craftsmanship
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Beige abstract poster with light spot. Gradient mesh grid background. Green banner. Vector illustration
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
jade bracelet on white background
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Young woman using jade roller at home
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Bug in computer icon, error, bug or scam detected, thread, malware scan, Malware on computer display, Virus computer bug icon, Simple design
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
jade vine rarest plant in the world
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Illustration concept of data stealing from the computer.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
A woman applies a jade roller to her face, showcasing a glowing, healthy complexion.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
2d illustration cyber crime and internet privacy hacking.Network security,cyber attack,computer virus,ransomware and malware concept
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Hacker using network interface in city
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Binary code background. Falling, streaming binary code background. Digital technology wallpaper
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Web browser window with virus detection alert on laptop screen. Internet threat warning. Concept of malware, ransomware, hacking, or cybercrime. Dangerous website. Flat technology vector illustration.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
piękne konie na łące, pastwisko i ogrodzenie
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Binary code on flag of South Africa. Program source code or Hacker concept on South African flag. South Africa digital technology security, hacking or programming
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Jade market in Hong Kong 香港の翡翠市場
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Golden Bitcoin floating above of hacker's hand in dark background. Finance, business, e-commerce or cyber crime concept
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Digital blue background. Information code. Binary computer code. 3d rendering
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
A stream of binary matrix code on the screen. numbers of the computer matrix.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
POV - horse carriage ride through golden field. View from horse carriage. Summer view at sunset
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Hacker with fake facial biometrics wants to commit fraudulent actions for log into protected system. Hacker uses false identity to hack identification system and gain access confidential information
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Beautiful woman with jade massage roller. Vector line art
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
jade gemstone mineral on collection
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Big Data 3D Cube. Quantum Computer CPU Core Virus Concept Background. Red Cube Inside Blue Block. 3D Blockchain Cube Blocks Concept. Data Sorting. Artificial Intelligence HUD Design Element.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
A blue pixel background with a glowing square pattern. The abstract illustration has a digital mosaic texture, creating a modern tech effect.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Top view photo of eucalyptus rose quartz roller and gua sha on isolated white background with copyspace
Do ulubionych favorite_border
Usuń z ulubionych favorite