-
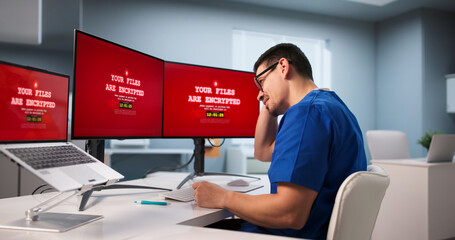
System hacked alert A computer whose system has been hacked due to a cyber attack on the computer network, therefore, an icon is displayed on the virtual screen.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Hand drawing green jade texture seamless pattern background
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
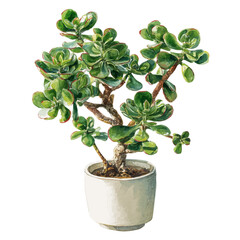
Crassula ovata, jade plant close-up. House plant in pot on the table by the window. Lush, fresh green leaves of houseplant. Succulent in home garden.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
System hacked alert after cyber attack on computer network. Cybersecurity vulnerability, data breach, illegal connection, compromised information concept. Malicious software, virus and cybercrime.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
abstract green marble surface texture background
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Steel hack saw in white male hand
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Remote communication, life hack media, automated online helper. Internet forum, how-to videos, chatbot voice-controlled virtual assistant metaphors. Vector isolated concept metaphor illustrations.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Abstract grunge jade green background with golden patina
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Hand writing the text: Life Hacks
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Pretty woman massaging face with jade roller and looking at round cosmetic mirror in bathroom
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Senior mid aged lady of 50s years old massaging face skin using natural stone trendy jade quartz rolling device for detox of perfect skin. Spa traditional technique skincare ads.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Celadon ceramic dishes , Thai Celadon on white background
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Attention Danger Hacking. Neon Symbol on Red Map Background. Security protection, Malware, Hack Attack, Data Breach Concept. System hacked error, Attacker alert sign computer virus. Ransomware. Vector
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Cyber security protects against breaches, hacks, and network attacks using strong infrastructure and proactive digital defense strategies. Latch
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Fitness girl preparing to do squats on the hack machine in the gym.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
word system hacked computer
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
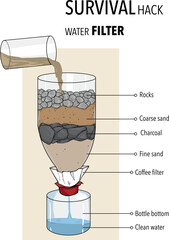
Survival hack water fılter vector illüstration
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
High-spirited lady with a jade roller looking forward
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Panoramic view of Saint Lucia
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Security icons set isolated on white background. Cybersecurity icons set for digital protection and data security concepts. A collection of flat design icons representing cybersecurity elements
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Digital binary code matrix background with digits moving across the screen. Data decoding and encoding algorithms in the digital age. Vector illustration.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
AI monitors network to issue real-time alerts for cybersecurity incidents. Alert warning showing red cyber for data breach, network threat, emphasis on security risk, caution, digital protection Vouch
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
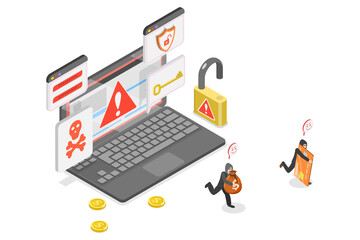
3D Isometric Flat Illustration of Cyber Crime, Hacker Attack, Online Criminals Stealing Computer Banking Information.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
The concept of credit card theft. Hackers with credit cards on laptops use these data for unauthorized shopping. Unauthorized payments from credit card owners. In the hacker's secret office
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Abstract background texture featuring swirling deep emerald green liquid flow design mimicking polished natural stone surface.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Abstract blue and pink technology background. Lines texture. Motion dots. Black backdrop. Futuristic wallpaper.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
A male hacker is using a computer to hack data to demand ransom from victims.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Dark teal paper texture background with emerald, jade geometric corners gradient layers, copy space for banner presentation
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Glitch background. Abstract screen with noise effect. Failure television and monitor. Technical problem computer. Digital hacking. Warning bug lost connect, disconnection, hack. 3D rendering.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
cyber security concept, Login, User, identification information security and encryption, secure Internet access, cybersecurity, secure access to user's personal information,
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Cybersecurity Icons Set Digital Protection Technology Concepts.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Female hand holding massage roller for the face with two heads of green jade stone. Beauty facial massage therapy, SPA self care concept.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Phishing scam, hacker crime attack and personal data security concept. Hacker stealing online credit card password on png background
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Anxious technicians in data center reacting to system lockdown caused by ransomware alert. IT professionals under pressure evaluating security breaches and scrambling to contain damage, camera A
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Luxury skincare korean beauty products - creams, balm and mud mask jars with jade stone face roll massager - Facial roller massaging therapy.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Digital glitch background. Screen interferences, broken pixels, cyberpunk hacker attack, computer error, noise, 80s television, error screen, digital banner, qualitative vector concept
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Guasha face massage in beauty salon, massage technique for stimulating pressure points on the face, using jade stone roller
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Girl hacker in the hood holding the phone in hands trying to hack the mobile device cloud in the dark under neon light
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Cybersecurity Glitch Lock and Shield Symbol on Dark Background Representing Data Protection, Firewall and Secure Access. System Under Hackers Attack. Ransomware Lock Vector Illustration.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Biohacking and healthy lifestyle concept, extended health surveillance and longevity programd. Biohacking for life extension.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Real jade Natural sparkling green color
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
horse Arab gallop stud dynamics
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Silhouette of a human head. Conceptual image of AI (artificial intelligence), VR (virtual reality), Deep Learning and Face recognition systems. Cyberpunk style vector illustration.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Collection of eight black icons depicting padlocks in various stages of being broken or unlocked, symbolizing security breaches or access.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Troubled Graphic Artist Battles Cyber Attack
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Cybersecurity Breach Vector. Broken Shield with Lock and Warning Icon.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Man accessing laptop with glowing cybersecurity login screen, warning icons and digital shields
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Red circle prohibition sign with hack text on black background no hack forbidden
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
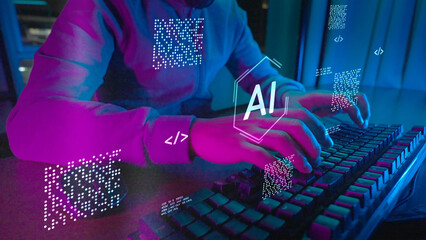
Computer coding prompt cyber security futuristic artificial intelligence in business finance, AI-powered analyze big data, showing charts and performance metrics for strategic planning.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Hand painted green watercolor background.Set of abstract green watercolor water splash on a white background,Ink paint brush stain. Green splatters spot. Watercolor pastel splash
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Succulent and Cactus Plant Illustration Set Featuring Aloe, Echeveria, Jade Plant, Hanging Succulents, and Decorative Potted Desert Plants for Botanical Design.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
breach icon set multi style various collection
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Cybersecurity threat, phishing email scam concept. Man hand on phone, data breach danger. Hacker attack, internet fraud, password stealing. Spam message, virus, security risk warning.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Server security icon set. Network protection concept. Vector illustration.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Little child with mobile phone is under cyber attack on internet. Anonymous hacker hacks into boy cellphone and steals data and passwords. Cyber crime,
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Hacker icon art in black and white
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Man receiving professional relaxing water head massage with jade mask
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Defense business related icons set. Including cybersecurity, shield, firewall, lock, encryption, antivirus, data protection, and prevention. Editable stroke. outline icons.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Modern Developer Programmer Screen with Computer Programming Language Code with Color Syntax Highlighting. Vector Illustration.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Dark Emerald Green Blurred Texture Abstract Background
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Anonymous man wearing black hoodie using smartphone indoors with his back to the camera, Phone Scammers, mysterious person typing message on mobile phone
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Horizontal scanlines glitch effect overlay, VHS screen lines, TV static interference pattern. Retro CRT monitor noise texture isolated on white. Motion blur speed stripes for video transition effects.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Hacker in hood try to unlock the key and fingerprint on computer and phishing folder. Phishing scam, hacker crime attack, personal data security, stealing password and cyber security.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Hacked stamp sign red rectangle grunge style
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Hospital's Cybersecurity Breached By Malicious Cyber Attack
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Phishing Email Icon with Skull, Cyber Attack and Online Scam Warning Illustration
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Lijiang snow mountain Jade Dragon in Yunnan China.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Concept of cyber crime and cyber security. Hand using laptop and show malware screen with phishing email, hack password and personal data. hackers, Virus Trojans, Encription Spyware or Malware.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Cybersecurity icons: Radar, bug, shield, lock, server, warning
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Healthcare data protection background, clean hex surface with red PHI warnings. HIPAA training, EHR access control. Medical IT backgrounds for hospitals. Vector illustration.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Refreshing lime green and light jade create a beautiful polygonal gradient surface
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Colorful VHS Glitch Screen Effect. Abstract Technology Vector Background in Retro Style
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Succulent and Cactus Houseplant Illustration Set Featuring Aloe, Echeveria, Jade Plant, Snake Plant, and Decorative Potted Desert Plants.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Silhouette jade plant bubble leaf silhouettes
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
data breach icon set collection in solid glyph dual color style. pack contain leak, hack, breach, malware, spyware, intrusion, phishing, ransomware, attack, theft icon
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
3D illustrastion - Data Matrix Warning Sign System Hacked
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Matrix code background with Japanese katakana symbols. Digital data stream with abstract green character patterns. Cyber security and programming abstract technology wallpaper concept.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Scam alert notification set icon. fraud notice alert. malware hack attack atention banner pop up. vector
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
thermal regulating jade roller silhouette vector illustration on transparent background
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
hacksaw tool icon silhouette vector art illustration
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Green jade roller massager for face on white marble.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
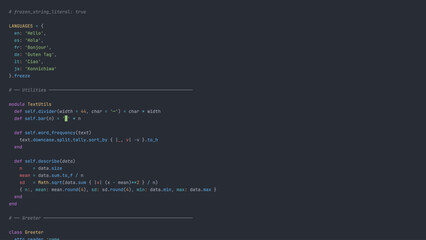
Unsecure and buggy programming code filled with errors and strange logic. Code contains insecure queries, broken validation, weird functions, and programming flaws for demonstration. Vouch
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Horizontal scanlines glitch effect overlay, VHS screen lines, TV static interference pattern. Retro CRT monitor noise texture isolated on white. Motion blur speed stripes for video transition effects.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Cyber crime awareness illustration, laptop security breach, malware alert, password hacking, digital threat icons, cartoon-style vector for online safety
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Ransomware Malware Cyber Attack
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Grunge aged life hack sign on wood
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Stara lampa w stadninie koni w Polsce
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Beautiful young african woman making face massage with jade roller
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Abstract texture of a deep green, cloudy background with stormy sky or turbulent cosmic nebula. Soft blending between darker forest green areas and lighter emerald or jade. Vivid, moody, atmosphere
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Cybersecurity cybercrime internet scam, online business secure payment, Cyber security platform VPN computer privacy protection data hacking malware virus attack defense, network system hacked warning
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Hand Holding a Smartphone with Multiple Glowing Red Alert and Warning Icons for Email Spam and Cyber Security Breach
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Futuristic green digital matrix space with binary code streams and glowing horizon line, symbolizing data transfer, cybersecurity, virtual networks, artificial intelligence vector background
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Cybersecurity Hacker technology and cyber threats with computers and digital globe in front, showing cyber theft, virus attacks and data extortion over a global high-speed internet network.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Credit card fraud and online banking hack concept showing hacker using laptop to stealing payment data.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Purple abstract pixel texture bg video screen. Tv pattern background with square noise effect. Futuristic broadcast neon gradient banner for television. Modern vhs led static display element
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
A person types on a laptop with a holographic interface showing a "SYSTEM HACKED" alert, symbolizing a cybersecurity breach, data theft, and AI technology risks in a modern office.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Jade Plant in watercolor style, vector illustration, isolated on white background.
Do ulubionych favorite_border
Usuń z ulubionych favorite
-
Traditional Mid Autumn Festival cakes and a golden color celebration
Do ulubionych favorite_border
Usuń z ulubionych favorite