-
Blue Moon Valley showing waterfall, clear blue lake and stunning mountain backdrop of Jade Dragon Snow Mountain, Lijiang, China
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Jade Emperor Pagoda, a Buddhist temple in District 1, Ho Chi Minh City, Vietnam
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Fraud icons. Abstract digital hacker icon set in futuristic glowing dots style. Skull, bag, unlock, data server, broken shield, and bank card with red glitch dangerous particles. Vector illustration.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Innovation, network, technology, security, information, privacy, internet, software, neural, system, secure. The world innovation technology on up hand. information privacy and neural system.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Cosmetic skin care products, jade stone face massager, creams, gel and oil. Roller massage of the face. Flat lay, top view
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Grunge HACKED round stamp seals isolated on a white background. Round seals with grunge texture in red and blue colors. Vector rubber overlay of HACKED label inside circle form with stripes.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Skin care tools background.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Night, cybersecurity and hands typing with phone for texting, internet troll or person cyberbullying. Dark comment, social media netizen or keyboard warrior for smartphone, online bullying or hacking
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Businessman using laptop with electronic email hacking and spam warning symbol. cyber attack network, virus, spyware, Cyber security and cybercrime.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Houseplant Crassula jade plant money tree in white pot in home - home gardening concept
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
3D rendering. Abstract background concept of cyber security and attack, system crash.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Vector set of realistic isolated red rubber stamp of Hacked logo for template decoration on the transparent background.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Woman wearing round jade necklace around her neck
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Money Heist Of Digital Bank Account
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Sunrise Glow on Jade Dragon Snow Mountain over Lijiang Old Town, Yunnan, China.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Rough natural green tone color paint on blank eco environmental friendly cardboard box paper texture background with space minimal style
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Abstract digital cloud skull on blue background. Cloud computing, hacking and data theft concept. 3D Rendering.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
collection of various Jade natural mineral gem stones and samples of rock isolated on white background
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Girl hacker in a hoodie using a laptop. Abstract digital polygonal hack woman in blue on technology dark background. Cybersecurity or cyber attack concept. Computer scam. Low poly vector illustration
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Hooded cybercriminal uses laptop to hack internet in cyberspace, black background, internet personal data security concept. Hacker on a black background with space for text
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Abstract Elegant dark green background with mottled vintage texture in old fancy background design, texture of colored parchment paper.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Presentation background vector design Banner background design with circle, arrow, square, stroke Dotted pattern background with jade colour
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Wanted Hacker is Coding Virus Ransomware Using Abstract Binary Code. Cyberattack, System Breaking and Malware Concept.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Glitching computer screen, glitch programming code. Virtual environment, programm function failure and data loss, critical code mistake, hacker attack or hardware malfunction concept vector background
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Hacker on the phone screen with a folder infected with a Trojan. From the folder, connections go to the messenger application which are hacked and taken over. Flat design vector illustartion.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Horse Hunter Jumper equestrian rider riding flat trot hack
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Abstract Technology Machine Code Background. Random Binary Hexadecimal Code. Matrix with Digits. Vector Illustration. Hacking, Cryptography, Malware, Reverse Engineering.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Data breach banner web icon vector illustration concept with icon of computer, security, attack, hacker, algorithm, access, digital and confidence
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Cyber crime and internet privacy hacking. Network security, Cyber attack, Computer Virus, Ransomware and Malware Concept. 3d illustration
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
jade jewelry, jade stone, jade, green jade, gemstone, leaves, water, white, nature, green
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
A golden buddha at Shanghai's Jade Buddha Temple
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Krajobraz wiejski Podlasia. Konie na łące, Podlasie, Polska
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
cyber security concept, Login, User, identification information security and encryption, secure Internet access, cybersecurity, secure access to user's personal information
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Rose Quartz jade roller and Gua Sha massager on white towel. Massage tool for facial skin care, SPA beauty treatment concept
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Rose quartz facial massage roller with essential oil on monstera leaf. Face massage tool, anti-aging, anti-wrinkle beauty skin care concept. Flat lay, top view
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Futuristic Glitch background. Abstract pixel noise glitch error video damage like Vhs glitch. Pattern for wallpaper design. Screen error effect. Abstract background. Medical background. Cosmic
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Hand holding a saw with a black handle isolated on white background
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Hacker in mask hacking computer system password, breaking into online server, anonymous attacking database. Cybercrime, woman hacker stealing information portrait at night time
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Galop, wyspa Olchon, jezioro Bajkał, Syberia, Rosja
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Open source intelligence. OSINT. Open data access. Open source analysis. Cyber analytics. Data gathering. Wireframe hand places an element into a composition visualizing OSINT. Vector illustration.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
rose quartz facial roller and massage stone gua sha isolated on white background, flat lay
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Frustrated Businesswoman Looking At Her Computer Screen
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Anonymous hacker and face mask with smartphone in hand. Man in black hood shirt trying to hack personal data from mobile phone. Represent cyber crime data hacking or personal data stealing concept.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Young sly man trying to breach the system while giving bad commands on laptop in empty dark office
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Concept of hacker attack, fraud investigation, internet phishing attack, evil win, personal privacy data, hacking and stealing email and money with tiny people. Vector illustration in flat design
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Silhouette Of Hooded Criminal Hacking Computer On Binary Code Background - Cyber Crime Concept
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
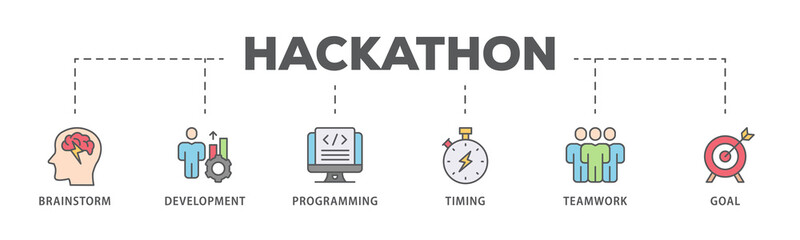
Hackathon banner web icon illustration concept for design sprint-like social coding event with icon of brainstorm, development, programming, timing, speed, teamwork, and goal
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
hacker attack , cyber threat risk management , malware and virus prevention , security awareness
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Illustration vector isolated of chinese gods, chinese mythology, jade emperor, sky god
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
hooded hacker solar winds hack concept
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Real jade That is the original jade ball Green and rare, expensive
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Vector isolated cartoon illustration of home potted succulent jade bonsai plant.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Email security system identifies phishing attempts, detects suspicious messages, and protects users from data theft and malware through intelligent monitoring and alerts. Parse
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Abstract Red Binary Software Programming Code Background. Malicious Hack Malware Ransomware Concept. Data Leak Breach. Random Binary Data Matrix Wide Vector Illustration.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Imperial green jadeite jade Guan Yin (Avalokitesvara) and Smiling Buddha pendant. Beautiful Chinese style Burmese jadeite jade jewelry
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Hacker doing illegal activities in secret underground base, uploading USB flash drive containing data obtained from victim after tricking it into installing ransomware program, camera B
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Laptop Bug solid glyph icon
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Cyber security destroyed. Padlock red opens on code connection dark red background.Cyber attack and Information leak concept.Vector illustration.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Young male hacker in hat and glasses using computers to hack nuclear warhead and start war while sitting at table in dark room
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Life hack written on tablet in office as flatlay
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
hacker at work with graphic user interface around
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Skin care beauty concept with face roller on green background
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Man doing machine hack squat exercise. Flat vector illustration isolated on white background
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Abstract virtual binary code illustration on flag of China and blurry skyscrapers background. Big data and coding concept. Multiexposure
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
you have been hacked. Vector hacker icon or pictogram. Keylogger, cyber security concept. Technology data. Hybrid, and warfare, DDoS attack. Cyber war. Hackers, criminals. login and password. Digital
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Jade roller and gua sha stone massager at pastel background. Anti-aging therapy. Top view.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Gua Sha massager and jade roller over brown paper on green background. green jade stone for face and body care. top view.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Ethical Hacking icon set. Includes symbols for hacker, fraud, security, crime, hack, cyber and more. Hacking linear icon. Icons for UI design. Outline and solid pictogram.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Ransomware Cyber Attack Showing Personal Files Encrypted
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Cybersecurity internet and networking concept. Close up of hand holding smartphone information security and encryption, secure access to user's personal information, secure Internet access.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Cybersecurity cybercrime internet scam business, Cyber security platform privacy protection 3D AI robot safety icon, computer virus attack defense, identity privacy data hacking protection firewall
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Cables plugged into a box
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Jade : Green jade (jadite) scupture in cubbage shaped, symbol of wealthy, rich, treasure and lucky in Chinese traditional culture. Jade isolated on white background.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Technicians in AI server hub panicked by hacking attempt stealing sensitive company data. Team of data center IT experts fighting computer virus triggered by security systems, camera A
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Cybersecurity protects digital systems from hackers with IT security, attack prevention, and risk management for safe online operations. Latch
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Green marble stone surface. Luxury jade texture for product display.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Cute Colorful Typography Lettering productivity hacks
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Young insighted smart proactive woman of African American ethnicity she wear blue shirt casual clothes holding index finger up with great new idea isolated on plain pink background. Lifestyle concept.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Uncooked Jade Rice in a Measuring Cup
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Cyber background constructed with different symbols. Digital futuristic backdrop. Abstract visualization of programming. Vector illustration.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Smiling senior woman massaging her face with a jade roller while looking in the mirror
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Green Burmese Imperial Jade Ring. And art background
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Zaprzęgi konne na drodze do Morskiego Oka w Tatrach,
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Woman holding semiprecious stones in her hands on dark grey background
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Pretty woman massaging face with jade roller and looking at round cosmetic mirror in bathroom
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Smartphone security tips linear icons set. Prevention from hacking attack. Security. Customizable thin line symbols. Isolated vector outline illustrations. Editable stroke. Quicksand-Light font used
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
skull in the digital matrix on the BCD stream on the screen. computer matrix numbers.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Blue moon valley in lijiang city yunan , China
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Do ulubionych favorite_border
Usuń z ulubionych favorite