-
Digital locker icon in a Server room data center - 3d rendering
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
You have been hacked! Text inscription in a distorted glitch style on a black background. Vector illustration.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Chinese jade bracelet features
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
jade gemstone mineral on collection
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Hacker with fake facial biometrics wants to commit fraudulent actions for log into protected system. Hacker uses false identity to hack identification system and gain access confidential information
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Hacking Detected. Concept meaning activities that seek to compromise affairs are exposed Entering New Programming Codes. 3d illustration
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
The Jade Emperor statue in Hat Yai, Thailand
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
healthy green crassula ovata succulent jade plant lucky money tree indoor on window-sill
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Surface of jade stone background or texture.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Mountain background vector. Minimal landscape art with gold line art texture. Abstract art wallpaper for prints, Art Decor, wall art and canvas prints.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Computer hacker hood touches touchscreen with lock symbol and binary code. Light waves on abstract binary background hacker silhouette. Hacking computer system, database server, data theft, vector
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Jade tree or Crassula ovata, a very easy succulent to grow
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
X Danger Symbol on Dark Red Glitched Background. Computer Virus. System Hacked Error Sign. Malware, Ransomware, Data Breach Concept. Vector Illustration.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
AI powered System hacked alert after cyber attack on computer network compromised information concept. hand using latop computer internet virus cyber security and cybercrim.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Face jade roller, gua sha, eucalyptus branches on stone surface. Flat lay, top view, overhead.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Ancient mayan jade necklace
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Green blue abstract background. Toned mountain texture. Close-up. Marble pattern effect. A combination of jade color and rough rock texture. Green stone background.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
źrebak konia arabskiego z klaczą
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Web banner with phrase Hack The Password. Concept of phishing, invasion of privacy, hacking, malware or cyber crime
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Face cleanser, serum bottle, essential oil and jade facial roller on light blue background with hard shadows, top view. Flat lay, copy space
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
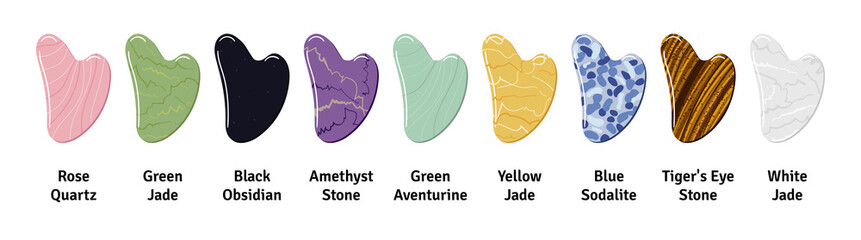
Big set of different gua sha stones with title are made of quartz, aventurine, jade, amethyst, sodalite. Facial gua sha massage tools, Chinese skin care. Hand drawn vector illustration.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Necklace made from natural green onyx stone, agate (layered chalcedony), gray-blue Labrador beads stone and jade beads on an old brown linen cloth. Onyx stone is powerful energy talisman.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Jade : Beautiful green jade bracelet isolated on white background
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Automobile hack computer program.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Shocked young man looking at smartphone
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Face lift anti-aging treatment with jade roller. Woman with perfect skin of her face after massage.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Data phishing hacking online. Scam envelope concept. Computer data fishing hack crime
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Stones for massage and recovery of health. Yellow jade on the massage table column.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
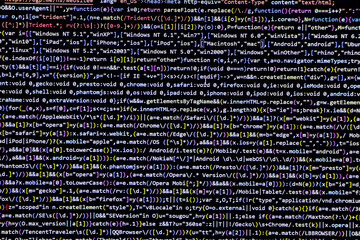
Unsecure and buggy programming code filled with errors and strange logic. Code contains insecure queries, broken validation, weird functions, and programming flaws for demonstration. Latch
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Programming coding screen, web developer coding screen
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Top view of a caucasian woman getting massage with jade face roller in spa salon. Freckled face. Cosmetology, body and skin care. Vacuum roller massage
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Big Data 3D Cube. Quantum Computer CPU Core Virus Concept Background. Red Cube Inside Blue Block. 3D Blockchain Cube Blocks Concept. Data Sorting. Artificial Intelligence HUD Design Element.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
3d Cyber security concept. Personal data protection, encryption technology, access code to cloud storage Cloud technology on digital circuit board. Vector illustration
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Technology concept is attacked, computer cybersecurity defense system is hacked or destroyed. Interfering internet network. The unlocked red padlock stands out in the center of a small binary polygon.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Abstract dark background. Bright box. Shine square. Sci fi shape. Light golden geometry. Smart code. Energy effect. Big data. Vivid streak. Vibrant strings. Digital chip. Glare grid lines. Cubes
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
A gold ring embellished with green jade lay on the ground.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Surface of jade stone background or texture.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Pixel glitch effect background - colorful distorted digital noise, random horizontal lines, strips, blocks. Retro futuristic design, abstract glitched texture for web pages. Neon colors on dark.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Binary Code backgrounds, a sequence of zero and one, blue numbers, on a black background. Numbers of the computer matrix. The concept of coding and cybersecurity
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Guasha stone line icon set, face massage concept, soft skin health products vector icons, facial jade stone roller, oil, creme emblems, anti-aging gua sha tool symbols isolated on white background
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Haking into crypto world . Mixed media
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
A computer programmer or hacker prints a code on a laptop keyboard to break into a secret organization system.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Self made moisturizer and green jade face roller with pieces of ice. Exotic fern leaves and water drops on off white background. Monochromatic white green look. Facial massage, handmade cosmetics.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Virus bot robot hacker. Network piracy danger. Errors on monitor screen. Pirate attack artificial intelligence concept
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
System failure security fail computer breakdown hacking warning message hacked alert. Cyber attack network fail. Digital illustration.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Glitch noise static television VFX. Visual video effects stripes background, CRT tv screen no signal glitch effect
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Software source code. Programming code. Programming code on computer screen. Developer working on program codes in office. Source code
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Abstract digital cloud skull on blue background. Cloud computing, hacking and data theft concept. 3D Rendering.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Neo Mint Gradient Waves Vector Background. 2020 Color Trend Forecast. Minimal Cover Design Concept. Wavy Stripes Pattern. Pastel Green Abstract Texture.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Cyber attack with skull symbol alert on screen
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Isometric vector of a hooked login form pulled from an open yellow envelope by a fishhook, symbolizing hacker credential theft and deceptive phishing email. Phishing attack
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Glitched silhouette with binary code. Danger internet virus, technical problem or system error. Vector illustration.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Protecting information in mobile devices. Hacking mobile devices by hackers. Data protection in the cloud.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Mother Arguing With Teenage Daughter Over Use Of Mobile Phone
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Cybersecurity cybercrime internet scam, online business secure payment, Cyber security platform VPN computer privacy protection data hacking malware virus attack defense, network system hacked warning
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Blue green rock texture. Toned cracked crumbled rough mountain surface. Close-up. Dark teal color. Colorful background for design. Fantasy, fantastic, mystic.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Phishing concept background, Phishing email, Data Breach, Theft, Steal. Data Hacking Background
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Jade Buddha Temple, Shanghai, China
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Creative shot of trendy pink jade roller.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Close up on a RJ45 panel in a computer data center
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Luxury marbling background vector. Emerald green marble design with golden texture.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Hacker Attack Concept Icon Set 3d Isometric View. Vector
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Modern glitch transition with hacked and skull
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Active and mobile lifestyle, sports as hobby and way of life. Guy sports club visitor exercises on hack squat machine. Client performs exercises, combines dynamic and static loads on body.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Gua Sha massager isolated from background, green jade stone for face and body care.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
System hacked alert after cyber attack on computer network. user is using computer with triangle caution warning sign for notification error. cyber crime, cyber security, Ransomware, Phishing, Spyware
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
green nephrite ball on black background
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Cyberattack trolling and broadcast on screen 3d illustration
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Abstact grunge sci-fi background with geometic pixelated figures and patterns.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Perplexed tele workers watching media in the night
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
emeralds and gemstone jade
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Closeup old green jade leo statue for good fortune in front of door in the temple of thailand isolated on white background with clipping path
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Hand painted watercolor background. Black blue green modern abstract art background. Dark turquoise aquarelle background with copy space for design. Web banner.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Jade face roller. Spa concept
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Woman Protecting Her Business From Cyber Security Breach
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Suspicious Email Link Detected, Cybersecurity Warning, digital warning interface, phishing email and a suspicious link detection alert. Concept for cybersecurity, email threats, phishing prevention
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Green gua sha tools for facial acupuncture massage.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
abstract lines with dots over dark background.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Hacker Head Logo Vector Template Illustration Design. Mascot Hacker Logo design
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
jade text effect design vector
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Bitcoin cryptocurrency theft concept with a silhouette of a thief sneaking towards a coin on a dark digital background. Vector EPS10.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Young excited handsome man in casual clothes posing isolated on blue wall background, studio portrait. People lifestyle concept. Mock up copy space. Holding index finger up with great new idea.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Close up photo of disappointed youth collar employee have fear horrible novelty have sacked touch head hands palms scream wear checkered shirt plaid light room
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
User Man Vector Icon Glitch
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
White Water River waterfall and Jade Dragon Snow Mountain, Lijia
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Abstract Red Background with Binary Code. Malware, or Hack Attack Concept
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
2d illustration abstract binary skull
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Beautiful african woman smiling and massaging face skin with jade roller isolated on yellow
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
gift box with rose quartz jade roller and stone on pastel pink background with festive lights
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
jade vine (Strongylodon macrobotrys)
Do ulubionych favorite_border
Usuń z ulubionych favorite